The Internet of Things (IoT) has revolutionized the way we interact with devices, enabling seamless connectivity and remote access. However, ensuring secure and efficient remote access to IoT devices on AWS can be challenging for businesses and developers alike. This article dives deep into the world of IoT device remote access on AWS, offering actionable insights and expert guidance to help you leverage this powerful technology.
As IoT continues to expand, the demand for secure and scalable solutions for managing and accessing devices remotely has never been higher. AWS provides a robust platform for building and deploying IoT applications, empowering users to connect, monitor, and control devices from anywhere in the world.
In this comprehensive guide, we will explore the nuances of IoT device remote access on AWS, covering everything from setup and configuration to best practices and security considerations. Whether you're a seasoned developer or just starting your IoT journey, this article will equip you with the knowledge you need to succeed.
Read also:Dracula 2000 Actors Unveiling The Talented Cast Behind The Classic Vampire Tale
Table of Contents
- Introduction to IoT and Remote Access
- AWS IoT Core: The Backbone of IoT Solutions
- Setting Up IoT Device Remote Access on AWS
- Security Considerations for IoT Device Remote Access
- Scaling IoT Solutions on AWS
- Cost Optimization for IoT Deployments
- Best Practices for IoT Device Remote Access
- Real-World Applications of IoT Device Remote Access
- Troubleshooting Common Issues in IoT Remote Access
- Future Trends in IoT Device Remote Access
Introduction to IoT and Remote Access
IoT refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data and interact with their environment. Remote access is a critical component of IoT, allowing users to interact with devices from any location via the internet.
Remote access to IoT devices on AWS enables businesses to monitor and control equipment in real-time, improving operational efficiency and reducing downtime. This capability is particularly valuable for industries such as manufacturing, healthcare, and agriculture, where continuous monitoring and quick response times are essential.
Key benefits of IoT device remote access on AWS include:
- Enhanced scalability and flexibility
- Improved data security and privacy
- Cost-effective management of IoT deployments
AWS IoT Core: The Backbone of IoT Solutions
AWS IoT Core is a managed cloud service that allows connected devices to securely interact with cloud applications and other devices. It serves as the foundation for building IoT solutions, enabling seamless communication between devices and the cloud.
Features of AWS IoT Core
AWS IoT Core offers a range of features that make it an ideal choice for IoT device remote access:
- Device Gateway: Facilitates secure and reliable communication between devices and the cloud
- Rules Engine: Automates data processing and routing based on predefined rules
- Device Shadow: Maintains a synchronized copy of device state, even when the device is offline
By leveraging AWS IoT Core, businesses can build scalable and secure IoT solutions tailored to their specific needs.
Read also:Debbie Does Dallas Actors A Comprehensive Look At The Iconic Films Cast
Setting Up IoT Device Remote Access on AWS
Setting up IoT device remote access on AWS involves several key steps, including provisioning devices, configuring security settings, and establishing communication protocols. Below is a step-by-step guide to help you get started:
Step 1: Provision IoT Devices
Provisioning involves registering devices with AWS IoT Core and assigning them unique identities. This ensures that each device can be securely authenticated and authorized to access the cloud.
Step 2: Configure Security Settings
Security is paramount when it comes to IoT device remote access. Configure security settings such as certificates, policies, and roles to ensure that only authorized users and devices can access the system.
