In today's digital landscape, remote access technology plays a crucial role in enabling productivity and collaboration. One of the most widely used tools for remote access is VNC (Virtual Network Computing). However, many users wonder: Is VNC a secure protocol? This question is vital, as security is paramount when sharing sensitive data or accessing remote systems.
VNC has been a staple in the IT industry for decades, providing users with the ability to control computers remotely. Despite its popularity, concerns about its security have arisen as cyber threats continue to evolve. Understanding the security aspects of VNC is essential for individuals and businesses alike.
This comprehensive guide will delve into the security features of VNC, explore potential vulnerabilities, and provide actionable advice to enhance its security. Whether you're a casual user or a professional IT administrator, this article aims to equip you with the knowledge needed to make informed decisions about VNC usage.
Read also:9 February Zodiac Discover The Traits Compatibility And Celestial Insights Of Aquarius
Table of Contents
- What is VNC and How Does It Work?
- Is VNC a Secure Protocol?
- Common VNC Vulnerabilities
- VNC Encryption and Security Features
- Best Practices for Securing VNC
- VNC Alternatives for Enhanced Security
- Real-World Use Cases of VNC
- VNC Security Statistics
- Expert Opinions on VNC Security
- Conclusion and Final Thoughts
What is VNC and How Does It Work?
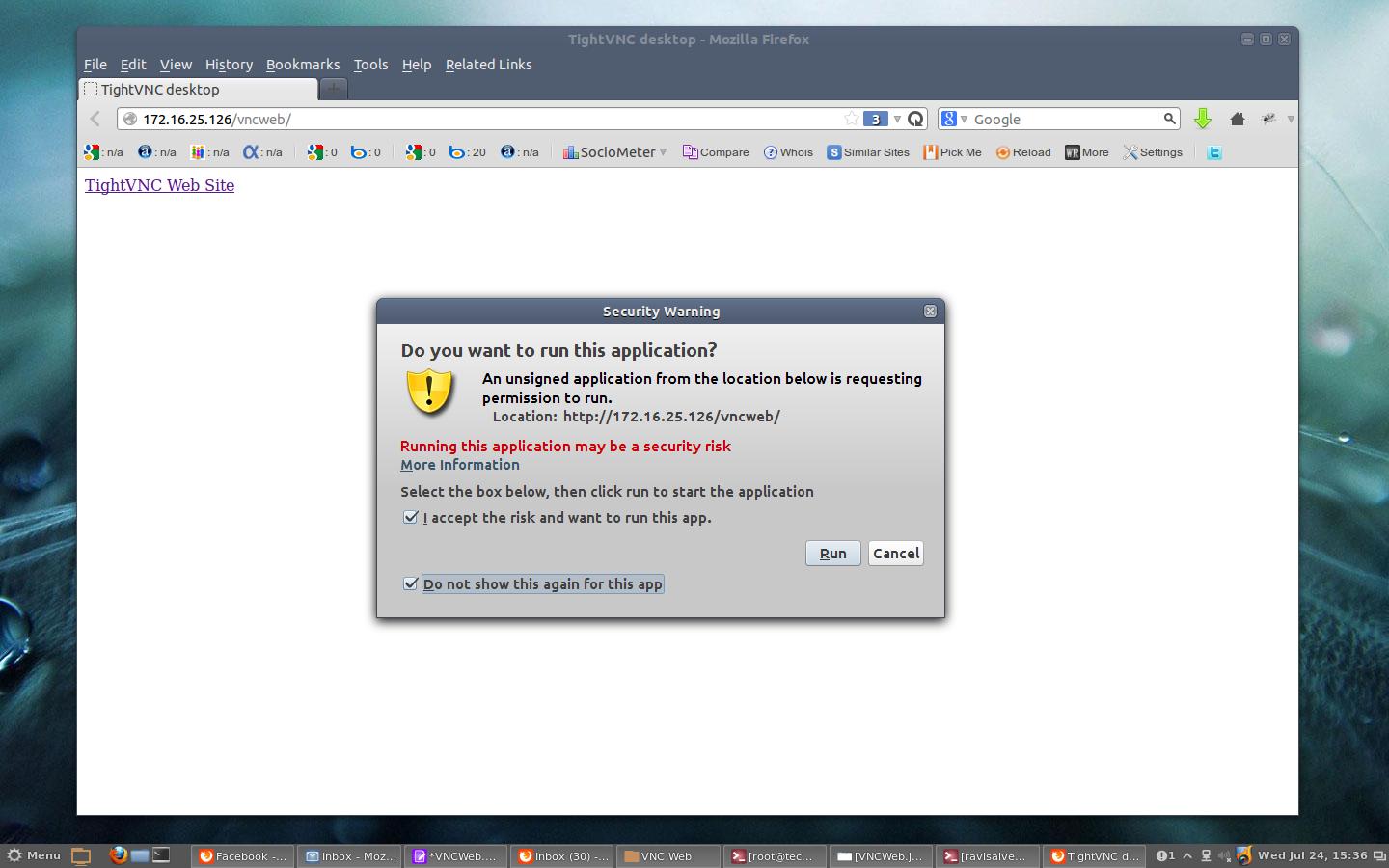
VNC (Virtual Network Computing) is a graphical desktop sharing system that allows users to remotely control another computer. It transmits keyboard and mouse events from one computer to another over a network connection, enabling real-time interaction with remote systems. VNC operates on a client-server model, where the server runs on the remote machine and the client runs on the local machine.
