In today's digital landscape, SSH key management solution has become an essential aspect of cybersecurity. Organizations are increasingly relying on secure communication channels to protect sensitive data and ensure seamless operations. However, managing SSH keys effectively can be challenging without the right strategies and tools in place.
SSH (Secure Shell) keys are cryptographic keys used to authenticate users and systems, replacing traditional password-based authentication. While they offer stronger security, mismanagement of SSH keys can lead to significant vulnerabilities. This guide will delve into the importance of SSH key management, best practices, and advanced solutions to help you secure your network infrastructure.
By understanding the principles of SSH key management, organizations can enhance their security posture and reduce risks associated with unauthorized access. Whether you're a cybersecurity professional or an IT administrator, this comprehensive guide will provide actionable insights and expert advice to ensure your SSH keys are managed effectively.
Read also:Nate Robinsons Sports Career A Journey Of Perseverance And Passion
Table of Contents
- Introduction to SSH Key Management Solution
- Why SSH Key Management Matters
- Understanding the Basics of SSH Keys
- Risks of Poor SSH Key Management
- Best Practices for SSH Key Management
- Top Tools for SSH Key Management
- Strategies for Effective SSH Key Management
- Automation in SSH Key Management
- Compliance and Regulatory Considerations
- The Future of SSH Key Management
Introduction to SSH Key Management Solution
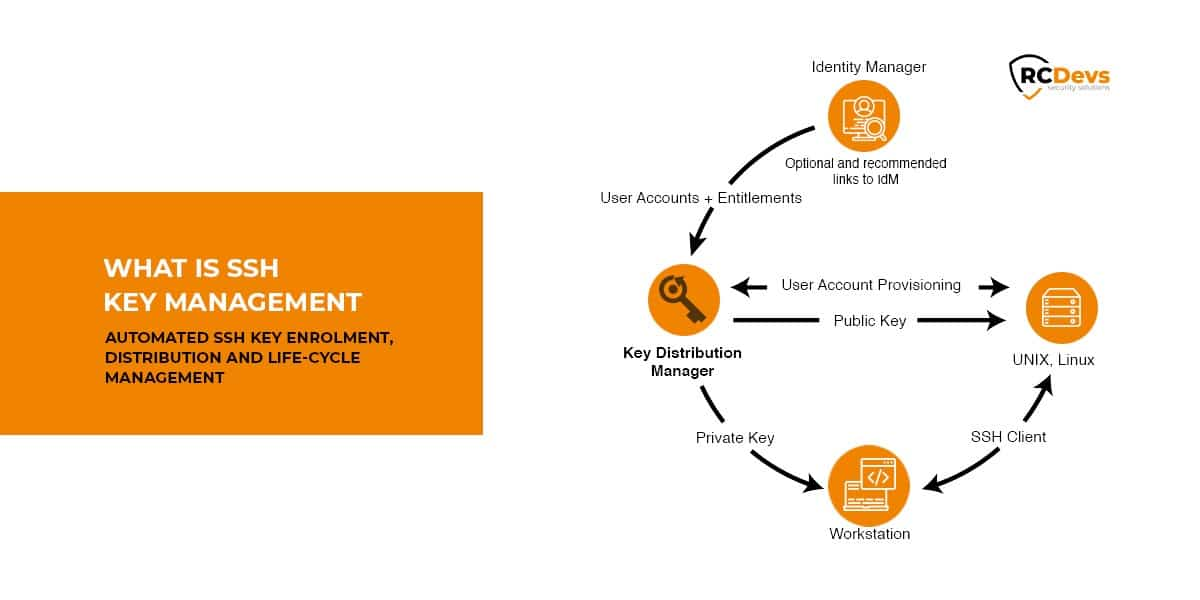
SSH key management solution involves the processes and tools used to create, distribute, monitor, and retire SSH keys within an organization. Proper management ensures that only authorized users and systems have access to critical resources, reducing the risk of security breaches.
SSH keys are widely used across industries for secure communication between servers, automated processes, and remote access. However, without a structured approach to managing these keys, organizations may face challenges such as key sprawl, unauthorized access, and compliance violations.
Effective SSH key management solutions provide centralized control, automation, and visibility into key usage, ensuring that security policies are consistently enforced. In this section, we will explore the key components of an SSH key management solution and its role in modern cybersecurity strategies.
Why SSH Key Management Matters
SSH keys are often referred to as the "keys to the kingdom" in IT environments due to their critical role in securing network infrastructure. However, many organizations underestimate the importance of managing these keys effectively, leading to potential security risks.
Key Security Challenges
Here are some of the primary reasons why SSH key management matters:
- Unauthorized Access: Mismanaged SSH keys can grant unauthorized users access to sensitive systems and data.
- Key Sprawl: As organizations grow, the number of SSH keys increases exponentially, making it difficult to track and manage them.
- Compliance Violations: Failure to manage SSH keys properly can result in non-compliance with industry regulations such as HIPAA, PCI-DSS, and GDPR.
- Increased Attack Surface: Poorly managed SSH keys can create vulnerabilities that attackers can exploit to gain access to critical systems.
