In today's digital landscape, the need for secure remote access has never been more critical. With the rise of remote work and the increasing number of cyber threats, ensuring that your Virtual Network Computing (VNC) setup is secure has become a top priority for businesses and individuals alike. But what exactly makes a VNC system "most secure"?
As more users rely on VNC software to remotely access and control computers, the potential risks associated with weak security measures are becoming more apparent. From unauthorized access to data breaches, the consequences of neglecting VNC security can be severe. In this article, we will explore the best practices and tools to ensure that your VNC setup is as secure as possible.
Whether you're a small business owner or an IT professional managing remote access for an enterprise, understanding how to secure your VNC connection is essential. We'll cover everything from encryption methods to advanced authentication techniques, so you can make informed decisions about your remote access setup.
Read also:Daniel B Clark The Visionary Entrepreneur And Philanthropist
Table of Contents
Introduction to Most Secure VNC
Understanding the Basics of VNC
Common Security Threats in VNC
The Role of Encryption in VNC Security
Advanced Authentication Methods
Configuring Firewalls for VNC Security
Read also:February 9 Star Sign Discover The Traits And Secrets Of Aquarius
Top Most Secure VNC Software Options
Best Practices for Most Secure VNC
Troubleshooting Common Security Issues
Introduction to Most Secure VNC
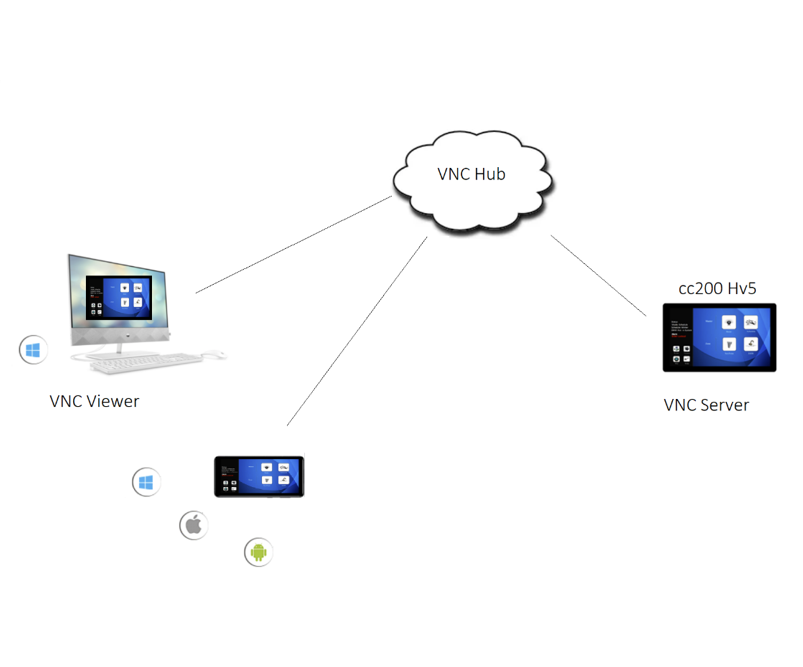
Virtual Network Computing (VNC) has revolutionized the way we interact with computers remotely. It allows users to control a computer from another device, making it an indispensable tool for remote work, IT support, and system administration. However, the convenience of VNC comes with significant security challenges. To ensure your VNC setup is the most secure, you need to implement robust security measures.
Securing your VNC connection involves a combination of encryption, authentication, and network configuration. By following the best practices outlined in this article, you can minimize the risk of unauthorized access and protect sensitive data. Whether you're using VNC for personal or professional purposes, understanding the security implications is crucial.
Understanding the Basics of VNC
Before diving into the security aspects, it's important to understand how VNC works. VNC enables users to remotely control a computer by transmitting keyboard and mouse inputs and displaying the remote screen in real-time. This technology is widely used in various industries for tasks such as:
- Remote system administration
- Technical support
- Collaboration and file sharing
- Remote access to workstations
While VNC offers numerous benefits, its security vulnerabilities can be exploited by cybercriminals. That's why choosing the most secure VNC solution is essential.
