SSH remote access device has become a cornerstone of modern network management, enabling users to securely connect to remote servers or devices from virtually anywhere in the world. With the growing demand for remote work and distributed teams, understanding SSH (Secure Shell) and its applications is more important than ever. Whether you're an IT professional, a developer, or a system administrator, this article will guide you through everything you need to know about SSH remote access devices.
In today's digital landscape, security is paramount. As cyber threats continue to evolve, organizations are increasingly relying on secure communication methods to protect their data and infrastructure. SSH remote access device offers a reliable solution by encrypting communications between a client and a server, ensuring that sensitive information remains private and tamper-proof.
This comprehensive guide will explore the fundamentals of SSH, its advantages, potential risks, and best practices for implementation. By the end of this article, you'll have a thorough understanding of how to leverage SSH remote access device for your personal or professional needs. Let's dive in!
Read also:Exploring The World Of Shue A Comprehensive Guide
Table of Contents
- Introduction to SSH
- How SSH Works
- Advantages of SSH
- Common Use Cases
- Securing SSH Connections
- Troubleshooting SSH
- Best Practices for SSH Remote Access Device
- Alternatives to SSH
- Frequently Asked Questions
- Conclusion
Introduction to SSH
Secure Shell (SSH) is a cryptographic network protocol designed to facilitate secure data communication, remote command execution, and other network services over an unsecured network. At its core, SSH remote access device provides a secure channel between a client and a server, ensuring that all data transmitted is encrypted and protected from unauthorized access.
Originally developed in 1995 as a replacement for less secure protocols like Telnet, SSH has since become an industry standard for remote access and administration. Its widespread adoption is driven by its robust security features, ease of use, and compatibility with a wide range of devices and operating systems.
SSH is widely used by IT professionals, developers, and system administrators to perform tasks such as:
- Managing remote servers
- Transferring files securely using SFTP (SSH File Transfer Protocol)
- Executing commands on remote machines
- Setting up secure tunnels for network traffic
Why SSH is Essential for Modern Networking
In today's interconnected world, where data breaches and cyberattacks are common, SSH plays a critical role in safeguarding sensitive information. By encrypting all communication between a client and a server, SSH ensures that even if the data is intercepted, it cannot be deciphered without the appropriate decryption key.
How SSH Works
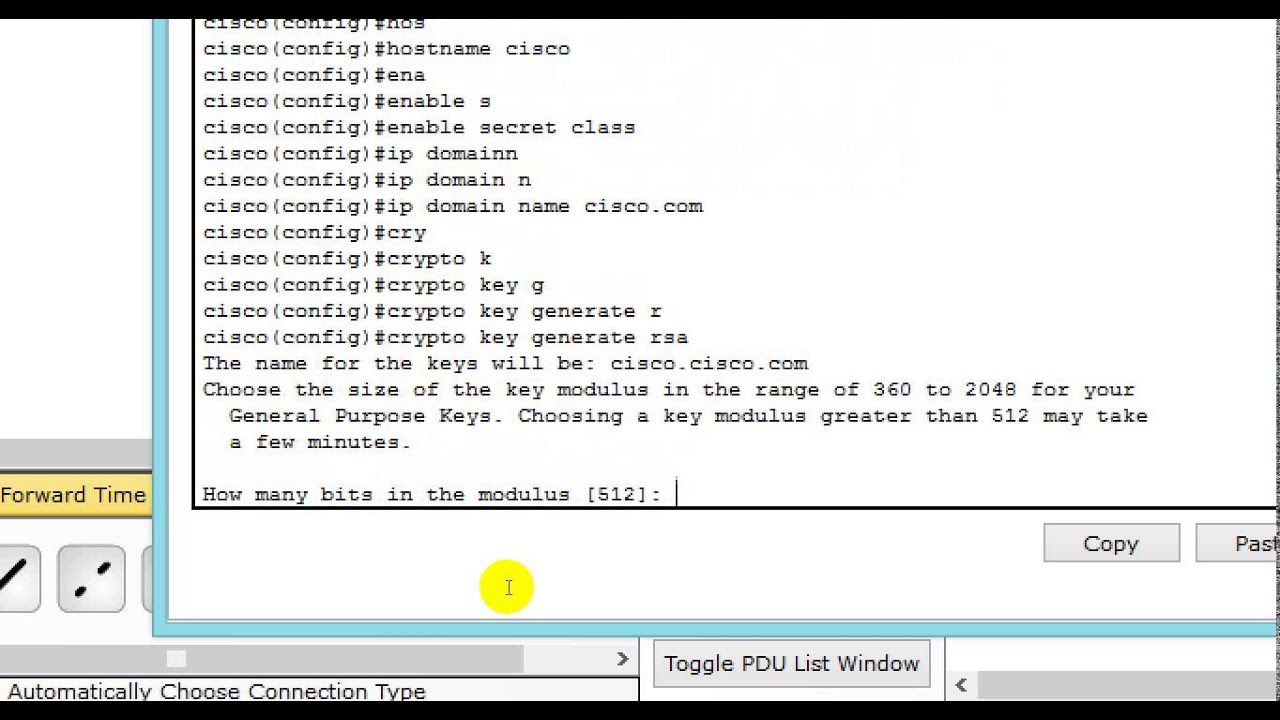
SSH operates using a client-server architecture, where the client initiates the connection and the server responds by authenticating the client and establishing a secure session. The process involves several key steps:
- Connection Establishment: The client connects to the server using the SSH protocol.
- Key Exchange: The client and server exchange cryptographic keys to establish a secure channel.
