In today's interconnected world, the concept of IoT (Internet of Things) access from anywhere example has become a driving force behind technological innovation and convenience. IoT systems enable devices to communicate seamlessly over the internet, creating a network of smart gadgets that improve efficiency and enhance user experience. As businesses and individuals increasingly adopt IoT technologies, understanding how to leverage these systems for remote access is crucial for staying competitive in the digital age.
The ability to access IoT devices from anywhere is no longer a luxury but a necessity. Whether you're managing smart home appliances, monitoring industrial equipment, or controlling office systems remotely, IoT access from anywhere provides unparalleled flexibility and control. This capability opens up endless possibilities, transforming the way we interact with technology and the world around us.
This article delves into the practical applications, security considerations, and implementation strategies for IoT access from anywhere. By exploring real-world examples and best practices, we aim to provide a comprehensive guide that empowers readers to harness the full potential of IoT technology. Let's dive in and explore how IoT is reshaping the future of connectivity.
Read also:Tara Elders The Rising Star In The Spotlight
Table of Contents
- What is IoT Access from Anywhere?
- Real-World Examples of IoT Access
- Benefits of IoT Access from Anywhere
- Security Considerations for IoT Systems
- Steps to Implement IoT Access
- IoT Protocols and Standards
- Challenges in IoT Deployment
- The Future of IoT Access
- Best Practices for IoT Management
- Conclusion
What is IoT Access from Anywhere?