Common Security Threats in VNC
Unauthorized Access
One of the most significant risks associated with VNC is unauthorized access. If your VNC server is not properly secured, attackers can gain control of your system, leading to data theft or system compromise.
Data Interception
Without proper encryption, data transmitted over VNC can be intercepted by malicious actors. This can expose sensitive information such as passwords, financial data, and confidential files.
Brute-Force Attacks
Attackers often use brute-force techniques to guess weak passwords and gain access to VNC servers. Implementing strong authentication methods is critical to preventing these attacks.
The Role of Encryption in VNC Security
Encryption is a fundamental aspect of securing your VNC connection. By encrypting data transmitted between the client and server, you can protect it from interception and unauthorized access. Modern VNC solutions offer various encryption protocols, including:
- SSL/TLS
- SSH tunneling
- 128-bit AES encryption
When choosing a VNC software, ensure that it supports strong encryption standards. This will significantly enhance the security of your remote access setup.
Advanced Authentication Methods
Authentication is another critical component of VNC security. Traditional password-based authentication can be vulnerable to brute-force attacks, which is why advanced methods are recommended. Some of the most secure authentication techniques include:
Two-Factor Authentication (2FA)
2FA adds an extra layer of security by requiring users to provide two forms of identification before accessing the VNC server. This could include a password and a one-time code sent to a mobile device.
Biometric Authentication
Biometric methods, such as fingerprint or facial recognition, offer a high level of security and convenience. While not yet universally adopted in VNC solutions, their use is becoming more common.
Public Key Infrastructure (PKI)
PKI uses digital certificates to verify the identity of users and devices. This method is highly secure and widely used in enterprise environments.
Configuring Firewalls for VNC Security
Firewalls play a crucial role in securing your VNC setup by controlling incoming and outgoing network traffic. By configuring your firewall to allow only authorized VNC traffic, you can reduce the risk of unauthorized access. Some best practices for firewall configuration include:
- Restricting VNC access to specific IP addresses
- Using non-standard ports for VNC connections
- Regularly updating firewall rules to address new threats
Proper firewall configuration is essential for ensuring that your VNC setup remains the most secure.
Top Most Secure VNC Software Options
Choosing the right VNC software is critical for maintaining security. Below are some of the most secure VNC solutions available:
