Securing VNC connections is crucial for protecting sensitive data and ensuring the integrity of your remote systems. Virtual Network Computing (VNC) allows users to access and control computers remotely, but without proper security measures, it can expose your network to unauthorized access and cyber threats. In this guide, we will explore the best practices, tools, and techniques to secure your VNC connections effectively.
As remote work becomes increasingly common, the demand for secure remote access solutions has grown exponentially. VNC is a popular choice for many organizations and individuals due to its simplicity and cross-platform compatibility. However, the growing number of cyberattacks targeting remote connections highlights the importance of implementing robust security measures.
This article delves into the intricacies of securing VNC connections, covering everything from encryption protocols to advanced security configurations. Whether you're a system administrator, IT professional, or an individual user, this guide will equip you with the knowledge and tools needed to safeguard your remote access infrastructure.
Read also:Sophie Thavet A Rising Star In The Entertainment Industry
Table of Contents
1. Introduction to VNC and Its Security Challenges
2. Understanding the Basics of VNC
3. Importance of Encryption in Securing VNC Connections
4. Strengthening Authentication for VNC
5. Configuring Firewalls to Protect VNC
6. Choosing the Right VNC Software for Enhanced Security
Read also:Unveiling The World Of Amateur Uk Facials A Comprehensive Guide
7. Advanced Techniques for Securing VNC Connections
8. Common Vulnerabilities in VNC and How to Address Them
9. Best Practices for Securing VNC Connections
10. The Future of VNC Security
Introduction to VNC and Its Security Challenges
Virtual Network Computing (VNC) is a widely used technology that enables users to remotely access and control computers over a network. While VNC offers numerous benefits, such as increased productivity and flexibility, it also introduces potential security risks. One of the primary concerns with VNC is the possibility of unauthorized access to sensitive systems and data.
Securing VNC connections requires a multi-layered approach that includes encryption, strong authentication, and proper network configuration. In this section, we will explore the fundamental security challenges associated with VNC and discuss why it is essential to address these issues proactively.
Understanding the Basics of VNC
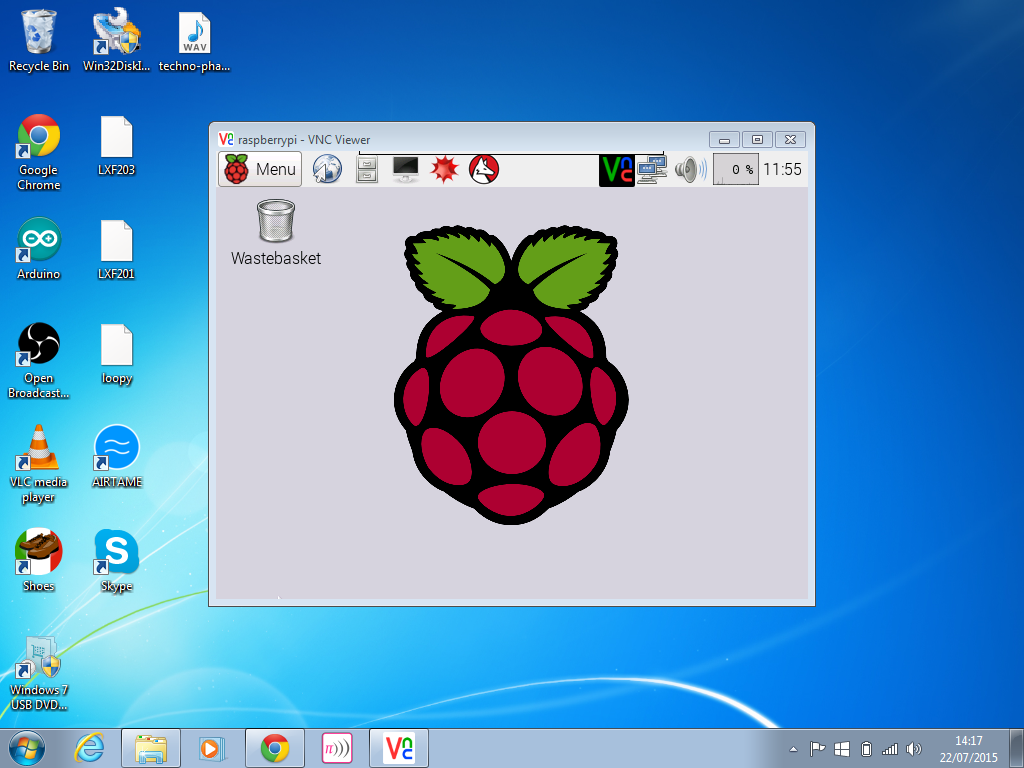
Before diving into the security aspects, it is important to understand how VNC works and its key components. VNC operates on a client-server model, where the server runs on the remote machine, and the client connects to it from another location. The communication between the server and client is facilitated through the Remote Frame Buffer (RFB) protocol.
Key Features of VNC
VNC offers several features that make it a popular choice for remote access:
- Platform independence, allowing cross-operating system compatibility.
- Real-time screen sharing and interaction.