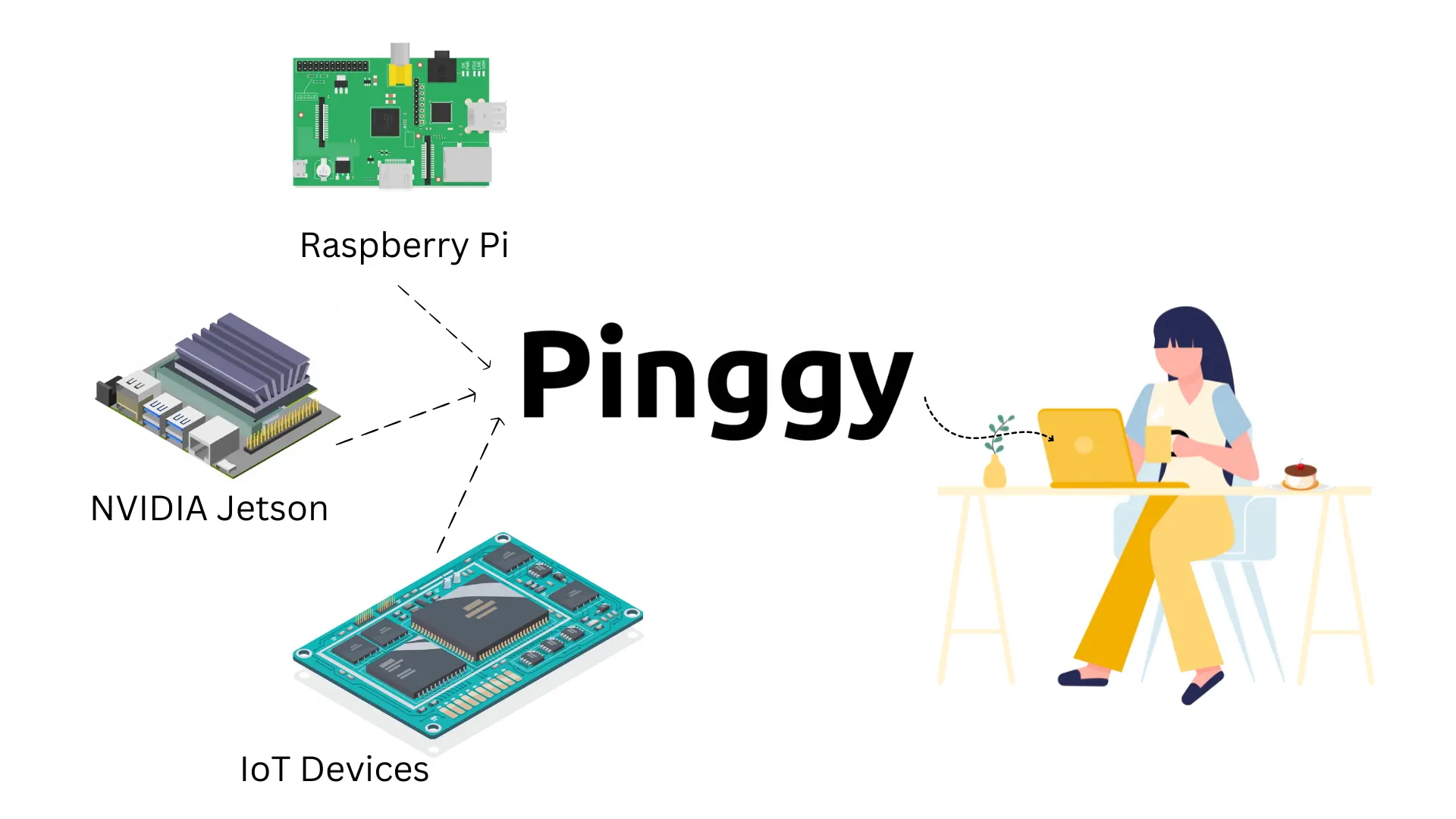
The Internet of Things (IoT) represents a network of interconnected devices that communicate via the internet. IoT access from anywhere refers to the ability to remotely connect to and control these devices regardless of physical location. This functionality relies on cloud computing, secure communication protocols, and user-friendly interfaces to ensure seamless interaction with IoT devices.
Key components of IoT access include:
- Cloud Infrastructure: Provides the backbone for storing and processing data generated by IoT devices.
- Mobile Applications: Enable users to interact with IoT systems through smartphones or tablets.
- Web Interfaces: Allow access via web browsers for greater flexibility.
How IoT Access Works
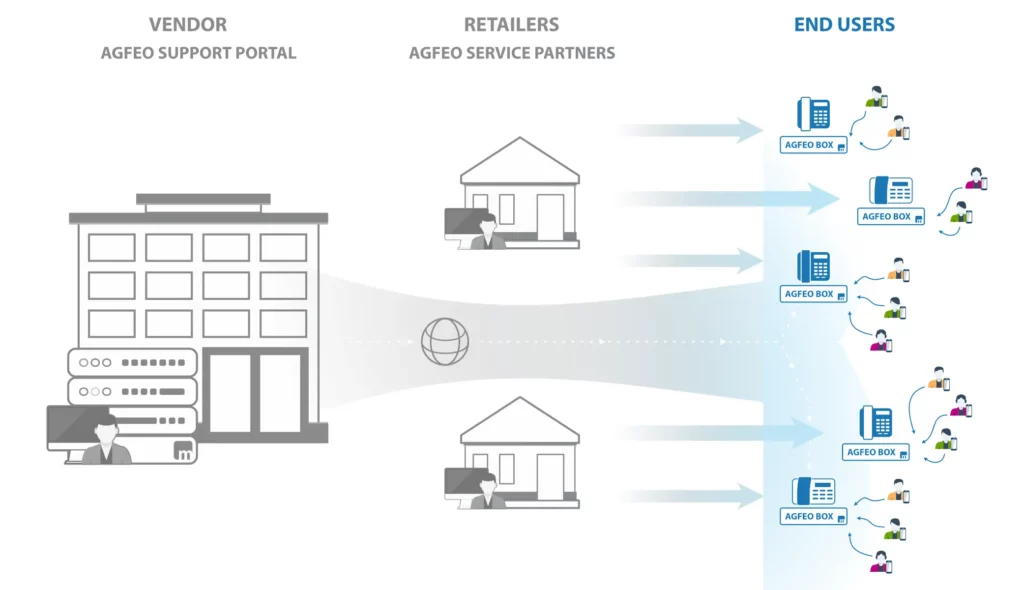
IoT devices typically connect to a central server or cloud platform, which acts as a hub for data exchange. Users can then access this platform remotely using secure authentication methods, ensuring that only authorized individuals can control the devices. This architecture supports real-time monitoring and control, making IoT access from anywhere example both practical and efficient.
Real-World Examples of IoT Access
IoT access from anywhere has found applications across various industries, enhancing productivity and improving quality of life. Below are some examples of how IoT systems are being utilized in real-world scenarios:
Smart Homes
Smart home systems allow users to control lighting, temperature, security cameras, and other appliances remotely. For instance, homeowners can adjust their thermostat settings while on vacation to save energy or check security footage to ensure their property is safe.
