In today's interconnected world, accessing remote IoT devices has become a critical aspect of modern technology. As more devices are integrated into the Internet of Things (IoT), the ability to control and monitor them remotely has become increasingly important. Whether you're managing smart home systems, industrial equipment, or agricultural sensors, understanding how to securely access remote IoT devices is essential for maximizing efficiency and ensuring data protection.
Remote access to IoT devices allows users to interact with their systems from anywhere in the world, provided they have an internet connection. This capability opens up countless possibilities for businesses and individuals alike. However, with great power comes great responsibility. Ensuring that your remote access methods are secure and reliable is crucial to avoid potential cyber threats.
This article aims to provide a comprehensive guide on accessing remote IoT devices. We will explore various methods, tools, and best practices to ensure secure and efficient connectivity. Additionally, we will address common challenges and solutions, making this guide an invaluable resource for anyone looking to enhance their IoT system's accessibility and security.
Read also:Maria The Rising Star In The Japanese Actress Scene
Table of Contents
- Introduction to IoT
- Why Remote Access Matters
- Methods to Access Remote IoT Device
- Tools for Remote IoT Access
- Security Best Practices
- Common Challenges
- Remote Access Protocols
- Use Cases for Remote IoT Access
- Future of Remote IoT Access
- Conclusion
Introduction to IoT
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data with other devices and systems over the internet. IoT devices range from simple household appliances to sophisticated industrial tools. The ability to access these devices remotely is one of the key features that make IoT so powerful.
IoT technology has revolutionized industries by providing real-time data and insights. From smart homes to healthcare systems, IoT devices are transforming the way we live and work. However, as the number of connected devices grows, so does the complexity of managing and securing them. This is where remote access plays a vital role.
Benefits of IoT Devices
- Increased efficiency and automation
- Real-time monitoring and control
- Cost savings through optimized resource usage
- Enhanced user experience
Why Remote Access Matters
Accessing remote IoT devices is crucial for maintaining and managing systems effectively. Whether you're a homeowner checking your smart thermostat or an engineer troubleshooting industrial machinery, remote access saves time and resources. It allows users to perform tasks such as monitoring, configuring, and troubleshooting without being physically present at the device's location.
Remote access also enhances scalability. As businesses grow, they can add more devices to their IoT network without worrying about the logistics of manual management. This flexibility makes IoT systems highly adaptable to changing needs.
Key Features of Remote Access
- Real-time data access
- Centralized control
- Improved fault detection and resolution
- Reduced operational costs
Methods to Access Remote IoT Device
There are several methods to access remote IoT devices, each with its own advantages and limitations. The choice of method depends on factors such as device type, network infrastructure, and security requirements. Below are some of the most common methods:
1. Cloud-Based Platforms
Cloud-based platforms offer a centralized way to manage and access IoT devices. These platforms provide web interfaces and mobile apps, making it easy for users to interact with their devices from anywhere. Popular cloud platforms include AWS IoT, Microsoft Azure IoT, and Google Cloud IoT.
Read also:Amatuer Facials
2. Virtual Private Networks (VPNs)
VPNs create a secure connection between the user and the IoT device, encrypting all data transmitted between them. This method is particularly useful for securing sensitive information and protecting devices from unauthorized access.
3. Remote Desktop Protocols (RDP)
RDP allows users to access IoT devices remotely by connecting to a server or gateway. This method is commonly used in industrial settings where devices are connected to a central control system.
Tools for Remote IoT Access
Several tools are available to facilitate remote access to IoT devices. These tools range from software applications to hardware solutions, each designed to address specific needs. Below are some of the most widely used tools:
1. IoT Platforms
IoT platforms such as Particle, Losant, and Blynk provide comprehensive solutions for managing and accessing IoT devices. These platforms offer features like data visualization, device management, and remote control.
