SSH key management system plays a crucial role in securing digital communications and protecting sensitive data. In today's interconnected world, ensuring secure access to systems and networks is more important than ever. Organizations of all sizes rely on SSH keys to authenticate users and automate processes, making proper management a top priority.
As cybersecurity threats continue to evolve, understanding how to manage SSH keys effectively is essential. Mismanagement of SSH keys can lead to significant vulnerabilities, exposing sensitive information to unauthorized access. This article delves into the nuances of SSH key management systems, offering practical advice and actionable insights for secure implementation.
Whether you're an IT professional, a system administrator, or simply someone interested in cybersecurity, this guide will equip you with the knowledge and tools needed to implement a robust SSH key management strategy. Let's explore the ins and outs of this critical security component.
Read also:Dracula 2000 Actors Unveiling The Talented Cast Behind The Classic Vampire Tale
Table of Contents
- Introduction to SSH Key Management System
- What is SSH?
- The Importance of SSH Key Management
- Common Challenges in SSH Key Management
- Best Practices for SSH Key Management
- Tools for Managing SSH Keys
- Enhancing Security with SSH Key Management
- Automation in SSH Key Management
- Compliance and Regulatory Requirements
- The Future of SSH Key Management
Introduction to SSH Key Management System
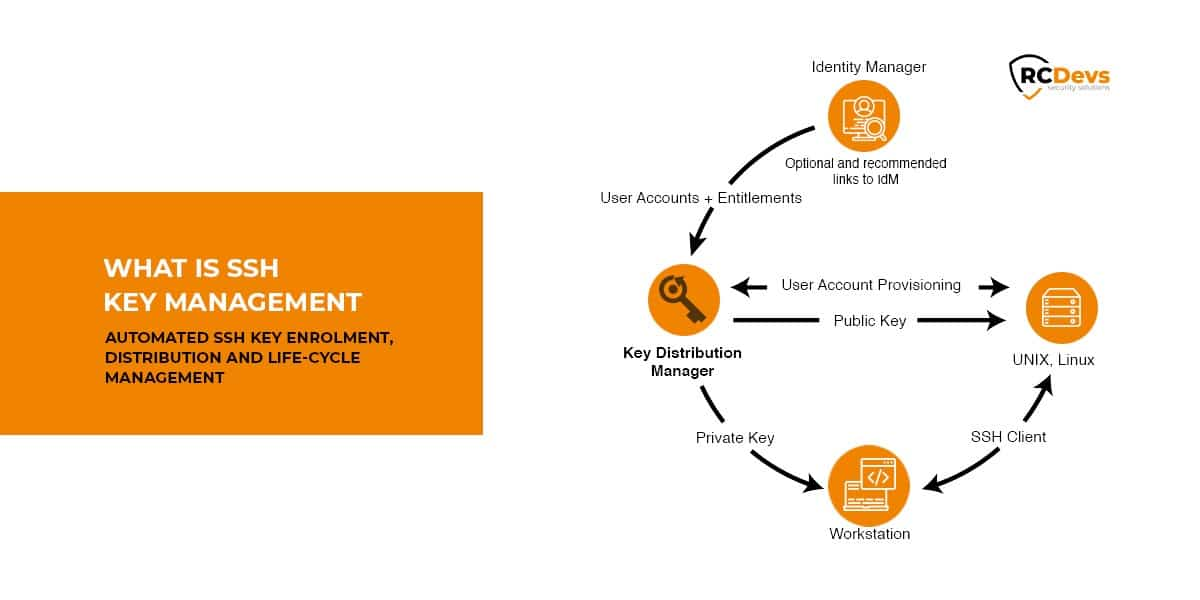
SSH (Secure Shell) is a cryptographic protocol used for secure communication between systems. At the heart of SSH lies the concept of key pairs—public and private keys—that facilitate secure authentication. An SSH key management system ensures these keys are properly generated, distributed, and revoked when necessary. This foundational system is critical for maintaining security and operational efficiency.
The importance of SSH key management cannot be overstated. Poorly managed keys can lead to unauthorized access, data breaches, and compliance violations. Organizations must adopt a proactive approach to key management, leveraging best practices and advanced tools to safeguard their infrastructure.
What is SSH?
Understanding SSH Protocol
SSH, or Secure Shell, is a network protocol designed to provide secure communication over unsecured networks. It encrypts data transmitted between systems, ensuring confidentiality and integrity. SSH is widely used for remote server access, file transfers, and command execution.
SSH operates on a client-server model, where the client initiates a connection to the server. Authentication is achieved through password-based or key-based methods. Key-based authentication, which relies on SSH keys, is preferred due to its enhanced security and convenience.