Step 3: Establish Communication Protocols
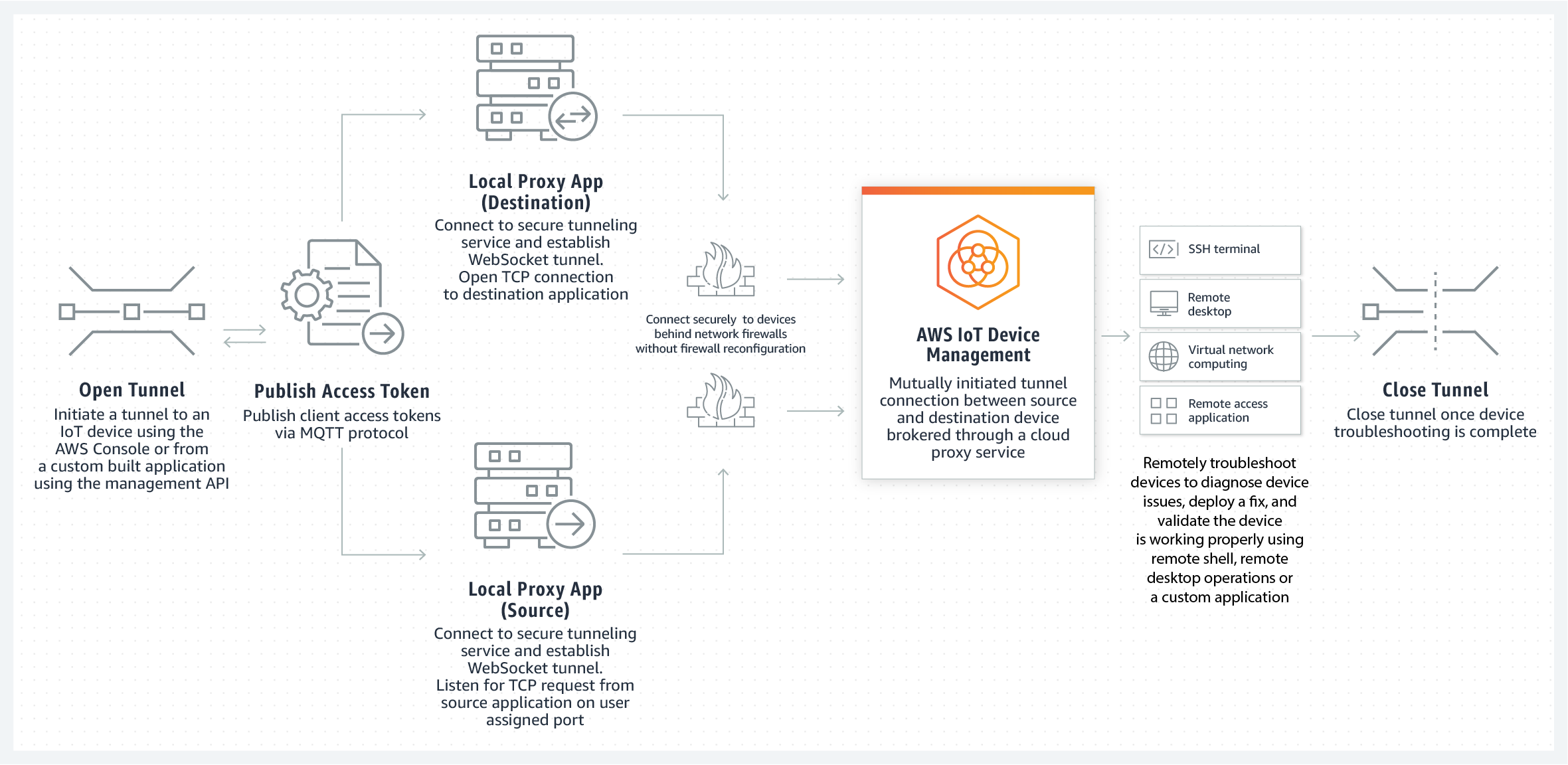
Choose the appropriate communication protocol for your IoT deployment, such as MQTT, HTTP, or WebSockets. AWS IoT Core supports multiple protocols, making it easy to integrate with existing systems.
Security Considerations for IoT Device Remote Access
Security is a critical concern when implementing IoT device remote access on AWS. Below are some best practices to ensure the security of your IoT deployment:
- Use strong authentication mechanisms, such as X.509 certificates
- Implement encryption for data in transit and at rest
- Regularly update firmware and software to address vulnerabilities
By following these guidelines, you can minimize the risk of unauthorized access and protect sensitive data.