TeamViewer
TeamViewer is a popular VNC solution that offers strong encryption, 2FA, and advanced authentication methods. It is widely used in both personal and professional settings.
AnyDesk
AnyDesk provides robust security features, including end-to-end encryption and customizable access controls. Its lightweight design makes it ideal for remote work.
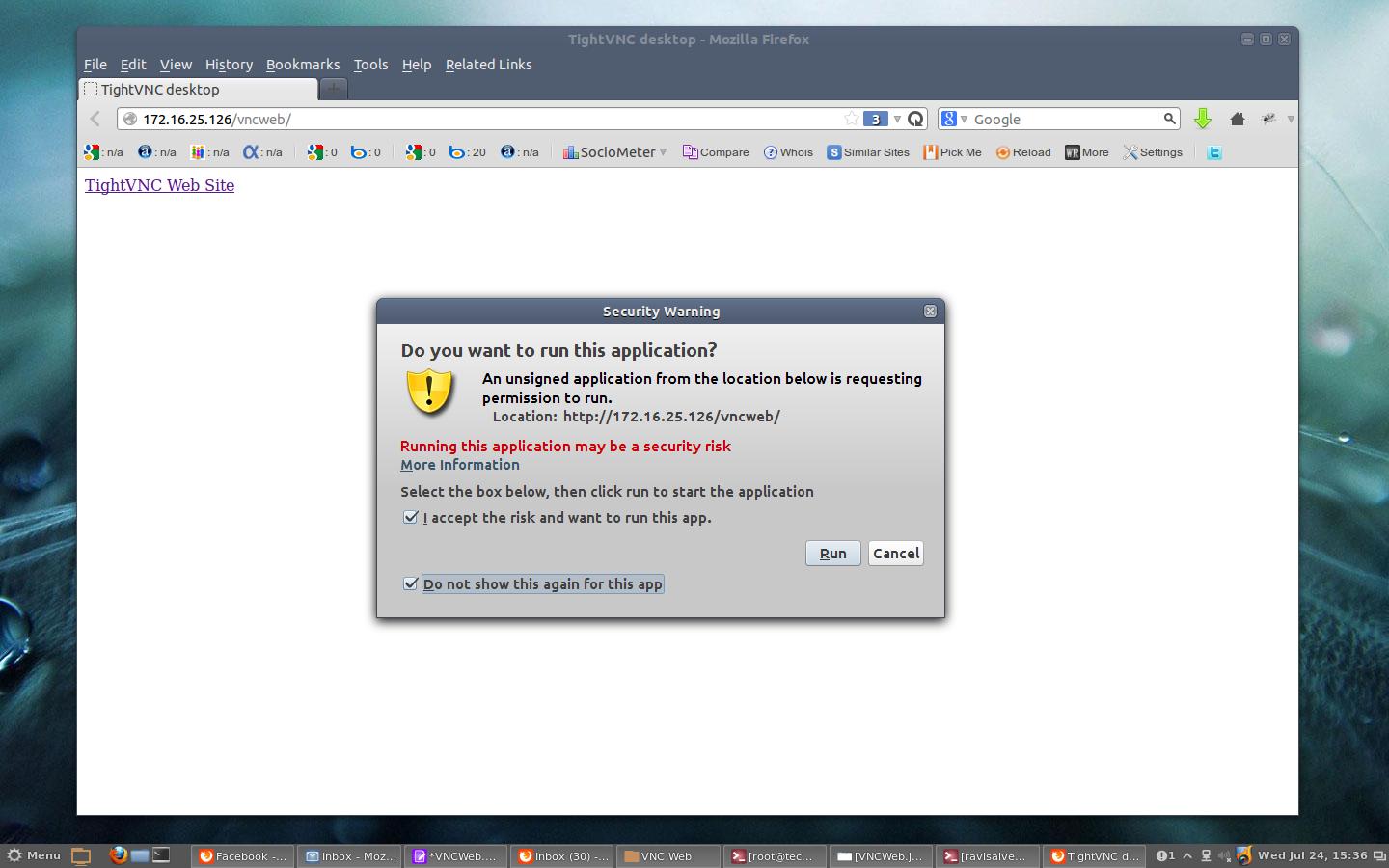
TightVNC
TightVNC is an open-source VNC solution that supports strong encryption and is highly customizable. While it may require more technical expertise to configure, it offers excellent security for power users.
Best Practices for Most Secure VNC
Implementing best practices is essential for ensuring that your VNC setup remains secure. Below are some key recommendations:
- Use strong, unique passwords for VNC access
- Enable encryption for all VNC connections
- Regularly update VNC software to address security vulnerabilities
- Limit VNC access to trusted devices and networks
- Monitor VNC activity for signs of unauthorized access
By following these best practices, you can significantly enhance the security of your VNC setup.
Troubleshooting Common Security Issues
Even with the best security measures in place, issues can arise. Below are some common VNC security problems and how to address them:
Slow Connection Speeds
Slow VNC connections can be caused by network congestion or insufficient encryption. Optimizing your network settings and using compression can help improve performance.
Failed Authentication Attempts
If users are experiencing frequent authentication failures, it may be due to incorrect settings or weak passwords. Reviewing authentication logs and enforcing stronger password policies can resolve this issue.
Future Trends in VNC Security
The field of VNC security is constantly evolving, with new technologies and trends emerging to address emerging threats. Some of the most promising developments include:
- AI-driven threat detection and response
- Quantum encryption for ultra-secure communications
- Zero-trust architecture for enhanced access control
Staying informed about these trends will help you maintain the most secure VNC setup in the future.
Conclusion and Call to Action
In conclusion, securing your VNC setup is essential for protecting sensitive data and preventing unauthorized access. By implementing strong encryption, advanced authentication methods, and proper network configuration, you can ensure that your VNC connection is the most secure possible.
We encourage you to take action by reviewing your current VNC setup and implementing the best practices outlined in this article. Don't forget to share this article with others who may benefit from it and explore our other resources for more information on cybersecurity.