- Support for multiple simultaneous connections.
However, these features also introduce potential vulnerabilities if not properly secured.
Importance of Encryption in Securing VNC Connections
Encryption plays a critical role in securing VNC connections by protecting data transmitted between the client and server. Without encryption, sensitive information, such as login credentials and personal data, can be intercepted by malicious actors. Implementing robust encryption protocols is essential to prevent unauthorized access and data breaches.
Types of Encryption for VNC
There are several encryption methods available for securing VNC connections:
- SSL/TLS Encryption: Provides a secure channel for data transmission.
- SSH Tunneling: Encrypts VNC traffic by routing it through a secure SSH connection.
- 128-bit AES Encryption: Offers strong encryption for sensitive data.
Selecting the appropriate encryption method depends on your specific security requirements and the capabilities of your VNC software.
Strengthening Authentication for VNC
Authentication is another critical aspect of securing VNC connections. Weak authentication mechanisms can leave your systems vulnerable to brute force attacks and unauthorized access. By implementing strong authentication protocols, you can significantly enhance the security of your VNC setup.
Best Authentication Practices
Here are some best practices for strengthening authentication in VNC:
- Use strong, complex passwords and enable password policies.
- Implement multi-factor authentication (MFA) for an additional layer of security.
- Regularly update and rotate passwords to minimize the risk of compromise.
These measures help ensure that only authorized users can access your VNC connections.
Configuring Firewalls to Protect VNC
Firewalls act as a barrier between your network and external threats, making them an essential component of VNC security. Properly configuring firewalls can help prevent unauthorized access and protect your systems from potential attacks.
Firewall Configuration Tips
Consider the following tips when configuring firewalls for VNC:
- Restrict access to VNC ports (default is 5900) to trusted IP addresses.
- Enable firewall rules to block suspicious traffic and potential threats.
- Regularly review and update firewall rules to adapt to evolving security needs.
By leveraging firewalls effectively, you can create a secure environment for your VNC connections.
Choosing the Right VNC Software for Enhanced Security
Not all VNC software solutions are created equal. Some offer advanced security features, while others may lack critical protections. When selecting VNC software, it is important to consider factors such as encryption capabilities, authentication options, and overall security features.
Recommended VNC Software
Here are some popular VNC software options known for their robust security:
- TightVNC: Offers lightweight and efficient performance with basic security features.
- RealVNC: Provides enterprise-grade security and advanced management capabilities.
- UltraVNC: Includes features like file transfer and enhanced encryption options.
Choose a solution that aligns with your security requirements and technical expertise.
Advanced Techniques for Securing VNC Connections
For organizations with stringent security needs, advanced techniques can further enhance the protection of VNC connections. These methods often involve integrating VNC with other security tools and technologies to create a comprehensive defense strategy.
Advanced Security Techniques
Consider implementing the following advanced techniques:
- Intrusion Detection Systems (IDS): Monitor VNC traffic for suspicious activity and potential threats.
- Network Segmentation: Isolate VNC connections from other network traffic to minimize exposure.
- Regular Audits and Vulnerability Assessments: Identify and address security weaknesses proactively.
These techniques can help organizations achieve a higher level of security for their VNC infrastructure.
Common Vulnerabilities in VNC and How to Address Them
Despite its many advantages, VNC is not immune to vulnerabilities. Understanding these weaknesses and taking proactive measures to address them is crucial for maintaining secure connections.
Common VNC Vulnerabilities
Some common vulnerabilities in VNC include:
- Weak or default passwords that can be easily guessed or brute-forced.
- Lack of encryption, leaving data transmissions exposed to interception.
- Improper firewall configurations that allow unauthorized access.
By addressing these vulnerabilities through strong security practices, you can significantly reduce the risk of breaches.
Best Practices for Securing VNC Connections
To ensure the security of your VNC connections, it is important to follow a set of best practices that cover all aspects of the setup and configuration process.
Key Best Practices
Here are some best practices for securing VNC connections:
- Use encryption protocols like SSL/TLS or SSH tunneling for secure data transmission.
- Implement strong authentication mechanisms, including MFA and complex passwords.
- Regularly update VNC software and apply security patches to address known vulnerabilities.
By adhering to these best practices, you can create a secure and reliable VNC environment.
The Future of VNC Security
As technology continues to evolve, so do the threats targeting remote access solutions like VNC. The future of VNC security will likely involve advancements in encryption, authentication, and threat detection technologies. Organizations must stay informed about emerging trends and adopt new security measures as needed to protect their systems and data.
Emerging technologies such as artificial intelligence and machine learning may play a significant role in enhancing VNC security by enabling more sophisticated threat detection and response capabilities.
Conclusion
Securing VNC connections is essential for protecting sensitive data and ensuring the integrity of your remote systems. By implementing encryption, strengthening authentication, configuring firewalls, and following best practices, you can significantly enhance the security of your VNC setup. Stay proactive and vigilant in addressing potential vulnerabilities to safeguard your network from cyber threats.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into cybersecurity and remote access solutions. Together, let's build a safer digital world!