In the era of the Internet of Things (IoT), securing devices through SSH has become a critical concern for both individuals and organizations. The rise of IoT has brought immense convenience, but it has also introduced new security challenges. Understanding the differences between IoT SSH and traditional SSH is essential to safeguard your connected devices.
As the number of IoT devices continues to grow exponentially, ensuring their security is no longer optional but a necessity. In this article, we will explore how IoT SSH differs from traditional SSH, the benefits and limitations of each, and strategies to enhance security in an interconnected world.
This guide aims to provide actionable insights into securing IoT devices using SSH protocols. By the end of this article, you will have a comprehensive understanding of IoT SSH vs SSH and how to implement best practices to protect your network and data.
Read also:Rikki H2o Actress A Comprehensive Look Into Her Career And Life
Table of Contents
- Introduction to SSH
- IoT Overview
- IoT SSH Definition
- SSH Definition
- Key Differences Between IoT SSH and SSH
- Security Benefits of IoT SSH vs SSH
- Limitations and Challenges
- Best Practices for Securing IoT Devices with SSH
- Future Trends in IoT SSH and SSH
- Conclusion
Introduction to SSH
Secure Shell (SSH) is a cryptographic network protocol designed to secure data communication, remote shell services, and other secure network services between computers. It provides a secure channel over an unsecured network by encrypting data and ensuring integrity.
SSH is widely used in IT environments to access remote servers, manage network infrastructure, and transfer files securely. Its primary function is to authenticate users and encrypt data, making it a cornerstone of modern cybersecurity practices.
IoT Overview
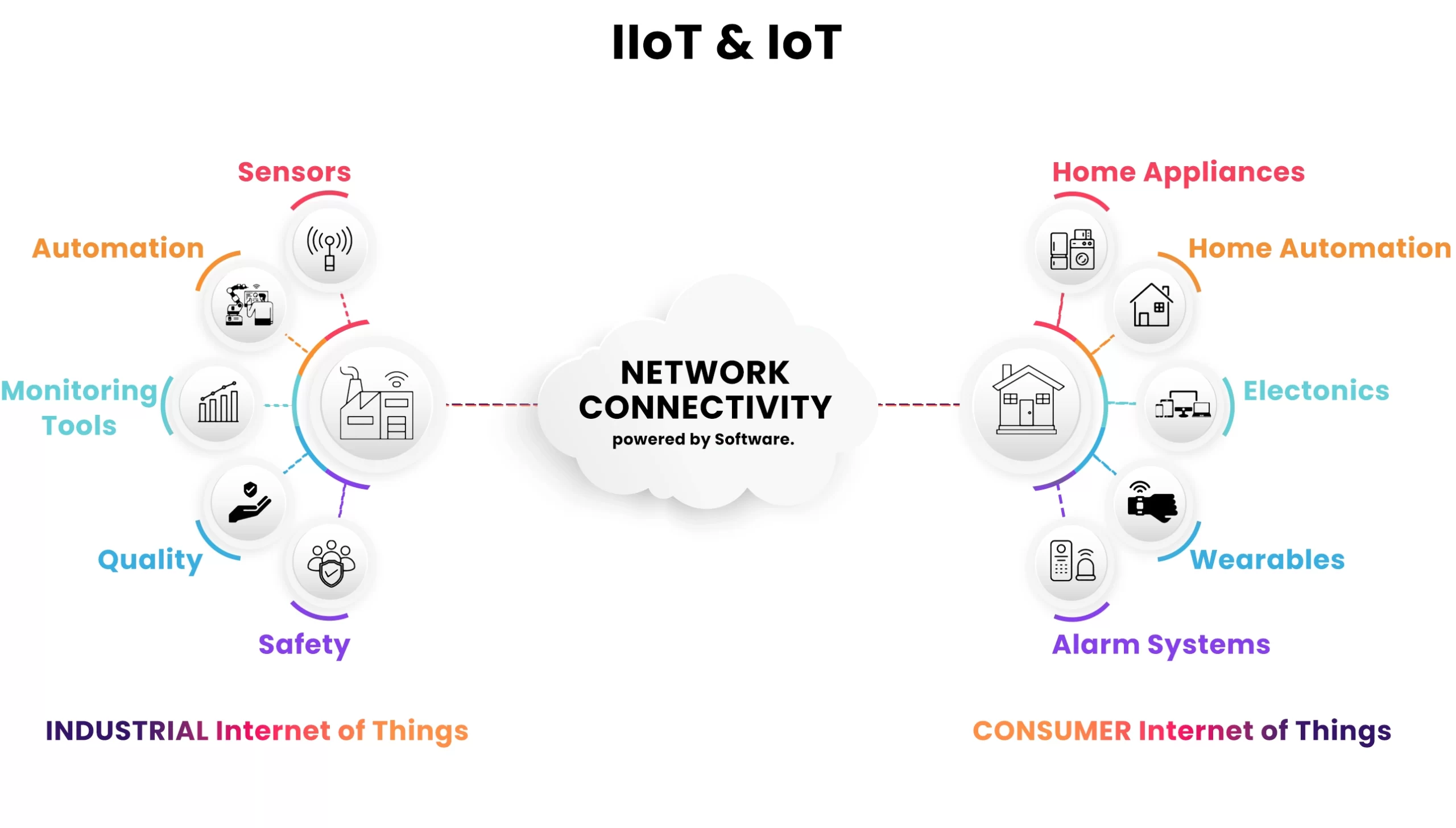
The Internet of Things (IoT) refers to the network of physical devices, vehicles, home appliances, and other items embedded with sensors, software, and connectivity that enable them to exchange data. IoT devices range from smart thermostats and fitness trackers to industrial machinery and autonomous vehicles.
