In today's rapidly evolving digital landscape, AWS IoT Tunnel has emerged as a critical tool for enabling secure and efficient communication between IoT devices and cloud applications. As businesses increasingly rely on connected devices to gather data, monitor operations, and automate processes, the need for secure and reliable communication channels has never been greater. AWS IoT Tunnel addresses this need by providing a secure, bi-directional communication pathway that simplifies device management and enhances security.
AWS IoT Tunnel is more than just another tool in the IoT ecosystem. It represents a significant advancement in how organizations can manage and interact with IoT devices remotely. By enabling secure tunneling between IoT devices and applications, it allows for seamless device management, troubleshooting, and data exchange without exposing sensitive information to potential threats.
As we delve deeper into the capabilities and benefits of AWS IoT Tunnel, it becomes clear why this service is becoming an essential component for businesses looking to harness the full potential of IoT technology. From enhancing security to simplifying device management, AWS IoT Tunnel offers a comprehensive solution for modern IoT challenges.
Read also:Top Book Publishing Companies In Dallas Your Ultimate Guide
Table of Contents
- Introduction to AWS IoT Tunnel
- AWS IoT Tunnel Architecture
- Security Features of AWS IoT Tunnel
- Use Cases for AWS IoT Tunnel
- Comparison with Other IoT Solutions
- Steps for Implementing AWS IoT Tunnel
- Benefits of Using AWS IoT Tunnel
- Challenges and Limitations
- Best Practices for AWS IoT Tunnel
- The Future of AWS IoT Tunnel
Introduction to AWS IoT Tunnel
AWS IoT Tunnel is a service designed to facilitate secure communication between IoT devices and cloud applications. It enables organizations to establish bi-directional communication channels without exposing devices to potential security risks. This service is particularly useful for managing devices that are deployed in remote or inaccessible locations, where physical access is limited or impractical.
One of the key advantages of AWS IoT Tunnel is its ability to create encrypted tunnels that protect data in transit. This ensures that sensitive information remains secure, even when devices are communicating over public networks. Additionally, the service supports a wide range of use cases, from industrial automation to smart home applications, making it a versatile solution for various industries.
How AWS IoT Tunnel Works
AWS IoT Tunnel operates by establishing a secure connection between a device and a cloud application. This connection is maintained through a series of protocols and encryption methods that ensure data integrity and confidentiality. The service also provides tools for monitoring and managing these connections, allowing administrators to maintain control over device interactions.
- Establishes secure tunnels between devices and applications.
- Supports bi-directional communication for enhanced functionality.
