As the Internet of Things (IoT) continues to expand, remote login for IoT devices has become a critical aspect of modern technology. It allows users to access and control their devices from anywhere in the world, opening up endless possibilities for convenience and efficiency. However, with this convenience comes the responsibility of ensuring security and privacy. Understanding how to securely log in to IoT devices remotely is essential for both individuals and businesses.
The ability to manage IoT devices remotely is transforming industries, from smart homes to industrial automation. Whether you're a homeowner wanting to monitor your security cameras or a business owner managing a network of sensors, remote access is a powerful tool. However, the growing number of cyber threats demands that users take the necessary precautions to protect their devices and data.
In this comprehensive guide, we will explore everything you need to know about remote login for IoT devices. From understanding the basics to implementing best practices for security, this article will equip you with the knowledge to confidently manage your IoT devices remotely. Let's dive in!
Read also:Real Housewives Of Beverly Hills Ages 2024 The Ultimate Guide To The Stars
Table of Contents
- What is Remote Login for IoT Devices?
- The Importance of Remote Login for IoT Devices
- Security Challenges in Remote IoT Login
- Best Practices for Secure Remote IoT Login
- Tools and Software for Remote IoT Login
- Authentication Methods for IoT Devices
- Network Security for IoT Remote Access
- Case Studies: Real-World Examples of Remote IoT Login
- Future Trends in Remote IoT Login
- Conclusion and Call to Action
What is Remote Login for IoT Devices?
Remote login for IoT devices refers to the ability to access and manage connected devices over the internet from a remote location. IoT devices include a wide range of gadgets such as smart thermostats, security cameras, industrial sensors, and more. With remote login, users can monitor, control, and configure these devices without being physically present.
For example, a homeowner can check their security camera footage while on vacation, or an engineer can troubleshoot a sensor in a remote factory. This capability is made possible through protocols like SSH (Secure Shell), Telnet, and others that facilitate secure communication between devices and users.
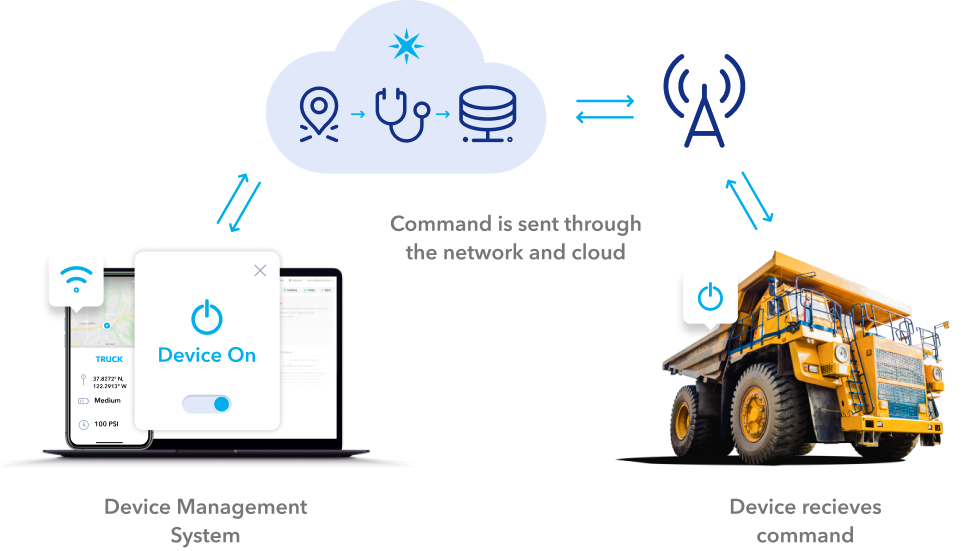
How Does Remote Login Work?
Remote login typically involves the following steps:
- Connection Establishment: The user initiates a connection to the IoT device using a client application or command-line interface.
- Authentication: The user provides credentials, such as a username and password, or uses advanced authentication methods like two-factor authentication (2FA).
- Data Transfer: Once authenticated, the user can send commands, retrieve data, or make configuration changes to the device.
- Session Termination: After completing the task, the user ends the session to ensure security.
The Importance of Remote Login for IoT Devices
Remote login for IoT devices offers numerous benefits that make it an indispensable feature in today's interconnected world. Here are some key reasons why remote login is important:
Increased Efficiency
By enabling users to manage devices remotely, remote login eliminates the need for physical presence, saving time and resources. For instance, IT professionals can troubleshoot network issues from their office instead of traveling to remote locations.
Enhanced Accessibility
IoT devices are often deployed in hard-to-reach areas, such as oil rigs, remote farms, or industrial facilities. Remote login ensures that these devices can still be monitored and managed effectively, regardless of their location.
