In today's digital landscape, securing your network infrastructure is paramount. One of the most effective ways to protect your systems is through robust SSH key management. Best SSH key management software plays a crucial role in safeguarding sensitive data and ensuring secure access to servers. Without proper management, SSH keys can become a vulnerability, leading to unauthorized access and potential breaches.
SSH (Secure Shell) keys are essential tools for authentication in server environments. They provide a secure way for users and systems to communicate without the need for passwords. However, managing these keys manually can be cumbersome and error-prone, especially as organizations grow in size and complexity.
This article explores the best SSH key management software available in the market, offering insights into their features, benefits, and how they can help streamline your security processes. Whether you're a small business or a large enterprise, finding the right software can significantly enhance your security posture.
Read also:Charles Alden Black A Comprehensive Exploration Of His Life Achievements And Legacy
Table of Contents
- Introduction to SSH Key Management
- Why SSH Key Management is Important
- Criteria for Selecting the Best SSH Key Management Software
- Top 10 SSH Key Management Software
- Comparison of Features
- Steps for Implementing SSH Key Management
- Security Best Practices for SSH Keys
- Cost Analysis and ROI
- Future Trends in SSH Key Management
- Conclusion
Introduction to SSH Key Management
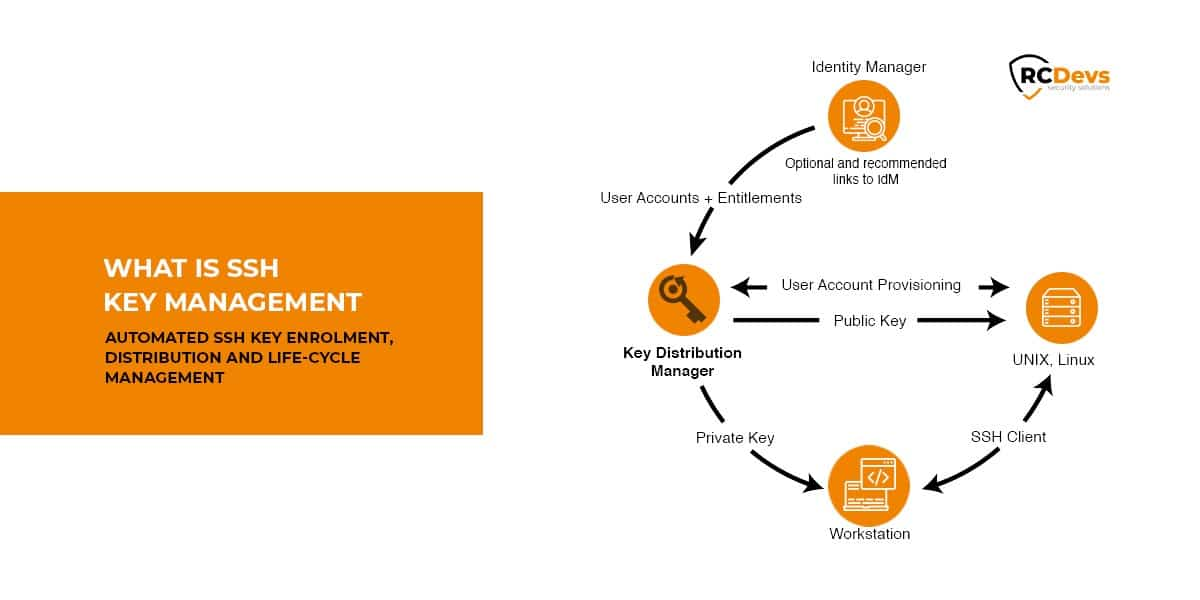
SSH key management involves organizing, monitoring, and securing SSH keys used for authentication in network environments. As organizations increasingly rely on cloud-based systems and remote work setups, the need for secure authentication has become more critical than ever. Best SSH key management software simplifies this process, ensuring that keys are properly managed and protected from misuse or unauthorized access.
Why SSH Key Management is Important
SSH keys are often referred to as the "keys to the kingdom" in IT infrastructure. Without proper management, these keys can become a significant security risk. Here are some reasons why SSH key management is crucial:
- Prevent Unauthorized Access: Mismanaged SSH keys can lead to unauthorized access to critical systems.
- Ensure Compliance: Many industries have strict regulations regarding data security, making SSH key management a compliance requirement.
- Reduce Operational Complexity: Automating key management reduces the burden on IT teams, allowing them to focus on other strategic tasks.
Criteria for Selecting the Best SSH Key Management Software
When evaluating SSH key management software, consider the following criteria:
- Scalability: Ensure the software can grow with your organization's needs.
- Automation: Look for tools that automate key rotation, revocation, and distribution.