- Uses encryption and authentication protocols to protect data.
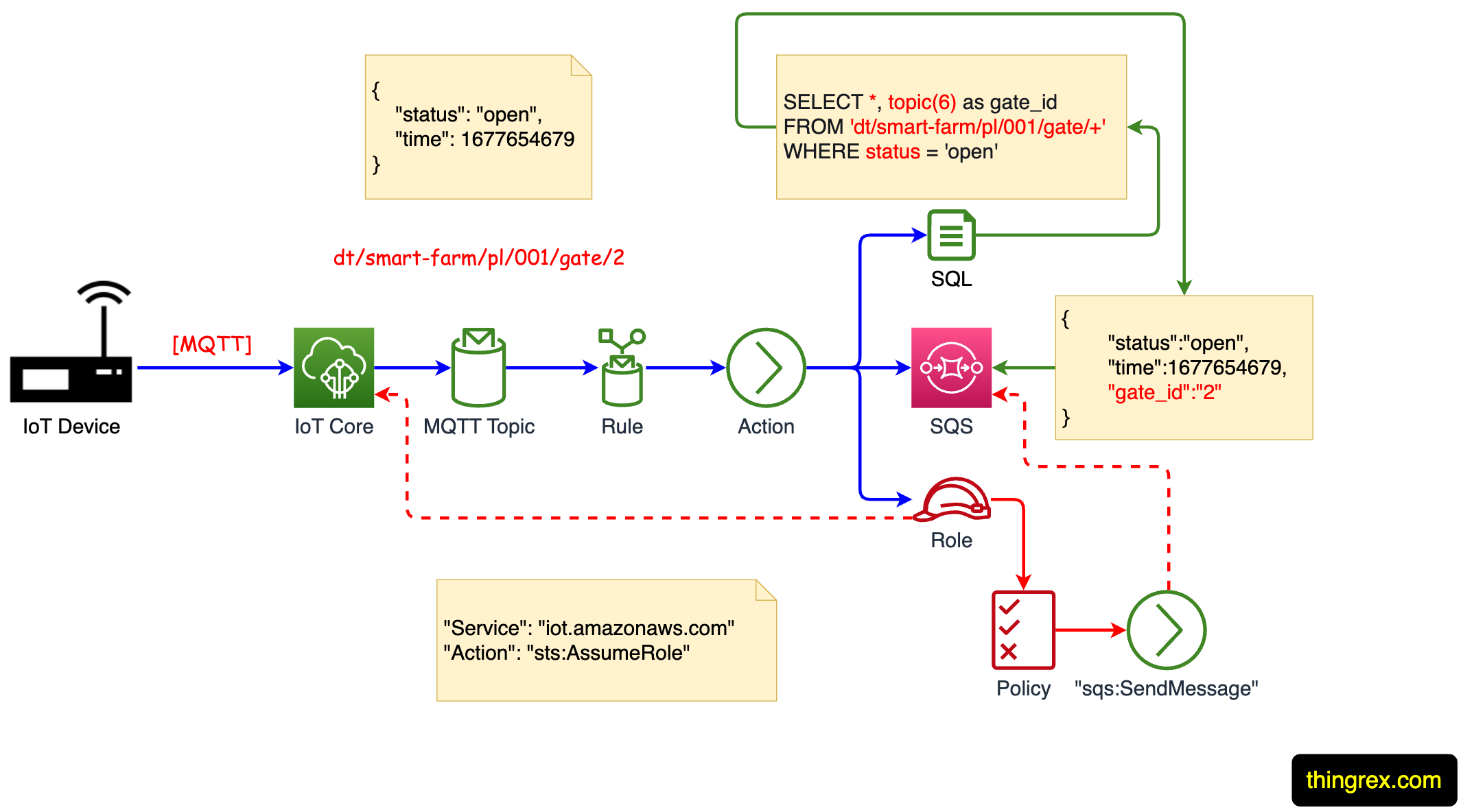
AWS IoT Tunnel Architecture
The architecture of AWS IoT Tunnel is designed to provide flexibility and scalability while maintaining high levels of security. At its core, the service relies on a combination of AWS IoT Core, AWS IoT Device Management, and AWS IoT Greengrass to create a robust communication framework. This architecture enables seamless integration with existing AWS services and simplifies device management processes.
Key Components of AWS IoT Tunnel
AWS IoT Tunnel incorporates several key components that work together to deliver its functionality:
- AWS IoT Core: Provides the foundation for device communication and data processing.
- AWS IoT Device Management: Offers tools for managing device fleets and monitoring device health.
- AWS IoT Greengrass: Enables local computation and data processing for IoT devices.
Security Features of AWS IoT Tunnel
Security is a top priority for AWS IoT Tunnel, and the service includes a range of features designed to protect devices and data. These features include encryption, authentication, and access control, all of which work together to create a secure communication environment.
Read also:Running Man 2025 Cast Korea The Ultimate Guide To The Beloved Reality Show
Encryption and Authentication
AWS IoT Tunnel uses industry-standard encryption protocols to protect data in transit. This ensures that even if data is intercepted, it remains unreadable to unauthorized parties. Additionally, the service employs robust authentication mechanisms to verify the identity of devices and applications, preventing unauthorized access.
According to a report by Gartner, "IoT security is a critical concern for organizations deploying connected devices, and services like AWS IoT Tunnel play a vital role in addressing these concerns."
Use Cases for AWS IoT Tunnel
AWS IoT Tunnel supports a wide range of use cases across various industries. Some of the most common applications include:
- Remote device management for industrial equipment.
- Secure data transfer for healthcare devices.
- Smart home automation for consumer products.
- Asset tracking and monitoring for logistics operations.
Industrial Use Case
In the manufacturing sector, AWS IoT Tunnel can be used to monitor and manage production equipment remotely. This allows engineers to diagnose issues and perform maintenance without needing to be physically present at the facility, saving time and reducing costs.
Comparison with Other IoT Solutions
While there are several IoT solutions available in the market, AWS IoT Tunnel stands out due to its focus on security and ease of use. Compared to other services, AWS IoT Tunnel offers a more comprehensive approach to device communication and management, making it an ideal choice for organizations looking to implement IoT solutions at scale.
Key Differentiators
- Strong emphasis on security and data protection.
- Seamless integration with AWS ecosystem.
- Flexible pricing options for different use cases.