Read also:Think Like A Man 2 Release Date A Comprehensive Guide To The Films Timeline And Impact
Cost Savings
Reducing the need for on-site visits translates into significant cost savings for businesses. Companies can allocate their resources more efficiently and focus on strategic activities rather than routine maintenance tasks.
Security Challenges in Remote IoT Login
While remote login offers numerous advantages, it also introduces security challenges that must be addressed. Cybercriminals are constantly looking for vulnerabilities to exploit, and IoT devices are prime targets due to their widespread adoption and often inadequate security measures.
Common Security Threats
- Unsecured Connections: Using unencrypted protocols like Telnet can expose sensitive data to interception.
- Weak Passwords: Default or weak passwords are easy targets for brute-force attacks.
- Malware Attacks: IoT devices can be infected with malware, allowing attackers to gain unauthorized access.
- Denial of Service (DoS) Attacks: Attackers can overwhelm IoT devices with traffic, rendering them inaccessible.
Best Practices for Secure Remote IoT Login
To mitigate the security risks associated with remote login for IoT devices, it's crucial to follow best practices. These practices ensure that your devices and data remain protected while still allowing for convenient access.
Use Strong Authentication
Implement strong authentication mechanisms, such as:
- Multi-factor authentication (MFA)
- Biometric authentication
- Certificate-based authentication
Encrypt Communication
Always use encrypted protocols like SSH or HTTPS to secure data transmission between the user and the IoT device. This prevents eavesdropping and data tampering.
Regularly Update Firmware
Keep your IoT devices' firmware up to date with the latest security patches. Manufacturers frequently release updates to address vulnerabilities and improve performance.
Tools and Software for Remote IoT Login
Several tools and software solutions are available to facilitate secure remote login for IoT devices. These tools provide features like encryption, authentication, and session management to enhance security.
Popular Tools
- TeamViewer: A widely used remote access tool that supports IoT devices and offers robust security features.
- SecureCRT: A terminal emulation program that supports SSH and other secure protocols.
- Putty: A free and open-source SSH client that is popular among IT professionals.
Authentication Methods for IoT Devices
Authentication is a critical component of secure remote login for IoT devices. It ensures that only authorized users can access the devices. Here are some common authentication methods:
Password-Based Authentication
While passwords are the most common form of authentication, they can be vulnerable to attacks if not properly managed. Use strong, complex passwords and avoid reusing them across multiple devices.
Biometric Authentication
Biometric authentication uses unique physical characteristics, such as fingerprints or facial recognition, to verify a user's identity. This method is highly secure but may not be suitable for all IoT devices due to hardware limitations.
Network Security for IoT Remote Access
Network security plays a vital role in securing remote login for IoT devices. A secure network infrastructure ensures that devices are protected from unauthorized access and cyber threats.
Firewall Protection
Deploy firewalls to monitor and control incoming and outgoing network traffic. Firewalls can block suspicious activity and prevent unauthorized access to IoT devices.
VLAN Segmentation
Use VLAN segmentation to isolate IoT devices from other network devices. This reduces the risk of lateral movement in case of a breach.
Case Studies: Real-World Examples of Remote IoT Login
Real-world examples demonstrate the practical applications and benefits of remote login for IoT devices. Here are two case studies:
Case Study 1: Smart Home Automation
A homeowner installed smart lighting and security cameras in their house. Using remote login, they can control the lights and monitor the cameras from their smartphone while at work. This setup enhances home security and convenience.
Case Study 2: Industrial IoT
An industrial facility deployed IoT sensors to monitor equipment performance. Engineers can remotely access these sensors to analyze data and perform maintenance tasks, reducing downtime and improving efficiency.
Future Trends in Remote IoT Login
The landscape of remote login for IoT devices is continuously evolving. Emerging technologies and trends are shaping the future of this field. Some notable trends include:
Artificial Intelligence (AI)
AI-powered systems can enhance security by detecting and responding to threats in real time. They can also automate routine tasks, freeing up human resources for more complex activities.
Quantum Computing
Quantum computing has the potential to revolutionize encryption and authentication methods, making them virtually unbreakable. While still in its infancy, this technology holds great promise for the future of IoT security.
Conclusion and Call to Action
Remote login for IoT devices is a powerful feature that offers numerous benefits, including increased efficiency, enhanced accessibility, and cost savings. However, it also introduces security challenges that must be addressed through best practices and secure tools. By following the guidelines outlined in this article, you can confidently manage your IoT devices remotely while ensuring their security and privacy.
We encourage you to implement these practices and explore the tools and technologies discussed here. Share your thoughts and experiences in the comments below, and don't forget to check out our other articles for more insights into IoT and related topics. Together, let's build a safer and more connected world!