- Authentication: The client authenticates itself to the server using methods such as passwords, public key authentication, or two-factor authentication.
- Secure Session: Once authenticated, the client and server can communicate securely over the encrypted channel.
SSH uses a combination of symmetric and asymmetric encryption algorithms to ensure data security. Symmetric encryption is used for bulk data transfer, while asymmetric encryption is used for key exchange and authentication.
Read also:Discover The Fascinating World Of The Ice Age Cast
Key Components of SSH
Here are some of the key components that make SSH a powerful tool for secure communication:
- SSH Client: The software used to initiate an SSH connection, such as OpenSSH or PuTTY.
- SSH Server: The software running on the remote machine that accepts and manages SSH connections.
- Public Key Authentication: A secure method of authentication that uses a pair of cryptographic keys (public and private) to verify the identity of the client.
- Encryption Algorithms: SSH supports a variety of encryption algorithms, including AES, DES, and Blowfish, to secure data in transit.
Advantages of SSH
SSH remote access device offers numerous advantages that make it an indispensable tool for modern networking. Some of the key benefits include:
- Enhanced Security: SSH encrypts all communication between the client and server, protecting sensitive data from eavesdropping and tampering.
- Flexibility: SSH supports a wide range of applications, including remote command execution, file transfer, and tunneling.
- Platform Independence: SSH is compatible with virtually all major operating systems, including Linux, macOS, and Windows.
- Scalability: SSH can be used to manage large numbers of remote devices and servers simultaneously, making it ideal for enterprise environments.
SSH vs. Other Remote Access Protocols
While there are several protocols available for remote access, SSH stands out due to its robust security features and ease of use. Compared to older protocols like Telnet, SSH offers end-to-end encryption, eliminating the risk of data interception. Additionally, SSH's support for public key authentication makes it more secure than password-based authentication methods.
Common Use Cases
SSH remote access device is widely used across various industries and applications. Some of the most common use cases include:
- Server Administration: IT professionals use SSH to manage remote servers, perform system updates, and troubleshoot issues.
- File Transfer: SSH's SFTP protocol allows users to securely transfer files between local and remote machines.
- Network Tunneling: SSH can be used to create secure tunnels for network traffic, enabling users to bypass firewalls and access restricted resources.
- Automated Tasks: Developers and system administrators use SSH to automate repetitive tasks, such as running scripts or deploying code updates.
Real-World Examples of SSH in Action
Many organizations rely on SSH remote access device to streamline their operations. For example, cloud service providers like Amazon Web Services (AWS) and Google Cloud Platform (GCP) use SSH to allow customers to securely access their virtual machines. Similarly, financial institutions use SSH to protect sensitive data during remote transactions.
