Connecting remote IoT devices securely using P2P SSH on Windows has become an essential skill for modern IT professionals and enthusiasts alike. As the Internet of Things (IoT) continues to expand, ensuring secure communication between devices is more critical than ever. This guide will walk you through the process step by step, helping you protect your data while enabling seamless device management.
In today's interconnected world, IoT devices are everywhere, from smart homes to industrial automation systems. However, with this convenience comes the challenge of maintaining security. Securely connecting remote IoT devices via P2P SSH ensures that your sensitive data remains protected from unauthorized access and cyber threats.
This article aims to provide a detailed explanation of how to securely connect remote IoT devices using P2P SSH on Windows. By following the steps outlined here, you'll gain the expertise needed to safeguard your IoT ecosystem while optimizing performance. Let's dive in!
Read also:Heather Turman The Inspiring Journey Of A Trailblazing Actress
Table of Contents
- Introduction to Remote IoT Connections
- What is P2P SSH?
- Setting Up SSH on Windows
- Ensuring Secure Connections
- Downloading Necessary Tools
- Step-by-Step Guide to Connecting IoT Devices
- Best Practices for Secure IoT Connections
- Troubleshooting Common Issues
- Real-World Case Studies
- Conclusion
Introduction to Remote IoT Connections
Remote IoT connections enable devices to communicate and exchange data across networks, even when they are physically distant. This capability is crucial for managing smart devices, monitoring environmental conditions, and automating processes in various industries.
When it comes to securely connect remote IoT devices, P2P SSH offers a robust solution. By leveraging encryption and authentication protocols, P2P SSH ensures that data transmitted between devices remains confidential and tamper-proof.
Why Secure IoT Connections Matter
IoT devices are often deployed in environments where security risks are high. Without proper protection, these devices can become entry points for cyberattacks, compromising sensitive information and disrupting operations.
What is P2P SSH?
P2P SSH, or peer-to-peer Secure Shell, allows direct communication between two devices over a secure channel. Unlike traditional client-server architectures, P2P SSH eliminates the need for intermediaries, reducing latency and enhancing security.
Key Features of P2P SSH
- Encryption: Data is encrypted during transmission, preventing eavesdropping.
- Authentication: Devices verify each other's identities before establishing a connection.
- Scalability: Suitable for connecting multiple devices in a decentralized network.
Setting Up SSH on Windows
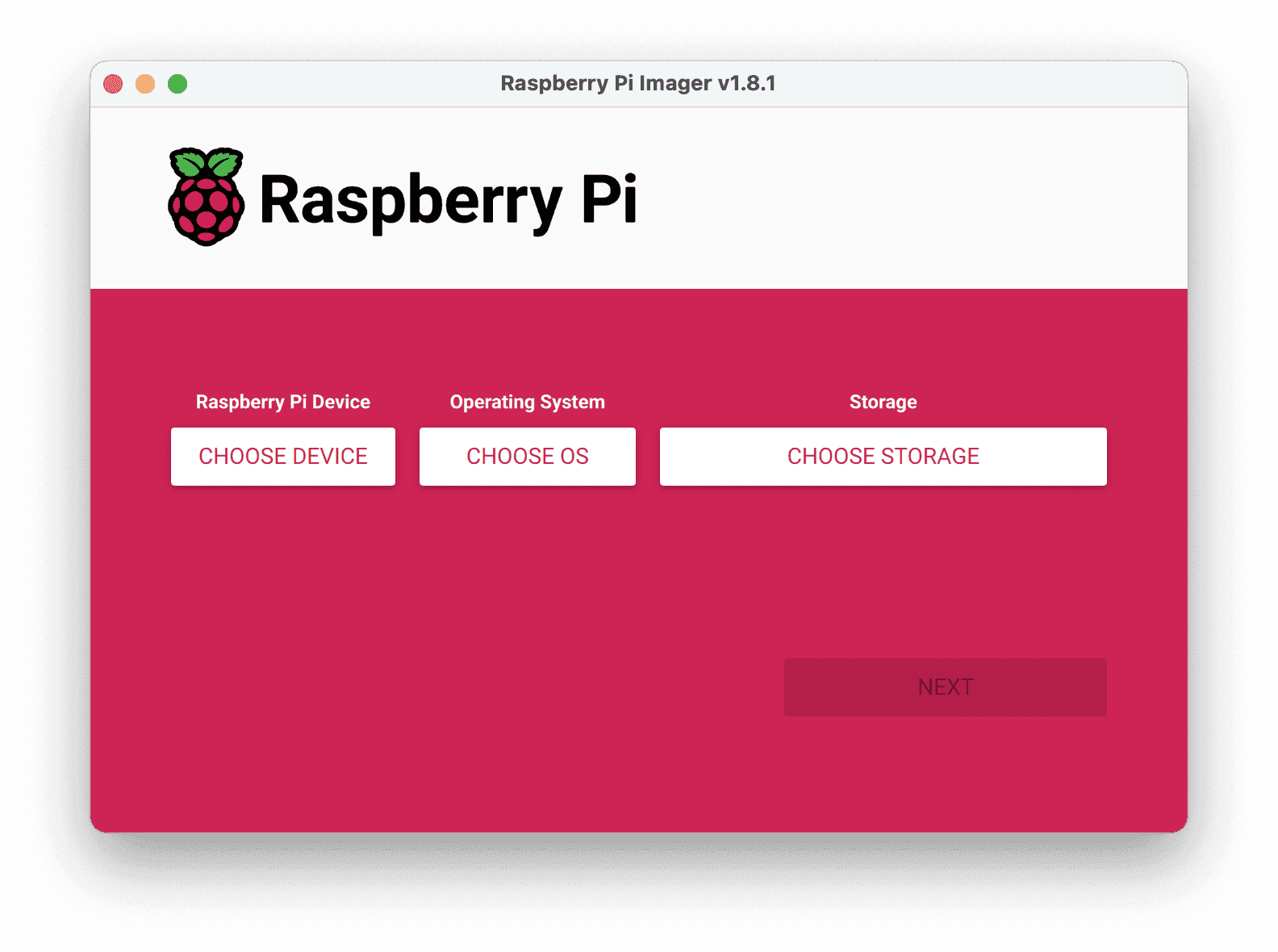
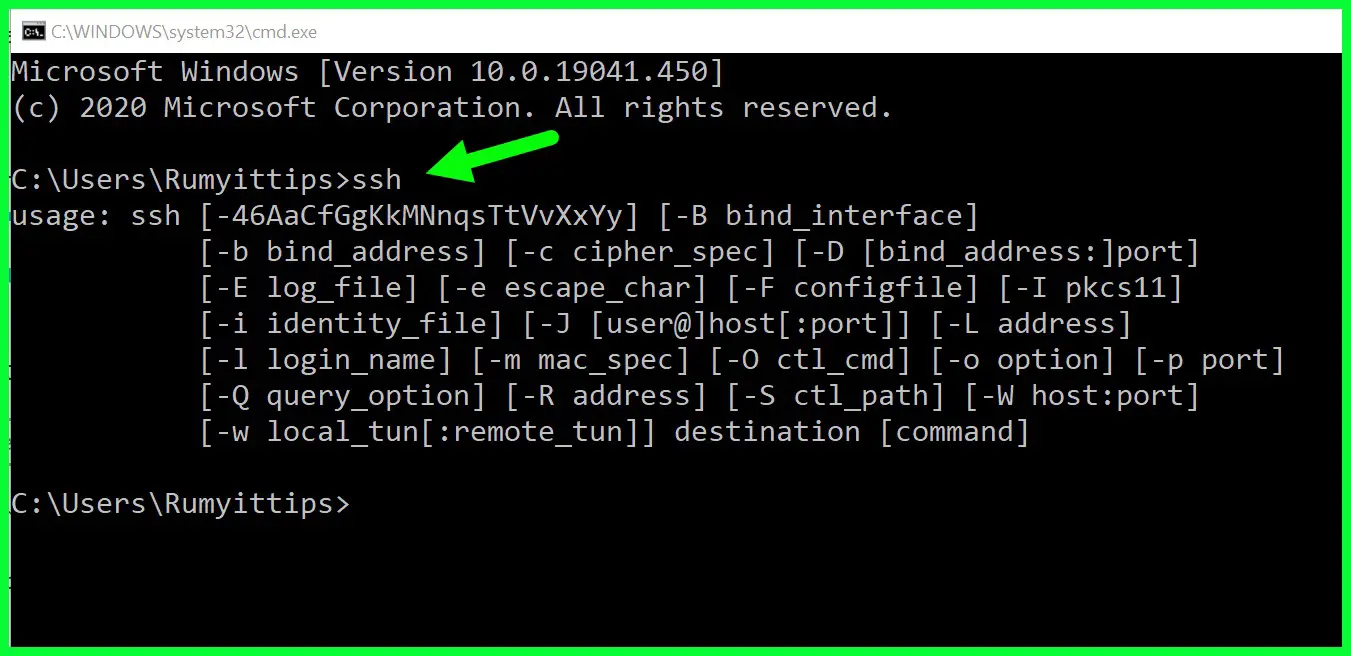
Windows provides built-in support for SSH, making it easy to configure secure connections for IoT devices. Follow these steps to enable SSH on your Windows machine:
- Open the Windows Settings app.