The Importance of SSH Key Management
Why SSH Key Management Matters
SSH keys serve as digital credentials that grant access to critical systems and data. Without proper management, these keys can become a liability. For example, unused or unrevoked keys can remain active, providing potential entry points for malicious actors. Effective SSH key management mitigates these risks by ensuring keys are properly tracked and controlled.
Key management also plays a vital role in compliance with industry regulations. Standards such as PCI-DSS, HIPAA, and GDPR require organizations to maintain strict control over access to sensitive data. By implementing a robust SSH key management system, businesses can meet these requirements and avoid costly penalties.
Read also:Mr Peabody Amp Sherman Cast A Comprehensive Look At The Voices Behind The Timetraveling Duo
Common Challenges in SSH Key Management
Identifying Key Management Issues
Managing SSH keys presents several challenges, including:
- Key sprawl: The proliferation of SSH keys across systems makes tracking and managing them difficult.
- Lack of visibility: Without centralized oversight, it's challenging to know which keys exist, who owns them, and where they are used.
- Expired or unused keys: Keys that remain active after their intended lifespan pose significant security risks.
- Inadequate revocation processes: Failing to revoke keys promptly when employees leave or systems are decommissioned can lead to unauthorized access.
Addressing these challenges requires a strategic approach that combines technology, processes, and policies.
Best Practices for SSH Key Management
Implementing Effective Key Management Strategies
To ensure secure and efficient SSH key management, consider the following best practices:
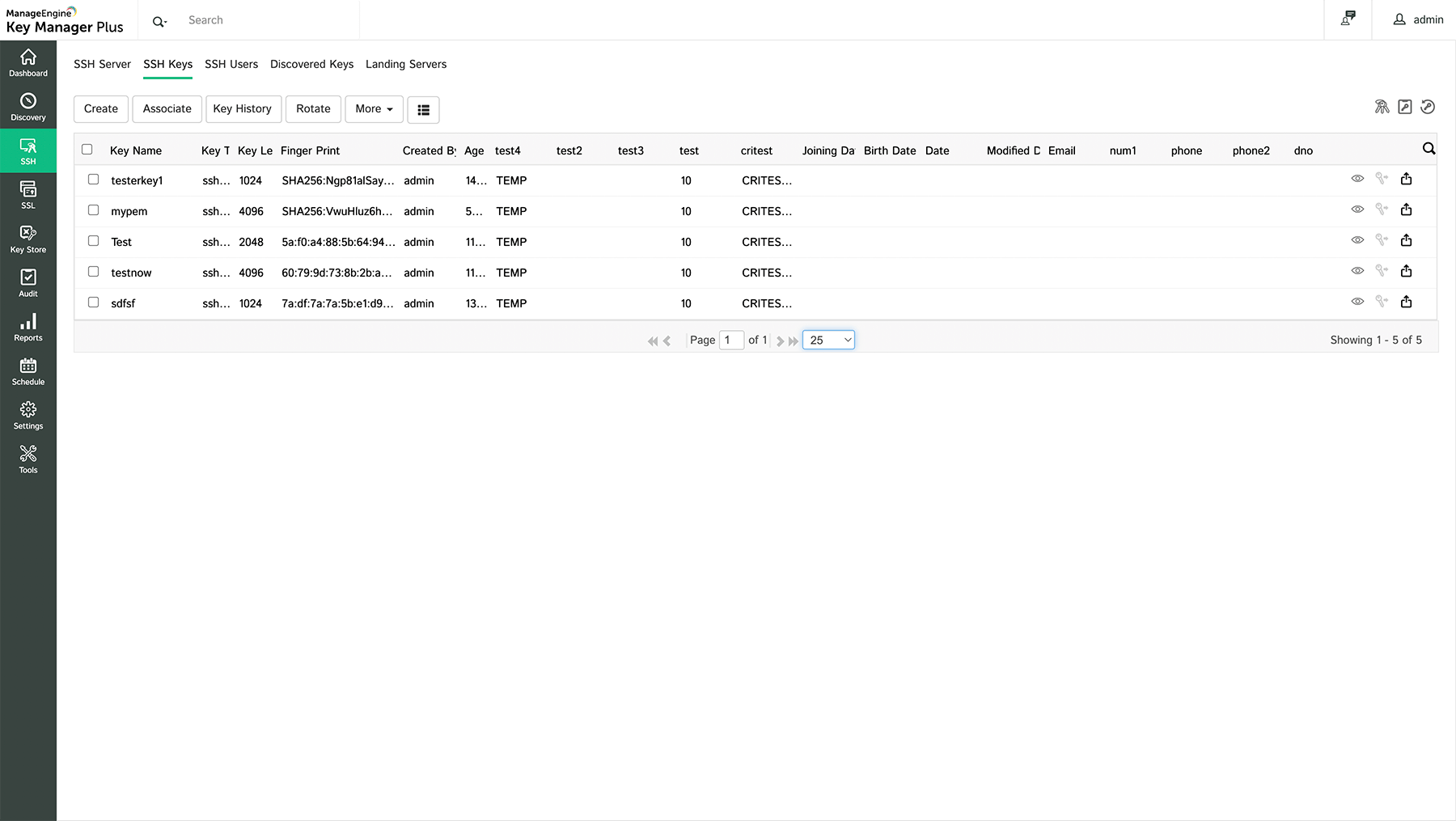
- Centralized key storage: Use a centralized repository to store and manage SSH keys, ensuring consistency and control.