By implementing robust SSH key management practices, organizations can mitigate these risks and ensure the security of their IT infrastructure.
Read also:Lea Dellecave The Remarkable Journey Of A Tech Entrepreneur Redefining Industries
Understanding the Basics of SSH Keys
Before diving into SSH key management solutions, it's important to understand the basics of SSH keys and how they work. SSH keys are cryptographic keys that provide a secure method of authentication between systems and users.
Types of SSH Keys
There are two main types of SSH keys:
- Public Key: The public key is shared with other systems or users to establish a secure connection.
- Private Key: The private key is kept secret and used to authenticate the user or system initiating the connection.
When a user attempts to connect to a server using SSH, the server verifies the public key against the private key to ensure the authenticity of the connection. This process eliminates the need for password-based authentication, providing stronger security and convenience.
Risks of Poor SSH Key Management
Poor SSH key management can lead to significant security risks, making it essential for organizations to address this issue proactively. Some of the key risks associated with mismanaged SSH keys include:
Unauthorized Access
When SSH keys are not properly managed, they can fall into the wrong hands, granting unauthorized users access to sensitive systems and data. This can result in data breaches, financial losses, and reputational damage.
Key Sprawl
As organizations grow, the number of SSH keys in use can increase rapidly, leading to key sprawl. Without proper management, it becomes difficult to track and revoke keys, increasing the risk of unauthorized access.
Compliance Violations
Many industries have strict regulations regarding data security and access control. Failure to manage SSH keys effectively can result in non-compliance, leading to fines and legal consequences.
By implementing comprehensive SSH key management solutions, organizations can address these risks and ensure the security of their IT infrastructure.
Best Practices for SSH Key Management
Effective SSH key management requires a combination of best practices, tools, and processes. Here are some key strategies to help you manage SSH keys effectively:
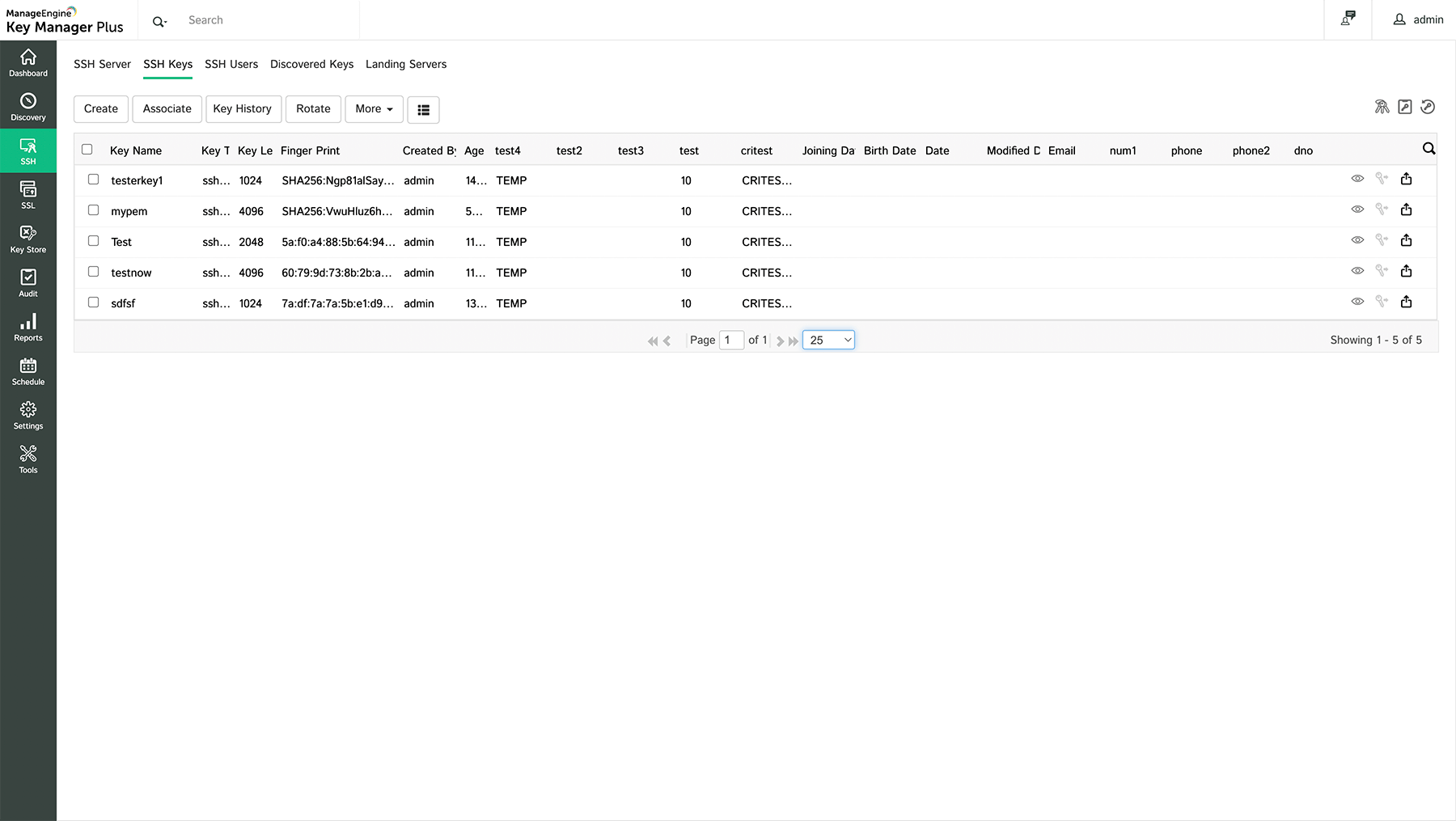
Centralized Key Management
Implement a centralized system for managing SSH keys, ensuring that all keys are stored in a secure location and can be easily tracked and monitored.
