Amazon Web Services (AWS) tunneling has become a crucial aspect of modern cloud computing infrastructure. As businesses increasingly rely on cloud-based solutions, ensuring secure and reliable network connections is paramount. AWS offers a variety of tools and services that enable organizations to create encrypted tunnels, protecting sensitive data as it moves between on-premises environments and the cloud.
With the growing number of cyber threats and the need for robust security measures, AWS tunneling plays a vital role in safeguarding corporate data. By leveraging AWS's advanced tunneling technologies, companies can establish secure communication channels that protect against unauthorized access and potential data breaches.
This article delves into the intricacies of AWS tunneling, exploring its benefits, implementation methods, and best practices. Whether you're a network administrator, IT professional, or cybersecurity expert, understanding AWS tunneling is essential for maintaining secure and efficient cloud environments.
Read also:Exploring The Uk Amateur Facials Scene A Comprehensive Guide
Table of Contents
- What is AWS Tunneling?
- Types of Tunnels in AWS
- Benefits of AWS Tunneling
- AWS Tunneling Architecture
- Implementing AWS Tunneling
- Securing Data with AWS Tunneling
- Best Practices for AWS Tunneling
- Troubleshooting Common Issues
- Real-World Use Cases
- Future of AWS Tunneling
What is AWS Tunneling?
AWS tunneling refers to the process of creating encrypted communication channels between on-premises environments and AWS cloud resources. These tunnels ensure that data transmitted over public networks remains secure and protected from unauthorized access. AWS provides several tools and services, such as AWS Direct Connect and AWS Site-to-Site VPN, to facilitate secure tunneling.
Tunneling in AWS typically involves encapsulating data packets within a secure protocol, such as IPsec or TLS, to prevent interception by malicious actors. This method is particularly useful for organizations that require high levels of security and compliance with industry regulations.
Key Features of AWS Tunneling
- End-to-end encryption for secure data transmission
- Support for multiple tunneling protocols
- Scalability to accommodate growing network demands
- Integration with AWS's extensive ecosystem of services
Types of Tunnels in AWS
AWS offers various types of tunnels to suit different organizational needs. These include:
1. AWS Site-to-Site VPN
This service establishes an encrypted tunnel between on-premises networks and AWS Virtual Private Clouds (VPCs). AWS Site-to-Site VPN uses IPsec to ensure secure communication and supports dynamic routing protocols for optimal performance.
2. AWS Direct Connect
AWS Direct Connect provides a dedicated network connection between on-premises infrastructure and AWS. While not a traditional tunnel, it offers low-latency, high-bandwidth connectivity that can be paired with encryption for enhanced security.
3. AWS Client VPN
This service enables secure remote access to AWS resources through an encrypted tunnel. AWS Client VPN is ideal for employees working remotely who need secure access to corporate resources hosted in the cloud.
Read also:Harry Jowsey And Rylee Arnold A Comprehensive Look Into Their Journey Achievements And Impact
Benefits of AWS Tunneling
Implementing AWS tunneling offers numerous advantages, including:
- Enhanced security through end-to-end encryption
- Improved network performance with optimized routing
- Scalability to accommodate growing business needs
- Compliance with industry regulations and standards
- Cost-effective solution for securing cloud-based infrastructure
AWS Tunneling Architecture
The architecture of AWS tunneling involves several key components, including:
1. Virtual Private Cloud (VPC)
A VPC is a logically isolated section of the AWS cloud where you can launch resources in a virtual network that you define. It serves as the foundation for establishing secure tunnels between on-premises environments and AWS resources.
2. Customer Gateway
A customer gateway represents your on-premises router or firewall and is used to establish a connection with AWS. It is configured with the necessary credentials and settings to facilitate secure tunneling.
3. Virtual Private Gateway
A virtual private gateway acts as the AWS-side endpoint for a Site-to-Site VPN connection. It is attached to a VPC and manages the encryption and decryption of data transmitted over the tunnel.
Implementing AWS Tunneling
Implementing AWS tunneling involves several steps, including:
1. Planning Your Network Architecture
Before setting up a tunnel, it's essential to plan your network architecture carefully. This includes determining the appropriate tunneling protocol, identifying the resources that will communicate over the tunnel, and configuring security policies.
2. Configuring AWS Services
Once the network architecture is defined, you can configure the necessary AWS services, such as creating a VPC, setting up a customer gateway, and attaching a virtual private gateway.
