In the ever-evolving world of technology, securely connecting remote IoT devices through peer-to-peer (P2P) networks on a Raspberry Pi has become a critical skill for developers and tech enthusiasts alike. As more devices are connected to the internet, ensuring secure communication between them is paramount. This guide will provide you with step-by-step instructions on how to securely connect remote IoT devices using P2P architecture on a Raspberry Pi, ensuring your data remains protected.
Whether you're building a smart home system, a remote monitoring solution, or any other IoT-based project, understanding how to create a secure connection is essential. This article will delve into the intricacies of IoT security, P2P networking, and Raspberry Pi configurations, empowering you to implement robust solutions.
By the end of this guide, you will have a solid understanding of the tools, techniques, and best practices required to establish a secure remote IoT P2P connection using a Raspberry Pi. Let's dive in!
Read also:27 Dresses Actor A Comprehensive Look At The Star Behind The Suit
Table of Contents
- Introduction to IoT and P2P Networking
- Raspberry Pi Overview and Its Role in IoT
- Why Secure Connections Are Crucial
- Step-by-Step Setup for Secure P2P IoT
- Securing IoT Devices
- Tools and Software for Implementation
- Troubleshooting Tips for Common Issues
- Best Practices for Secure IoT Connections
- Future Trends in IoT Security
- Conclusion and Next Steps
Introduction to IoT and P2P Networking
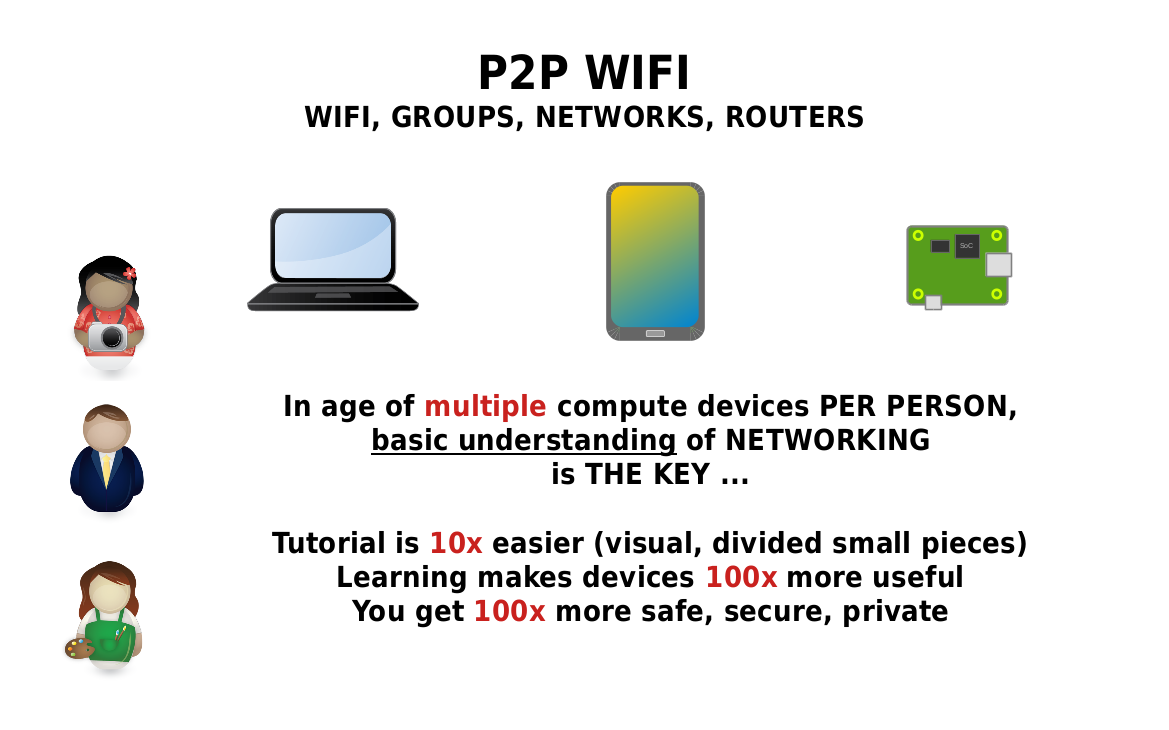
The Internet of Things (IoT) refers to the network of interconnected devices that communicate and exchange data over the internet. Peer-to-peer (P2P) networking is a decentralized communication model where devices connect directly without relying on centralized servers. This approach offers several advantages, including reduced latency, enhanced scalability, and improved resilience against failures.
Benefits of P2P Networking in IoT
P2P networking in IoT provides several benefits:
- Reduced Latency: Direct communication between devices minimizes delays.
- Improved Scalability: Devices can handle more connections without overloading a central server.
- Enhanced Security: Decentralized networks make it harder for attackers to compromise the entire system.
Raspberry Pi Overview and Its Role in IoT
The Raspberry Pi is a compact, affordable single-board computer that has become a staple in the world of IoT development. Its versatility, low power consumption, and ease of use make it an ideal platform for building IoT projects. By leveraging the Raspberry Pi, developers can create robust, secure, and scalable IoT solutions.
Key Features of Raspberry Pi
- Multiple GPIO pins for interfacing with sensors and actuators.
- Support for various operating systems, including Linux-based distributions.
- Built-in Wi-Fi and Ethernet capabilities for seamless connectivity.
Why Secure Connections Are Crucial
Security is a top priority when connecting IoT devices remotely. Without proper safeguards, sensitive data can be intercepted, leading to privacy breaches and potential financial losses. Establishing secure connections ensures that your data remains confidential, intact, and available only to authorized parties.
Common IoT Security Threats
- Data Breaches: Unauthorized access to sensitive information.
- Denial of Service (DoS) Attacks: Overloading devices with traffic to disrupt operations.