Securing SSH Connections
While SSH is inherently secure, it's important to take additional steps to protect your SSH connections from potential threats. Here are some best practices for securing SSH remote access device:
- Use Strong Passwords: Avoid using simple or easily guessable passwords, and consider implementing password policies that enforce complexity and expiration.
- Enable Public Key Authentication: Public key authentication is more secure than password-based authentication and eliminates the risk of brute-force attacks.
- Disable Root Login: Restricting root access reduces the risk of unauthorized users gaining administrative privileges.
- Use a Non-Standard Port: Changing the default SSH port (22) can help deter automated attacks and reduce the likelihood of brute-force attempts.
Advanced Security Measures
For added security, consider implementing the following advanced measures:
- Two-Factor Authentication: Require users to provide two forms of identification, such as a password and a one-time code, to access SSH connections.
- Firewall Rules: Configure firewall rules to restrict SSH access to specific IP addresses or networks.
- Logging and Monitoring: Enable logging and monitoring of SSH activity to detect and respond to suspicious behavior.
Troubleshooting SSH
Even with proper configuration, SSH connections can sometimes encounter issues. Here are some common problems and their solutions:
- Connection Refused: Check that the SSH server is running and that the correct port is being used.
- Authentication Failed: Verify that the correct username and password or key pair are being used.
- Timeout Errors: Increase the SSH timeout settings or check for network connectivity issues.
Tips for Effective Troubleshooting
When troubleshooting SSH remote access device issues, it's important to methodically identify and address the root cause. Start by reviewing server logs for error messages and consult the SSH documentation for guidance. Additionally, consider using tools like Wireshark or tcpdump to analyze network traffic and identify potential problems.
Best Practices for SSH Remote Access Device
Adopting best practices for SSH remote access device can help ensure the security and reliability of your connections. Here are some key recommendations:
- Regularly Update SSH Software: Keep your SSH client and server software up to date to protect against known vulnerabilities.
- Limit User Access: Restrict SSH access to only those users who require it, and assign appropriate permissions based on their roles.
- Monitor Activity: Regularly review SSH logs to detect and respond to suspicious activity.
- Document Procedures: Maintain clear documentation of your SSH configurations and procedures to ensure consistency and ease of troubleshooting.
Implementing SSH Best Practices in Your Organization
To successfully implement SSH best practices, it's essential to involve all stakeholders, including IT staff, developers, and system administrators. Provide training and resources to ensure that everyone understands the importance of SSH security and how to properly configure and use SSH remote access device.
Alternatives to SSH
While SSH is the most widely used protocol for secure remote access, there are other options available depending on your specific needs. Some alternatives to SSH include:
- Remote Desktop Protocol (RDP): Used primarily for Windows systems, RDP allows users to remotely access and control graphical interfaces.
- Virtual Network Computing (VNC): VNC provides remote access to graphical desktop environments and is supported on multiple platforms.
- Web-Based Interfaces: Some devices and services offer web-based interfaces for remote management, eliminating the need for SSH clients.
Choosing the Right Solution
When selecting a remote access solution, consider factors such as security requirements, platform compatibility, and ease of use. For most applications, SSH remote access device remains the gold standard due to its robust security features and versatility.
Frequently Asked Questions
What is SSH?
SSH (Secure Shell) is a cryptographic network protocol designed to facilitate secure data communication, remote command execution, and other network services over an unsecured network.
Is SSH secure?
Yes, SSH is highly secure when properly configured. It encrypts all communication between the client and server, protecting sensitive data from interception and tampering.
Can SSH be used on Windows?
Yes, SSH can be used on Windows. Modern versions of Windows include built-in support for SSH, allowing users to securely connect to remote servers and devices.
Conclusion
SSH remote access device is an essential tool for anyone working in the IT field or managing remote systems. Its robust security features, flexibility, and compatibility make it a popular choice for secure communication and remote access. By following the best practices outlined in this article, you can ensure that your SSH connections remain secure and reliable.
We encourage you to share this article with your colleagues and explore our other resources on cybersecurity and networking. If you have any questions or feedback, please leave a comment below. Together, we can create a safer digital world!