The global IoT market is expected to reach $1.5 trillion by 2030, according to Statista. This rapid growth highlights the importance of securing IoT devices, as they often lack the robust security features found in traditional computing environments.
IoT SSH Definition
What is IoT SSH?
IoT SSH refers to the application of SSH protocols specifically tailored for securing IoT devices. These devices often have limited processing power and memory, which poses unique challenges for implementing robust security measures.
IoT SSH is designed to address these limitations by optimizing encryption algorithms and reducing resource consumption while maintaining a high level of security. It ensures that even the smallest IoT devices can communicate securely over the internet.
Read also:Gta San Andreas Cast A Comprehensive Guide To The Voices Behind The Characters
SSH Definition
Traditional SSH Explained
Traditional SSH, also known as standard SSH, is a widely used protocol for securing communication between servers and clients in enterprise environments. It provides features such as secure file transfer, remote command execution, and secure tunneling.
SSH operates on port 22 by default and uses asymmetric encryption to establish a secure connection. It supports various authentication methods, including password-based and public key authentication, making it a versatile tool for network administrators.
Key Differences Between IoT SSH and SSH
While both IoT SSH and traditional SSH aim to secure communications, there are significant differences between the two:
- Resource Constraints: IoT devices typically have limited processing power and memory, requiring optimized SSH implementations.
- Scalability: IoT networks often consist of thousands of devices, necessitating scalable solutions that can handle large volumes of connections.
- Automation: IoT SSH often incorporates automated security features, such as device self-enrollment and certificate management, to simplify deployment.
- Interoperability: IoT SSH must work seamlessly with a wide range of devices and protocols, whereas traditional SSH is primarily used in homogeneous environments.
Security Benefits of IoT SSH vs SSH
Enhanced Security Features
IoT SSH offers several security benefits over traditional SSH, including:
- End-to-End Encryption: IoT SSH ensures that all data transmitted between devices is encrypted, preventing unauthorized access.
- Device Authentication: Each IoT device is authenticated before being allowed to communicate with the network, reducing the risk of unauthorized access.
- Real-Time Monitoring: IoT SSH enables real-time monitoring of network activity, allowing administrators to detect and respond to security threats quickly.
Reduced Attack Surface
By implementing IoT SSH, organizations can significantly reduce the attack surface of their IoT networks. This is achieved through features such as:
- Network segmentation
- Regular software updates
- Robust access control policies
Limitations and Challenges
Resource Constraints
One of the primary challenges of implementing IoT SSH is the limited resources available on IoT devices. This can lead to slower connection speeds and increased latency, which may impact performance.
Complexity of Deployment
Deploying IoT SSH across a large network of devices can be complex and time-consuming. Organizations must ensure that all devices are properly configured and updated regularly to maintain security.
Best Practices for Securing IoT Devices with SSH
Use Strong Authentication Methods
Implementing strong authentication methods, such as public key authentication, can significantly enhance the security of IoT devices. Avoid using weak passwords and ensure that all devices are authenticated before being allowed to connect to the network.
Regularly Update Firmware
Keeping IoT device firmware up to date is crucial for maintaining security. Manufacturers frequently release updates that address known vulnerabilities and improve performance.
Monitor Network Activity
Regularly monitoring network activity can help detect and respond to security threats in real time. Use tools such as intrusion detection systems (IDS) and security information and event management (SIEM) solutions to gain visibility into your network.
Future Trends in IoT SSH and SSH
Quantum-Resistant Encryption
As quantum computing continues to evolve, the need for quantum-resistant encryption becomes increasingly important. Both IoT SSH and traditional SSH will need to adapt to these advancements to ensure long-term security.
Artificial Intelligence and Machine Learning
AI and machine learning are expected to play a significant role in enhancing IoT security. These technologies can be used to detect anomalies in network behavior and predict potential security threats before they occur.
Conclusion
In conclusion, understanding the differences between IoT SSH and traditional SSH is essential for securing IoT devices in today's interconnected world. While both protocols offer robust security features, IoT SSH is specifically designed to address the unique challenges posed by resource-constrained devices and large-scale networks.
We encourage readers to implement the best practices outlined in this article to enhance the security of their IoT networks. By staying informed about the latest trends and technologies, you can ensure that your devices remain protected against emerging threats.
Feel free to leave a comment or share this article with others who may benefit from the information. For more insights into cybersecurity and IoT, explore our other articles on the website.