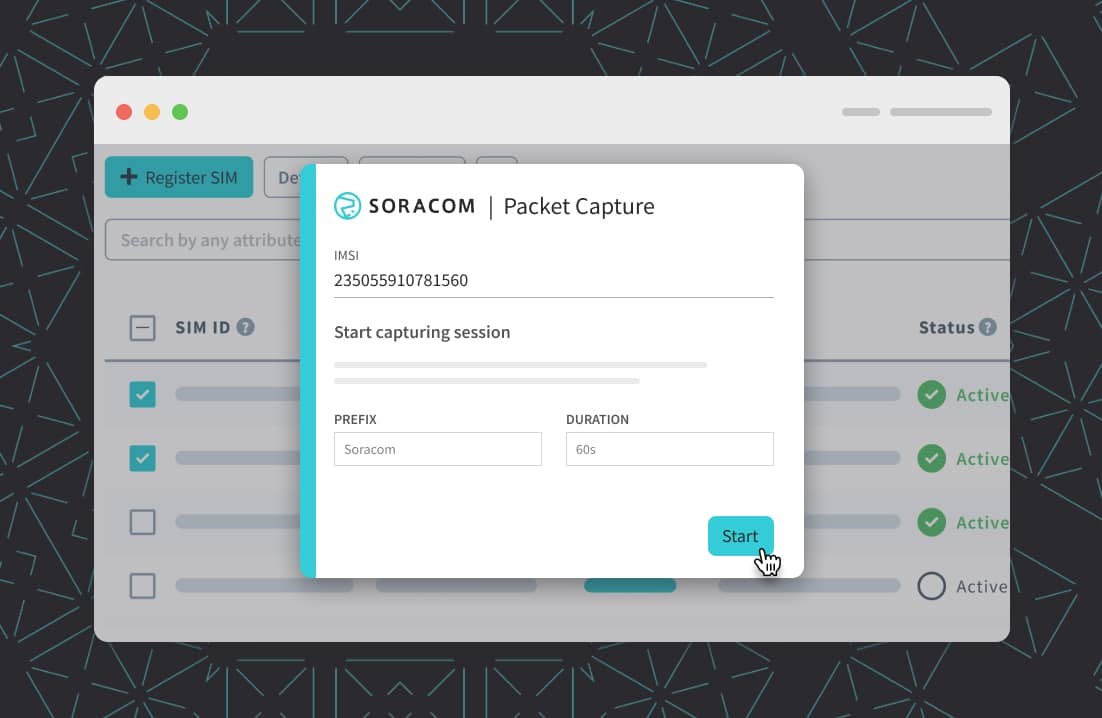
2. SSH Clients
SSH clients like PuTTY and OpenSSH allow users to securely access IoT devices via command-line interfaces. This method is ideal for technical users who prefer manual control over their devices.
3. Mobile Apps
Many IoT devices come with dedicated mobile apps that enable remote access. These apps provide user-friendly interfaces and are suitable for non-technical users.
Security Best Practices
Security is a top priority when accessing remote IoT devices. With the increasing number of cyber threats, implementing robust security measures is essential to protect sensitive data and prevent unauthorized access. Below are some best practices for securing your IoT devices:
1. Use Strong Authentication
Implement multi-factor authentication (MFA) to ensure only authorized users can access your devices. Strong passwords and biometric authentication can further enhance security.
2. Encrypt Data Transmission
Use encryption protocols such as SSL/TLS to secure data transmitted between devices and users. This prevents eavesdropping and data tampering.
3. Regularly Update Firmware
Keep your IoT devices' firmware up to date to patch vulnerabilities and improve performance. Manufacturers often release updates to address security issues and add new features.
Common Challenges
While remote access to IoT devices offers numerous benefits, it also presents several challenges. Below are some of the most common challenges and their solutions:
1. Network Connectivity Issues
Poor network connectivity can hinder remote access. Ensure that your devices have stable internet connections and use reliable network providers.
2. Security Threats
Cyberattacks targeting IoT devices are on the rise. Implementing strong security measures and monitoring your systems regularly can help mitigate these threats.
3. Compatibility Problems
Some devices may not be compatible with certain remote access methods. Choose platforms and tools that support a wide range of devices to avoid compatibility issues.
Remote Access Protocols
Various protocols are used to facilitate remote access to IoT devices. Understanding these protocols is essential for selecting the right method for your needs. Below are some of the most widely used protocols:
1. MQTT
MQTT (Message Queuing Telemetry Transport) is a lightweight protocol ideal for low-bandwidth environments. It is widely used in IoT applications due to its simplicity and efficiency.
2. HTTP/HTTPS
HTTP/HTTPS protocols are commonly used for web-based remote access. They provide secure communication between devices and users, making them suitable for cloud-based platforms.
3. CoAP
CoAP (Constrained Application Protocol) is designed for resource-constrained devices. It is ideal for IoT devices with limited processing power and memory.
Use Cases for Remote IoT Access
Remote access to IoT devices has numerous applications across various industries. Below are some of the most common use cases:
1. Smart Homes
Homeowners can remotely control smart lighting, thermostats, and security systems, enhancing convenience and energy efficiency.
2. Industrial Automation
Manufacturers can monitor and control industrial equipment from remote locations, improving productivity and reducing downtime.
3. Agriculture
Farmers can access weather sensors and irrigation systems remotely, optimizing crop yields and resource usage.
Future of Remote IoT Access
The future of remote IoT access looks promising, with advancements in technology driving innovation. Emerging trends such as 5G networks, edge computing, and artificial intelligence are set to revolutionize the way we interact with IoT devices. These technologies will enhance connectivity, reduce latency, and improve data processing capabilities.
As IoT continues to evolve, the importance of secure and efficient remote access will only increase. Businesses and individuals must stay informed about the latest developments and adopt best practices to stay ahead in this rapidly changing landscape.
Conclusion
In conclusion, accessing remote IoT devices is a critical aspect of modern technology. By understanding the methods, tools, and best practices for remote access, users can maximize the potential of their IoT systems while ensuring security and reliability. Whether you're managing a smart home or an industrial facility, remote access offers countless benefits that can enhance efficiency and convenience.
We encourage you to explore the resources and tools mentioned in this article and apply them to your IoT projects. Don't forget to leave a comment or share this article with others who may find it useful. For more information on IoT and related topics, check out our other articles on the site.