- Navigate to Apps > Optional Features.
- Select Add a feature and search for "OpenSSH Server."
- Install the OpenSSH Server and restart your computer if prompted.
Verifying SSH Installation
Once installed, verify that the SSH service is running by opening PowerShell and typing:
Read also:Ice Age Cast Meet The Voices Behind The Prehistoric Adventure
Get-Service sshd
If the service status is "Running," SSH is successfully set up on your Windows machine.
Ensuring Secure Connections
Securing your IoT connections involves implementing best practices to protect against potential threats. Here are some key strategies:
Use Strong Authentication
Employ strong passwords or public key authentication to prevent unauthorized access. Avoid using default credentials and regularly update your authentication methods.
Enable Firewall Rules
Configure firewall settings to restrict incoming connections to trusted IP addresses. This minimizes the risk of unauthorized access attempts.
Downloading Necessary Tools
To securely connect remote IoT devices using P2P SSH, you may need additional tools such as PuTTY or WinSCP. These applications simplify the process of establishing and managing SSH connections on Windows.
Popular Tools for SSH Connections
- PuTTY: A free and widely-used SSH client for Windows.
- WinSCP: A secure file transfer application that supports SFTP and SCP protocols.
Step-by-Step Guide to Connecting IoT Devices
Follow this step-by-step guide to securely connect your remote IoT devices using P2P SSH on Windows:
- Install and configure the SSH server on your Windows machine.
- Download and install PuTTY or WinSCP on your local computer.
- Enter the IP address of your remote IoT device in the SSH client.
- Authenticate using your chosen method (password or public key).
- Establish a secure connection and begin managing your IoT device.
Example Configuration
For example, if your IoT device has an IP address of 192.168.1.100, open PuTTY and enter this address in the "Host Name (or IP address)" field. Set the port to 22 (default SSH port) and click "Open" to initiate the connection.
Best Practices for Secure IoT Connections
Adopting best practices is essential for maintaining secure IoT connections. Consider the following recommendations:
Regularly Update Firmware
Keep your IoT device firmware up to date to address any security vulnerabilities discovered by manufacturers.
Monitor Network Activity
Implement network monitoring tools to detect and respond to suspicious activities promptly.
Troubleshooting Common Issues
Encountering issues while setting up SSH connections is not uncommon. Here are some troubleshooting tips:
Connection Refused
If you receive a "Connection refused" error, ensure that the SSH service is running on the remote device and that firewall rules allow incoming connections.
Authentication Failed
Double-check your credentials and authentication settings. Ensure that public keys are correctly configured if using key-based authentication.
Real-World Case Studies
Several organizations have successfully implemented P2P SSH for secure IoT connections. For instance, a manufacturing company used this method to monitor and control industrial sensors remotely, improving operational efficiency and reducing downtime.
Case Study: Smart Home Automation
A homeowner implemented P2P SSH to manage smart lighting and climate control systems. By securing these connections, they ensured the privacy and safety of their household data.
Conclusion
Securing remote IoT connections using P2P SSH on Windows is a vital step in protecting your devices and data. By following the guidelines outlined in this article, you can establish robust and reliable connections while minimizing security risks.
We encourage you to apply the knowledge gained here and share your experiences in the comments below. For further reading, explore our other articles on IoT security and best practices. Together, let's build a safer and more connected world!
References: