In today's interconnected world, IoT devices are revolutionizing the way we interact with technology. Best IoT device SSH access plays a crucial role in ensuring secure remote management of these devices. Whether you're a tech enthusiast or a professional managing a network of IoT devices, understanding SSH access is essential for maintaining security and efficiency.
IoT (Internet of Things) has become an integral part of modern living, connecting everyday devices to the internet. From smart homes to industrial automation, IoT devices are everywhere. However, with this connectivity comes the need for robust security measures, especially when it comes to accessing and managing these devices remotely.
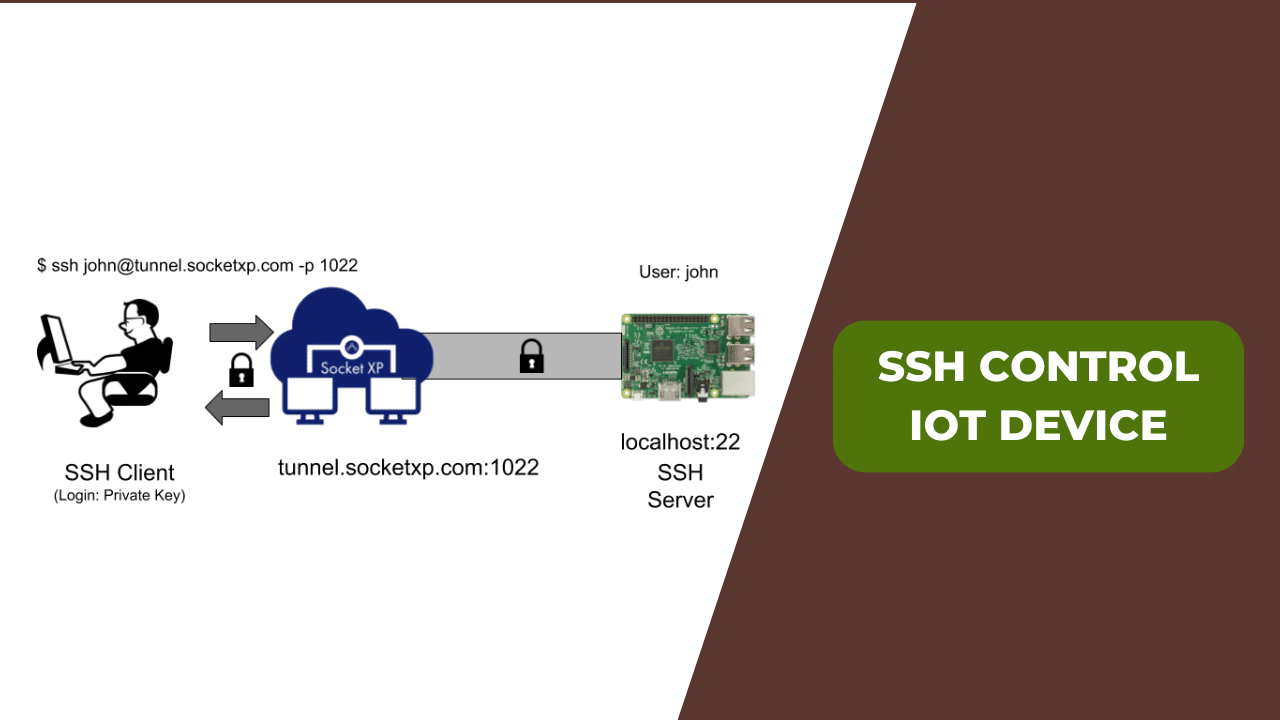
Secure Shell (SSH) is a protocol designed to provide secure remote access to network devices. When combined with IoT devices, SSH ensures that your data remains protected while allowing seamless control over your devices. In this article, we will explore the best IoT devices that offer SSH access, their features, and how to set them up securely.
Read also:Tara Elders The Rising Star In The Spotlight
Table of Contents:
- Introduction to IoT and SSH
- Overview of IoT Devices
- Why SSH is Important for IoT Devices
- Best IoT Devices for SSH Access
- How to Set Up SSH Access on IoT Devices
- Security Tips for SSH Access
- Common Issues and Troubleshooting
- Comparison of IoT Devices with SSH Access
- Future Trends in IoT and SSH
- Conclusion and Call to Action
Introduction to IoT and SSH
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity that allow them to exchange data. SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication between devices. For IoT devices, SSH access ensures that your interactions remain private and protected from unauthorized access.
What is IoT?
IoT encompasses a wide range of devices, from simple household appliances to complex industrial machinery. These devices are equipped with sensors and connectivity features that enable them to communicate with each other and with users. Understanding the basics of IoT is essential for grasping the significance of SSH access in securing these devices.
What is SSH?
SSH is a protocol designed to provide secure remote access to network devices. It encrypts all data transmitted between devices, ensuring that sensitive information remains confidential. For IoT devices, SSH access is a critical component of maintaining security and operational efficiency.
Overview of IoT Devices
IoT devices come in various forms and serve different purposes. From smart thermostats to industrial sensors, these devices are designed to enhance convenience, efficiency, and productivity. Understanding the types of IoT devices available is the first step in selecting the best option for your needs.
Types of IoT Devices
- Consumer IoT Devices: Devices designed for personal use, such as smart home systems, wearables, and smart appliances.