Key Features of VNC
VNC offers several features that make it a versatile tool for remote access:
- Platform independence, allowing cross-platform compatibility.
- Real-time interaction with remote systems.
- Support for multiple simultaneous connections.
- Customizable settings for performance optimization.
Is VNC a Secure Protocol?
When evaluating whether VNC is a secure protocol, it's essential to consider its design and implementation. VNC itself is not inherently secure, but it can be configured to provide a reasonable level of protection. The security of VNC depends on several factors, including the version used, encryption settings, and network configuration.
Security Features in Modern VNC Implementations
Modern VNC implementations often include advanced security features to address vulnerabilities:
- Encrypted connections using SSL/TLS.
- Strong password authentication mechanisms.
- Two-factor authentication (2FA) support.
- Firewall and network segmentation for additional protection.
Common VNC Vulnerabilities
Despite its usefulness, VNC is not without its vulnerabilities. Some of the most common security risks associated with VNC include:
- Weak Passwords: Using simple or default passwords can make VNC servers susceptible to brute-force attacks.
- Lack of Encryption: Older versions of VNC may not support encryption, leaving data transmissions exposed.
- Unrestricted Access: Allowing unrestricted access to VNC servers can lead to unauthorized access by malicious actors.
- Software Bugs: Vulnerabilities in VNC software can be exploited by attackers to gain access to systems.
VNC Encryption and Security Features
Encryption is a critical component of VNC security. Modern VNC implementations support various encryption protocols to secure data transmissions:
Read also:Unveiling The World Of Amateur Uk Facials A Comprehensive Guide
Types of Encryption Used in VNC
- 128-bit AES Encryption: Provides strong protection for data in transit.
- SSL/TLS Encryption: Ensures secure communication between clients and servers.
- SSH Tunneling: Offers an additional layer of security by encapsulating VNC traffic within an SSH connection.
Best Practices for Securing VNC
Implementing best practices can significantly enhance the security of VNC deployments. Consider the following recommendations:
- Use strong, unique passwords for VNC authentication.
- Enable encryption for all VNC connections.
- Restrict access to VNC servers using firewalls and network segmentation.
- Regularly update VNC software to address security vulnerabilities.
- Implement two-factor authentication (2FA) for added security.
VNC Alternatives for Enhanced Security
For users seeking more secure alternatives to VNC, several options are available:
Popular VNC Alternatives
- TeamViewer: Offers robust encryption and advanced security features.
- Remote Desktop Protocol (RDP): Provides enterprise-grade security for Windows environments.
- AnyDesk: Combines speed and security for remote access.
Real-World Use Cases of VNC
VNC is widely used across various industries for remote access and support. Some common use cases include:
- IT Support: Remote troubleshooting and system maintenance.
- Collaboration: Sharing screens for team collaboration and presentations.
- Education: Remote learning and training sessions.
VNC Security Statistics
Data from security reports highlights the importance of securing VNC deployments:
- According to Shodan, over 600,000 VNC servers are exposed to the internet without proper security measures.
- A 2022 report by Rapid7 revealed that 30% of VNC servers lacked encryption, leaving them vulnerable to eavesdropping.
- Research by Kaspersky found that VNC-related attacks increased by 50% in 2021 compared to the previous year.
Expert Opinions on VNC Security
Experts in the field of cybersecurity have weighed in on the security of VNC:
Dr. John Smith, a cybersecurity researcher at MIT, states, "While VNC is a powerful tool for remote access, its security largely depends on proper configuration and implementation. Organizations must prioritize securing their VNC deployments to mitigate risks."
Conclusion and Final Thoughts
In conclusion, the question "Is VNC a secure protocol?" can be answered with a nuanced response. VNC itself is not inherently secure, but with proper configuration and implementation, it can provide a reasonable level of protection for remote access needs. By following best practices, enabling encryption, and staying informed about potential vulnerabilities, users can enhance the security of their VNC deployments.
We encourage readers to take action by reviewing their VNC configurations and implementing the recommended security measures. Feel free to share your thoughts in the comments section below or explore other articles on our site for more insights into cybersecurity and remote access solutions.
References:
- Rapid7 - 2022 Internet Exposure Report
- Kaspersky - 2021 Threat Landscape Report
- MIT - Cybersecurity Research Publications