Regular Audits
Conduct regular audits of SSH keys to identify and revoke unused or outdated keys. This helps reduce the attack surface and ensures that only authorized keys are in use.
Access Control
Enforce strict access control policies for SSH keys, ensuring that only authorized personnel have access to them. Use role-based access control (RBAC) to limit access based on job responsibilities.
Key Rotation
Regularly rotate SSH keys to reduce the risk of compromise. Establish a schedule for key rotation and ensure that all relevant parties are aware of the process.
By following these best practices, organizations can enhance their SSH key management processes and improve overall security.
Top Tools for SSH Key Management
Several tools are available to help organizations manage SSH keys effectively. These tools provide features such as centralized key management, automation, and monitoring to simplify the SSH key management process.
Popular SSH Key Management Tools
- HashiCorp Vault: A popular tool for managing secrets, including SSH keys, with features such as encryption, access control, and auditing.
- Thycotic Secret Server: A comprehensive solution for managing SSH keys and other secrets, offering features such as centralized storage, access control, and reporting.
- CyberArk Privileged Access Security Solution: A robust solution for managing SSH keys and privileged accounts, providing features such as automated key rotation, access control, and compliance reporting.
When selecting an SSH key management tool, consider factors such as scalability, ease of use, and integration with existing systems. Choose a tool that aligns with your organization's needs and security requirements.
Strategies for Effective SSH Key Management
To ensure the effectiveness of your SSH key management solution, it's important to implement the right strategies. Here are some key strategies to consider:
Policy Development
Develop clear policies and procedures for SSH key management, outlining roles and responsibilities, key lifecycle management, and access control.
Education and Training
Provide education and training to employees on the importance of SSH key management and best practices for secure key usage. This helps foster a culture of security awareness within the organization.
Monitoring and Reporting
Implement monitoring and reporting mechanisms to track SSH key usage and detect potential security issues. Use analytics to identify trends and areas for improvement.
By implementing these strategies, organizations can enhance their SSH key management processes and improve overall security.
Automation in SSH Key Management
Automation plays a critical role in SSH key management, helping organizations streamline processes and reduce the risk of human error. By automating tasks such as key generation, distribution, and rotation, organizations can ensure consistent and secure key management practices.
Benefits of Automation
- Increased Efficiency: Automation reduces the time and effort required to manage SSH keys, allowing IT teams to focus on other critical tasks.
- Improved Security: Automation ensures that security policies are consistently enforced, reducing the risk of misconfigurations and vulnerabilities.
- Enhanced Compliance: Automation helps organizations meet compliance requirements by providing detailed logs and reports of key management activities.
When implementing automation in SSH key management, it's important to choose the right tools and technologies that align with your organization's needs and security requirements.
Compliance and Regulatory Considerations
SSH key management is a critical component of compliance with industry regulations such as HIPAA, PCI-DSS, and GDPR. Organizations must ensure that their SSH key management practices align with these regulations to avoid fines and legal consequences.
Key Compliance Requirements
- HIPAA: Requires secure access control and encryption for protected health information (PHI).
- PCI-DSS: Mandates strong access control measures for cardholder data.
- GDPR: Requires organizations to implement appropriate technical and organizational measures to protect personal data.
By addressing compliance requirements in SSH key management, organizations can ensure the security of sensitive data and maintain regulatory compliance.
The Future of SSH Key Management
As technology continues to evolve, the future of SSH key management will likely involve advancements in automation, artificial intelligence, and machine learning. These technologies will help organizations manage SSH keys more efficiently and securely, reducing the risk of security breaches and compliance violations.
Additionally, the rise of cloud computing and DevOps practices will drive the need for more flexible and scalable SSH key management solutions. Organizations must stay ahead of these trends to ensure the security of their IT infrastructure and maintain a competitive edge in the digital landscape.
Conclusion
In conclusion, SSH key management solution is a critical aspect of cybersecurity that requires careful attention and planning. By understanding the basics of SSH keys, implementing best practices, and leveraging the right tools and technologies, organizations can enhance their security posture and reduce risks associated with unauthorized access.
We encourage you to take action by implementing the strategies and solutions discussed in this guide. Share your thoughts and experiences in the comments section below, and don't forget to explore other articles on our site for more insights into cybersecurity and IT management.