- Regular audits: Conduct periodic audits to identify and remove unused or expired keys.
- Access controls: Implement strict access controls to limit who can generate, distribute, or revoke keys.
- Key rotation: Establish a schedule for rotating keys to minimize the risk of compromise.
- Documentation: Maintain detailed documentation of key usage, ownership, and lifecycle management.
By adhering to these practices, organizations can significantly reduce the risk of SSH-related security incidents.
Tools for Managing SSH Keys
Exploring Key Management Solutions
Several tools and platforms are available to streamline SSH key management. These solutions offer features such as key generation, distribution, monitoring, and revocation. Some popular options include:
- SSH Key Management System (SKMS): A dedicated tool designed for managing SSH keys across large-scale environments.
- HashiCorp Vault: A secrets management platform that supports SSH key management among other security features.
- CyberArk: A comprehensive privileged access management solution that includes robust SSH key management capabilities.
Choosing the right tool depends on factors such as organizational size, complexity, and budget. Evaluating these options carefully can help organizations select the best solution for their needs.
Enhancing Security with SSH Key Management
Strengthening Security Measures
SSH key management is a cornerstone of cybersecurity. By implementing strong key management practices, organizations can enhance their overall security posture. Key strategies include:
- Encryption: Use strong encryption algorithms to protect SSH keys during transmission and storage.
- Multi-factor authentication: Combine SSH key authentication with additional factors, such as passwords or biometrics, for added security.
- Intrusion detection: Monitor SSH activity for signs of unauthorized access or suspicious behavior.
These measures, combined with a proactive key management approach, can help organizations stay ahead of emerging threats.
Automation in SSH Key Management
Streamlining Processes with Automation
Automation plays a critical role in modern SSH key management. By automating repetitive tasks such as key generation, distribution, and revocation, organizations can reduce human error and improve efficiency. Automation tools can also provide real-time monitoring and alerts, enabling swift responses to potential security issues.
Additionally, automation facilitates compliance with regulatory requirements by maintaining detailed records of key management activities. This ensures organizations can demonstrate adherence to standards when required.
Compliance and Regulatory Requirements
Meeting Industry Standards
Compliance with industry regulations is a key driver for adopting robust SSH key management practices. Standards such as PCI-DSS, HIPAA, and GDPR mandate strict controls over access to sensitive data. Organizations must implement measures to ensure SSH keys are properly managed and protected.
Key compliance considerations include:
- Access control: Limiting who can generate, distribute, or revoke SSH keys.
- Audit trails: Maintaining detailed logs of key management activities.
- Data protection: Ensuring SSH keys are stored securely and encrypted.
By aligning SSH key management practices with regulatory requirements, organizations can avoid costly fines and reputational damage.
The Future of SSH Key Management
Trends and Innovations
As technology continues to evolve, so too does the landscape of SSH key management. Emerging trends such as cloud computing, DevOps, and IoT are driving the need for more advanced and scalable key management solutions. Innovations in areas such as artificial intelligence and machine learning are also poised to transform how SSH keys are managed and secured.
Looking ahead, organizations must remain adaptable and embrace new technologies to stay ahead of security challenges. By investing in cutting-edge tools and strategies, businesses can ensure their SSH key management systems remain effective and secure in the years to come.
Kesimpulan
In conclusion, SSH key management system is a critical component of modern cybersecurity. Properly managing SSH keys is essential for protecting sensitive data, ensuring operational efficiency, and maintaining compliance with industry regulations. By adopting best practices, leveraging advanced tools, and staying informed about emerging trends, organizations can implement a robust SSH key management strategy.
We encourage readers to take action by reviewing their current SSH key management processes and identifying areas for improvement. Share your thoughts and experiences in the comments below, and explore other articles on our site for more insights into cybersecurity and IT management.