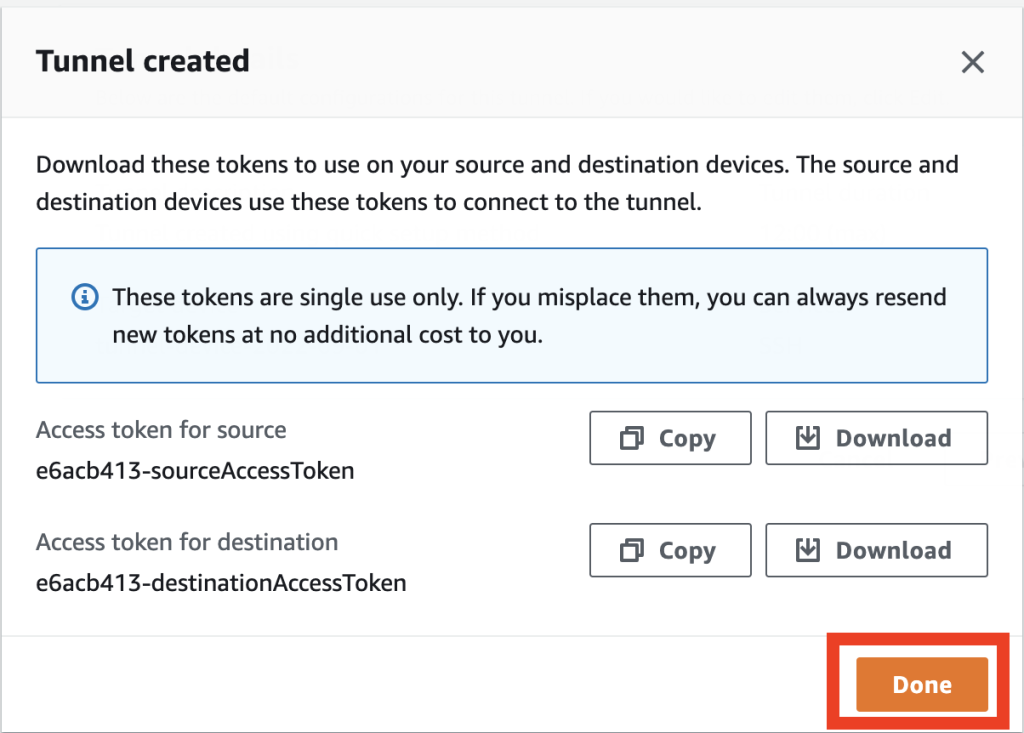
3. Establishing the Tunnel
With the AWS services configured, you can establish the tunnel by initiating a connection between the customer gateway and the virtual private gateway. This process typically involves exchanging encryption keys and configuring routing rules.
Securing Data with AWS Tunneling
AWS tunneling employs several security measures to protect data, including:
1. Encryption Protocols
Advanced encryption protocols, such as AES-256 and SHA-2, are used to secure data transmitted over tunnels. These protocols ensure that even if data is intercepted, it cannot be easily decrypted without the proper keys.
2. Access Controls
Implementing strict access controls is crucial for maintaining the integrity of AWS tunnels. This includes configuring firewalls, setting up security groups, and enforcing identity and access management (IAM) policies.
3. Monitoring and Logging
Regularly monitoring tunnel activity and maintaining detailed logs can help identify potential security threats. AWS provides tools such as CloudTrail and CloudWatch to facilitate this process.
Best Practices for AWS Tunneling
To maximize the effectiveness of AWS tunneling, consider the following best practices:
- Regularly update encryption keys and protocols
- Implement multi-factor authentication for added security
- Monitor tunnel performance and adjust configurations as needed
- Document all configurations and changes for future reference
- Perform regular security audits to identify vulnerabilities
Troubleshooting Common Issues
When implementing AWS tunneling, you may encounter various issues. Common problems include:
1. Connectivity Issues
Ensure that all necessary configurations, such as IP addresses and routing rules, are correctly set up. Verify that the customer gateway and virtual private gateway are properly connected.
2. Encryption Errors
Check that encryption keys and protocols are correctly configured on both sides of the tunnel. Ensure that all devices involved in the tunneling process support the required encryption standards.
3. Performance Bottlenecks
Optimize network settings and adjust tunnel configurations to improve performance. Consider upgrading hardware or increasing bandwidth if necessary.
Real-World Use Cases
AWS tunneling is widely used across various industries. Some notable use cases include:
1. Financial Services
Financial institutions rely on AWS tunneling to securely transmit sensitive customer data between on-premises systems and cloud-based applications.
2. Healthcare
Hospitals and healthcare providers use AWS tunneling to comply with HIPAA regulations while ensuring secure access to patient records.
3. E-commerce
Online retailers leverage AWS tunneling to protect customer information and maintain secure payment processing systems.
Future of AWS Tunneling
As technology continues to evolve, AWS tunneling is likely to become even more sophisticated. Advances in encryption techniques, automation, and artificial intelligence will enhance the security and efficiency of tunneling solutions. Additionally, the increasing adoption of hybrid cloud environments will drive further innovation in this area.
Conclusion
AWS tunneling is a critical component of modern cloud computing infrastructure, providing secure and reliable connections between on-premises environments and AWS resources. By understanding the various types of tunnels, implementation methods, and best practices, organizations can effectively leverage AWS tunneling to protect sensitive data and maintain compliance with industry regulations.
We encourage readers to share their experiences with AWS tunneling in the comments below. Additionally, feel free to explore other articles on our site for more insights into cloud computing and cybersecurity. Together, let's build a safer and more connected digital world!