- Enterprise IoT Devices: Devices used in business settings, including industrial sensors, smart lighting systems, and asset tracking solutions.
- Industrial IoT Devices: Devices employed in manufacturing and production environments, such as robotics, predictive maintenance systems, and supply chain management tools.
Why SSH is Important for IoT Devices
SSH plays a vital role in ensuring the security of IoT devices. By encrypting all data transmitted between devices, SSH prevents unauthorized access and data breaches. This is particularly important for IoT devices, which are often connected to sensitive networks and systems.
Read also:Think Like A Man 2 Actors A Comprehensive Dive Into The Talented Cast
Benefits of Using SSH
- Data Encryption: SSH encrypts all data transmitted between devices, ensuring that sensitive information remains confidential.
- Authentication: SSH uses public key authentication to verify the identity of devices and users, preventing unauthorized access.
- Secure Communication: SSH ensures that all communication between devices is secure, protecting against eavesdropping and data tampering.
Best IoT Devices for SSH Access
When it comes to selecting the best IoT devices for SSH access, several options stand out due to their robust security features and ease of use. Below are some of the top IoT devices that offer SSH access:
Raspberry Pi
Raspberry Pi is a popular choice for IoT projects due to its affordability and versatility. It supports SSH access out of the box, making it easy to manage and configure remotely. With a wide range of accessories and software support, Raspberry Pi is an excellent option for both beginners and professionals.
ESP32
ESP32 is a powerful microcontroller designed for IoT applications. It supports SSH access through third-party firmware, allowing users to securely manage their devices remotely. ESP32 is known for its low power consumption and high performance, making it ideal for battery-powered IoT devices.
Arduino MKR WiFi 1010
Arduino MKR WiFi 1010 is a compact IoT board that supports SSH access through firmware modifications. It is designed for projects requiring wireless connectivity and low power consumption. With its easy-to-use interface and extensive community support, Arduino MKR WiFi 1010 is a great choice for IoT enthusiasts.
How to Set Up SSH Access on IoT Devices
Setting up SSH access on IoT devices involves several steps, including enabling SSH, configuring network settings, and securing the connection. Below is a step-by-step guide to help you get started:
Enabling SSH on IoT Devices
- Raspberry Pi: SSH is enabled by default on Raspberry Pi OS. You can verify this by running the command "sudo systemctl status ssh" in the terminal.
- ESP32: SSH can be enabled on ESP32 by installing third-party firmware such as ESPAsyncWebServer.
- Arduino MKR WiFi 1010: SSH can be enabled by modifying the firmware and installing necessary libraries.
Configuring Network Settings
Once SSH is enabled, you need to configure the network settings to ensure secure communication. This includes setting up a static IP address, configuring firewalls, and enabling port forwarding if necessary.
Security Tips for SSH Access
While SSH provides a secure method of accessing IoT devices, there are additional steps you can take to enhance security:
- Use Strong Passwords: Avoid using default passwords and choose strong, unique passwords for your devices.
- Enable Public Key Authentication: Public key authentication adds an extra layer of security by requiring a private key for access.
- Disable Root Login: Disabling root login prevents unauthorized users from gaining administrative access to your devices.
Common Issues and Troubleshooting
When setting up SSH access on IoT devices, you may encounter some common issues. Below are some troubleshooting tips to help you resolve these problems:
Connection Issues
If you're unable to establish an SSH connection, check the following:
- Ensure that the device is connected to the network.
- Verify that SSH is enabled on the device.
- Check the IP address and port number for accuracy.
Authentication Failures
If you receive authentication failures, try the following:
- Double-check your username and password.
- Ensure that public key authentication is properly configured.
- Verify that the device's SSH settings are correct.
Comparison of IoT Devices with SSH Access
When selecting the best IoT device for SSH access, it's important to compare the features and capabilities of different options. Below is a comparison of some popular IoT devices:
| Device | Price | Features | Security |
|---|---|---|---|
| Raspberry Pi | $35 | Powerful processor, extensive software support | Strong SSH support, community-driven security updates |
| ESP32 | $8 | Low power consumption, Wi-Fi and Bluetooth connectivity | Third-party firmware for SSH, customizable security options |
| Arduino MKR WiFi 1010 | $25 | Compact size, built-in Wi-Fi and cryptographic support | Customizable firmware for SSH, secure communication protocols |
Future Trends in IoT and SSH
The future of IoT and SSH is bright, with advancements in technology driving innovation in both areas. Some key trends to watch include:
Quantum-Resistant Encryption
As quantum computing becomes more prevalent, there is a growing need for quantum-resistant encryption methods. SSH protocols are expected to evolve to incorporate these advanced encryption techniques, ensuring long-term security for IoT devices.
Edge Computing
Edge computing is becoming increasingly important in IoT applications, allowing devices to process data locally rather than relying on cloud-based solutions. This reduces latency and improves security, making it an ideal complement to SSH access.
Conclusion and Call to Action
In conclusion, selecting the best IoT device for SSH access requires careful consideration of your needs and the capabilities of available devices. By understanding the importance of SSH and following best practices for setup and security, you can ensure that your IoT devices remain protected and efficient.
We encourage you to leave a comment below sharing your experiences with IoT devices and SSH access. If you found this article helpful, please consider sharing it with others who may benefit from the information. For more insights into IoT and related technologies, explore our other articles on the site.