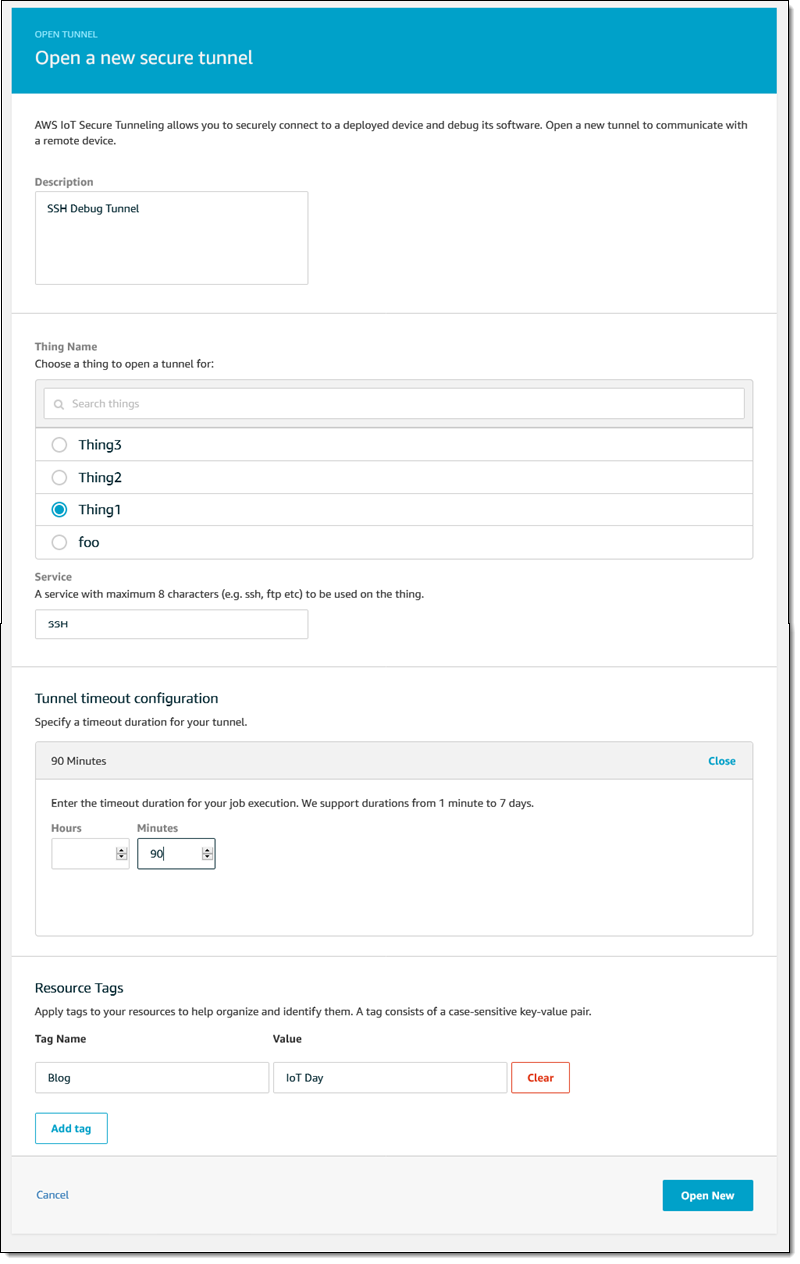
Steps for Implementing AWS IoT Tunnel
Implementing AWS IoT Tunnel involves several key steps, including setting up the necessary infrastructure, configuring devices, and testing the communication pathways. Below is a step-by-step guide to help organizations get started with AWS IoT Tunnel:
- Provision devices and register them with AWS IoT Core.
- Configure security settings and establish encryption protocols.
- Set up monitoring and management tools for ongoing device oversight.
- Test the communication pathways to ensure reliable data transfer.
Benefits of Using AWS IoT Tunnel
Organizations that adopt AWS IoT Tunnel can expect to see numerous benefits, including improved security, enhanced device management capabilities, and increased operational efficiency. These benefits make AWS IoT Tunnel an attractive option for businesses looking to leverage IoT technology effectively.
Enhanced Security
By providing secure communication channels, AWS IoT Tunnel reduces the risk of data breaches and unauthorized access. This is particularly important for industries such as healthcare and finance, where data security is paramount.
Challenges and Limitations
Despite its many advantages, AWS IoT Tunnel does have some limitations that organizations should consider before implementation. These include potential latency issues for devices located in remote areas and the need for specialized expertise to configure and manage the service effectively.
Addressing Latency Issues
To mitigate latency concerns, AWS recommends using AWS IoT Greengrass for local data processing. This allows devices to perform critical operations without relying on cloud connectivity, reducing the impact of network delays.
Best Practices for AWS IoT Tunnel
To maximize the effectiveness of AWS IoT Tunnel, organizations should follow best practices for device management and security. These practices include regular software updates, thorough testing of communication pathways, and ongoing monitoring of device performance.
Regular Software Updates
Keeping devices and applications up to date with the latest software versions is essential for maintaining security and functionality. Organizations should establish a routine schedule for updates and ensure that all devices are compliant with current standards.
The Future of AWS IoT Tunnel
As IoT technology continues to evolve, AWS IoT Tunnel is likely to play an increasingly important role in shaping the future of connected devices. With ongoing advancements in security, scalability, and ease of use, this service is poised to become an indispensable tool for businesses across a wide range of industries.
A report by McKinsey & Company predicts that "IoT adoption will grow exponentially over the next decade, driven by advancements in technology and increasing demand for connected solutions."
Conclusion
In conclusion, AWS IoT Tunnel offers a comprehensive solution for secure and efficient IoT device communication. By addressing key challenges such as security, scalability, and ease of use, this service provides organizations with the tools they need to successfully implement IoT solutions. We encourage readers to explore the capabilities of AWS IoT Tunnel further and consider how it can benefit their own operations.
Take the next step by implementing AWS IoT Tunnel in your organization and experience the benefits firsthand. Share your thoughts and experiences in the comments below, and don't forget to explore other articles on our site for more insights into IoT technology and its applications.