Industrial Automation
In manufacturing, IoT access enables engineers to monitor equipment performance and receive alerts about potential issues before they escalate. This proactive approach reduces downtime and optimizes resource utilization.
Read also:I Lost My Queen Too A Comprehensive Guide To Understanding And Overcoming The Emotional Struggles
Healthcare
Remote patient monitoring through IoT devices allows healthcare providers to track vital signs and medication adherence without requiring in-person visits. This is particularly beneficial for patients with chronic conditions who need continuous care.
Benefits of IoT Access from Anywhere
The adoption of IoT access from anywhere example offers numerous advantages, including:
- Increased Efficiency: Streamlines processes by automating tasks and providing real-time data insights.
- Cost Savings: Reduces operational expenses by minimizing manual intervention and optimizing resource usage.
- Enhanced Convenience: Allows users to manage systems remotely, saving time and effort.
- Improved Decision-Making: Provides actionable data to inform strategic decisions.
Security Considerations for IoT Systems
While IoT access from anywhere example offers numerous benefits, it also introduces security risks. Protecting IoT systems from unauthorized access and cyber threats is paramount. Key security measures include:
- Encryption: Ensures that data transmitted between devices and servers remains secure.
- Authentication: Verifies user identities to prevent unauthorized access.
- Regular Updates: Keeps software and firmware up to date to address vulnerabilities.
Best Practices for IoT Security
Implementing robust security protocols is essential for safeguarding IoT systems. Organizations should conduct regular security audits, educate employees about best practices, and collaborate with cybersecurity experts to stay ahead of emerging threats.
Steps to Implement IoT Access
Implementing IoT access from anywhere example requires careful planning and execution. Follow these steps to ensure a successful deployment:
- Define Objectives: Clearly outline the goals and expected outcomes of the IoT system.
- Select Devices: Choose compatible IoT devices that meet your requirements.
- Set Up Connectivity: Establish a reliable network infrastructure to support device communication.
- Develop User Interfaces: Create intuitive apps or web interfaces for user interaction.
- Test and Deploy: Perform thorough testing before rolling out the system to ensure it functions as intended.
IoT Protocols and Standards
Various protocols and standards govern IoT communication, ensuring interoperability and security. Some widely used protocols include:
- MQTT (Message Queuing Telemetry Transport): A lightweight protocol ideal for low-bandwidth environments.
- CoAP (Constrained Application Protocol): Designed for resource-constrained devices and networks.
- HTTP/HTTPS: Standard protocols for web-based communication, often used in conjunction with other IoT protocols.
Challenges in IoT Deployment
Despite its potential, IoT access from anywhere example faces several challenges, such as:
- Interoperability Issues: Ensuring different devices and platforms can communicate effectively.
- Data Privacy Concerns: Protecting sensitive information collected by IoT devices.
- Scalability Limitations: Managing large-scale deployments without compromising performance.
Overcoming Challenges
Addressing these challenges requires collaboration among stakeholders, adherence to industry standards, and investment in research and development. By prioritizing innovation and user-centric design, organizations can overcome obstacles and unlock the full potential of IoT technology.
The Future of IoT Access
As IoT technology continues to evolve, the possibilities for IoT access from anywhere example are limitless. Advancements in artificial intelligence, machine learning, and 5G networks will further enhance connectivity and expand the range of applications. From smart cities to autonomous vehicles, IoT is poised to transform industries and reshape society.
Best Practices for IoT Management
Effective IoT management involves adopting best practices to maximize system performance and security. These include:
- Regular Maintenance: Perform routine checks and updates to maintain system integrity.
- Monitoring and Analytics: Utilize data analytics tools to gain insights and identify trends.
- User Training: Educate users on proper usage and security protocols to prevent misuse.
Conclusion
In conclusion, IoT access from anywhere example represents a powerful tool for enhancing connectivity and improving quality of life. By understanding its benefits, addressing security concerns, and following best practices, organizations and individuals can harness the full potential of IoT technology. We encourage readers to share their experiences and insights in the comments section below. Additionally, feel free to explore other articles on our site for more information on emerging technologies and trends.
Stay connected and embrace the future of IoT access from anywhere!