- Malware Infections: Compromising devices with malicious software.
Step-by-Step Setup for Secure P2P IoT
Setting up a secure P2P IoT connection on a Raspberry Pi involves several key steps. Below is a comprehensive guide to help you get started:
Step 1: Prepare Your Raspberry Pi
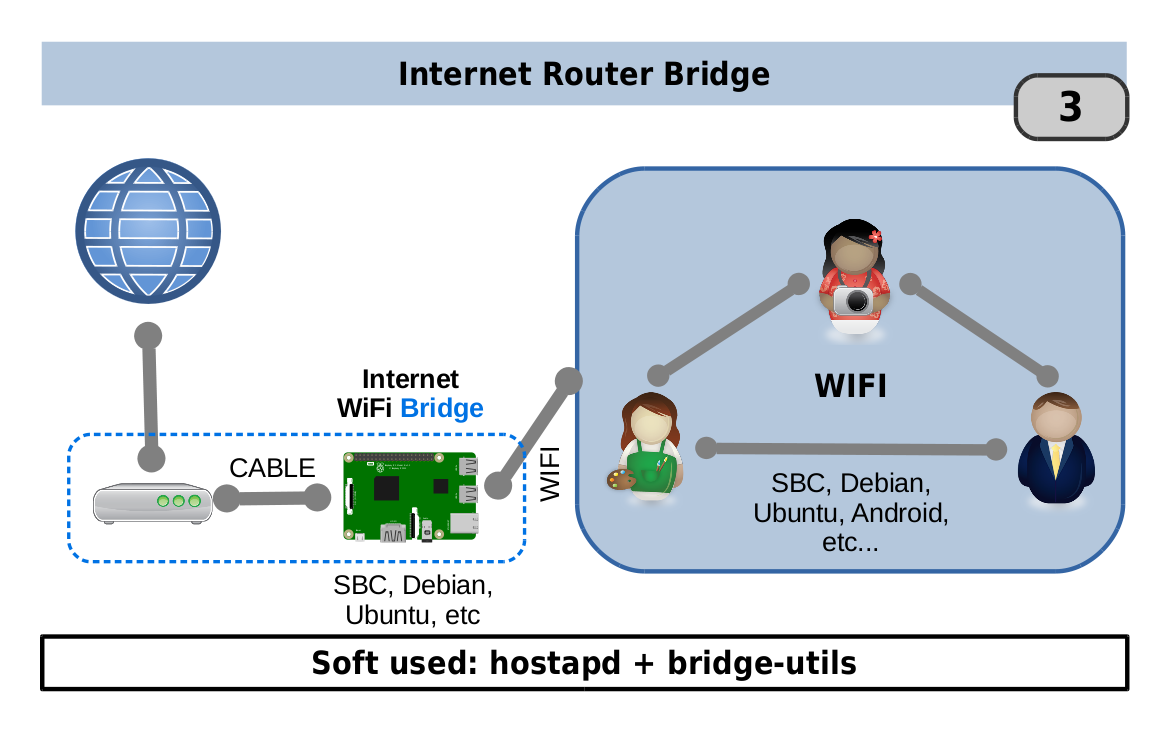
Begin by preparing your Raspberry Pi. Install the latest version of Raspberry Pi OS and ensure all software is up to date. Configure the network settings to allow for remote access.
Read also:51 Celebrities Discovering The Worlds Short But Talented Stars
Step 2: Install Necessary Software
Install the required software for P2P communication, such as OpenVPN or WireGuard, to establish a secure tunnel between devices. These tools provide robust encryption and authentication mechanisms.
Step 3: Configure Security Settings
Configure security settings to protect your devices from unauthorized access. Use strong passwords, enable two-factor authentication, and regularly update firmware to address vulnerabilities.
Securing IoT Devices
Securing IoT devices involves implementing multiple layers of protection. From encryption protocols to firewall configurations, each step plays a crucial role in safeguarding your network.
Encryption Protocols
Use encryption protocols like AES (Advanced Encryption Standard) to secure data transmission between devices. Encryption ensures that even if data is intercepted, it remains unreadable without the decryption key.
Tools and Software for Implementation
Several tools and software solutions are available to facilitate the implementation of secure IoT P2P connections:
- WireGuard: A modern VPN solution that provides fast and secure connections.
- OpenSSL: A robust toolkit for implementing SSL/TLS encryption.
- iptables: A powerful firewall utility for controlling network traffic.
Troubleshooting Tips for Common Issues
Encountering issues during setup is common. Below are some troubleshooting tips to help you resolve common problems:
- Check network configurations to ensure proper connectivity.
- Verify software installations and configurations for errors.
- Consult official documentation and community forums for additional support.
Best Practices for Secure IoT Connections
Adhering to best practices is essential for maintaining secure IoT connections:
- Regularly update software and firmware to address vulnerabilities.
- Use strong, unique passwords and enable two-factor authentication.
- Monitor network activity for suspicious behavior and respond promptly to threats.
Future Trends in IoT Security
The future of IoT security is shaped by emerging technologies and innovations. Blockchain, quantum cryptography, and AI-driven threat detection are just a few examples of advancements that promise to enhance IoT security. Staying informed about these trends will help you stay ahead of potential threats.
Conclusion and Next Steps
In conclusion, securely connecting remote IoT devices through P2P networks on a Raspberry Pi requires a combination of technical expertise, proper tools, and adherence to best practices. By following the steps outlined in this guide, you can establish a robust, secure connection that protects your data and ensures seamless communication between devices.
We invite you to share your thoughts and experiences in the comments section below. Additionally, explore other articles on our site for more insights into IoT and related technologies. Together, let's build a safer, more connected world!
Data Source: National Institute of Standards and Technology (NIST), Raspberry Pi Foundation.