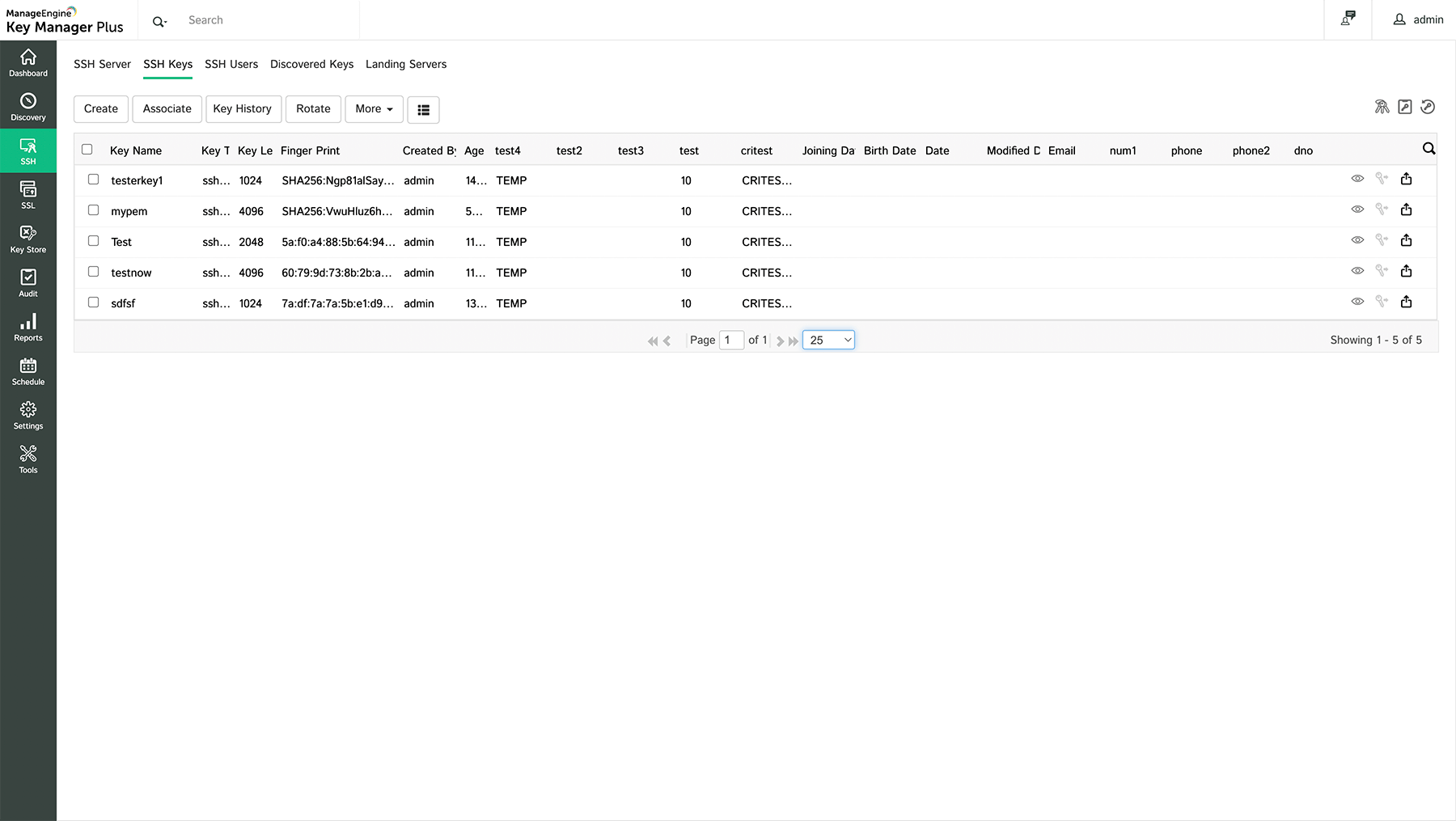
- Reporting and Auditing: Robust reporting features are essential for compliance and tracking key usage.
Top 10 SSH Key Management Software
Software 1: SSH Key Management Pro
SSH Key Management Pro is a comprehensive solution designed for enterprises seeking advanced security features. It offers automated key rotation, centralized key storage, and detailed audit trails. This software is particularly beneficial for organizations that require high-level compliance with industry standards.
Software 2: SecureAuth Key Manager
SecureAuth Key Manager focuses on simplifying the management of SSH keys across distributed environments. Its user-friendly interface and robust security protocols make it an ideal choice for businesses of all sizes. Key features include automated key discovery and real-time monitoring.
Software 3: Venafi Trust Protection Platform
Venafi Trust Protection Platform is renowned for its ability to manage SSH keys alongside other cryptographic keys. It provides a holistic approach to key management, ensuring that all keys are securely stored and monitored. This software is particularly effective for large enterprises with complex IT infrastructures.
Read also:Who Are The Actors For Alexa And Katie A Comprehensive Guide
Comparison of Features
Below is a comparison of the top SSH key management software based on key features:
- Automation Capabilities
- Scalability Options
- Compliance and Reporting Tools
Steps for Implementing SSH Key Management
Implementing SSH key management involves several steps:
- Conduct a thorough inventory of existing SSH keys.
- Select the appropriate software based on your organization's needs.
- Set up automated processes for key rotation and revocation.
- Train staff on the importance of SSH key management and how to use the software effectively.
Security Best Practices for SSH Keys
To maximize the security benefits of SSH key management, adhere to these best practices:
- Regularly update and rotate SSH keys.
- Limit the number of keys issued to each user or system.
- Implement multi-factor authentication alongside SSH keys.
Cost Analysis and ROI
While the cost of SSH key management software varies, the return on investment (ROI) is significant. By reducing the risk of security breaches and improving operational efficiency, organizations can save substantial resources in the long run. Additionally, compliance with industry standards can prevent costly fines and reputational damage.
Future Trends in SSH Key Management
The future of SSH key management is likely to include advancements in automation, machine learning, and integration with other security tools. As cyber threats continue to evolve, organizations must stay ahead by adopting cutting-edge technologies that enhance their security posture.
Conclusion
Best SSH key management software is an indispensable tool for any organization looking to enhance its security measures. By automating key management processes, ensuring compliance, and reducing operational complexity, these tools provide significant value. We encourage you to explore the options discussed in this article and choose the one that best fits your organization's needs.
Take action today by implementing SSH key management practices and sharing this article with your colleagues. For more insights on cybersecurity, explore our other articles and stay informed about the latest trends and solutions.