Scaling IoT Solutions on AWS
As your IoT deployment grows, it's essential to ensure that your system can scale to meet increasing demands. AWS provides several tools and services to help you scale your IoT solutions effectively:
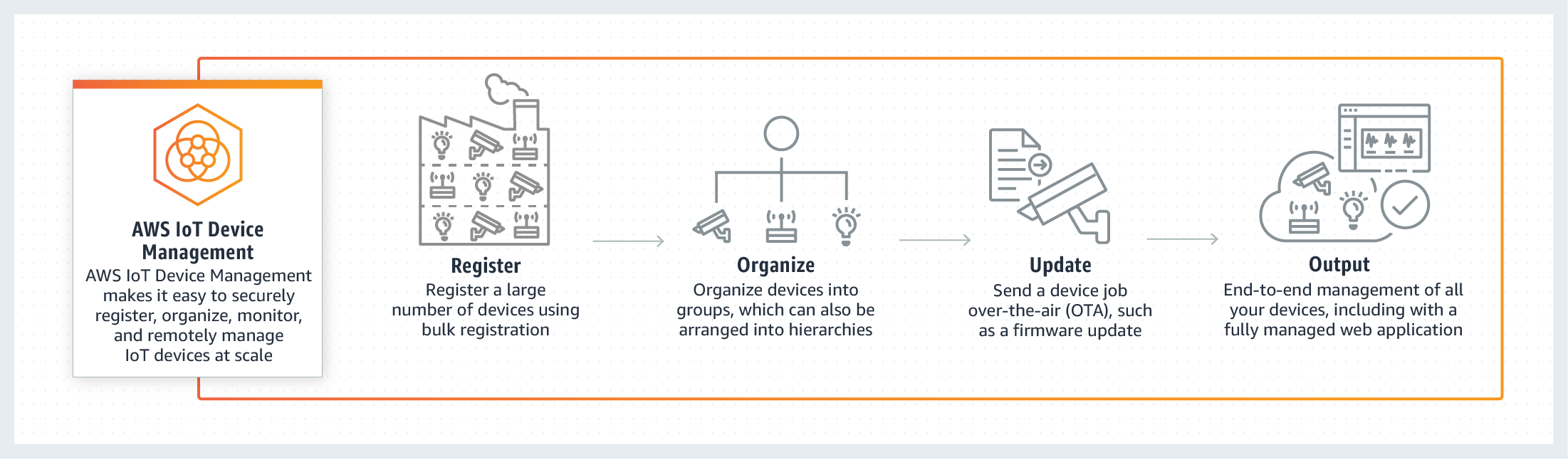
- AWS IoT Device Management: Simplifies the management of large fleets of devices
- AWS IoT Analytics: Enables advanced data processing and analysis
- AWS Lambda: Allows you to run code in response to IoT events without provisioning servers
By leveraging these tools, you can build scalable and resilient IoT solutions that meet the needs of your business.
Cost Optimization for IoT Deployments
Optimizing costs is crucial for ensuring the long-term viability of your IoT deployment. Below are some strategies to help you reduce costs while maintaining performance:
- Utilize AWS Free Tier for initial development and testing
- Monitor usage and adjust resource allocation as needed
- Implement cost-effective storage solutions, such as Amazon S3
By adopting these strategies, you can maximize the value of your IoT investment while minimizing expenses.
Best Practices for IoT Device Remote Access
Implementing best practices is key to achieving success with IoT device remote access on AWS. Below are some recommendations to help you optimize your deployment:
- Design for scalability and flexibility from the outset
- Monitor system performance and address issues proactively
- Document processes and procedures for future reference
By following these best practices, you can ensure that your IoT deployment remains efficient, secure, and cost-effective.
Real-World Applications of IoT Device Remote Access
IoT device remote access on AWS has numerous real-world applications across various industries. Below are some examples:
Manufacturing
Manufacturers use IoT to monitor equipment performance and predict maintenance needs, reducing downtime and improving efficiency.
Healthcare
IoT enables remote patient monitoring, allowing healthcare providers to deliver personalized care and improve patient outcomes.
Agriculture
Farmers leverage IoT to monitor soil conditions, weather patterns, and crop health, optimizing resource use and increasing yields.
Troubleshooting Common Issues in IoT Remote Access
Even with careful planning, issues can arise during IoT device remote access deployments. Below are some common problems and their solutions:
- Connection Issues: Verify network settings and ensure proper device configuration
- Authentication Failures: Check certificates and policies to ensure proper authorization
- Data Loss: Implement redundancy and backup solutions to prevent data loss
By addressing these issues promptly, you can maintain the reliability and performance of your IoT deployment.
Future Trends in IoT Device Remote Access
The future of IoT device remote access on AWS looks promising, with several emerging trends set to shape the industry:
- Edge computing: Enables real-time processing and decision-making at the edge of the network
- 5G connectivity: Provides faster and more reliable communication for IoT devices
- AI and machine learning: Enhances data analysis and automation capabilities
By staying informed about these trends, you can position your business for success in the evolving IoT landscape.
Conclusion
In conclusion, IoT device remote access on AWS offers businesses a powerful tool for managing and interacting with connected devices. By following the guidelines outlined in this article, you can build secure, scalable, and cost-effective IoT solutions that meet the needs of your organization.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore our other articles for more insights into IoT and related technologies. Together, let's harness the potential of IoT to drive innovation and growth.
Sources: