As the Internet of Things (IoT) continues to expand, the need to access IoT devices behind firewalls becomes increasingly important. Organizations and individuals must ensure secure and efficient communication between IoT devices and external networks. In this article, we will explore various methods and strategies for accessing IoT devices securely while maintaining robust network protection.
In today's interconnected world, IoT devices are everywhere, from smart home appliances to industrial equipment. However, accessing these devices from outside a secure network can pose significant challenges. This article will delve into practical examples and solutions, helping you understand how to access IoT devices behind firewalls effectively.
By the end of this guide, you will gain a thorough understanding of the best practices, tools, and protocols for accessing IoT devices securely. Whether you're a network administrator, IT professional, or simply someone interested in IoT technology, this article will provide valuable insights.
Read also:Sophie Thavet A Rising Star In The Entertainment Industry
Below is a table of contents with clickable links to help you navigate through the article effortlessly:
Table of Contents
- Understanding IoT Behind Firewalls
- Methods to Access IoT Devices Behind Firewalls
- Using a Virtual Private Network (VPN) for Secure Access
- Implementing Port Forwarding for IoT Access
- Cloud-Based Solutions for IoT Access
- Security Best Practices for IoT Access
- Real-World Examples of IoT Access Behind Firewalls
- Troubleshooting Common Issues
- Future Trends in IoT and Firewall Technology
- Conclusion
Understanding IoT Behind Firewalls
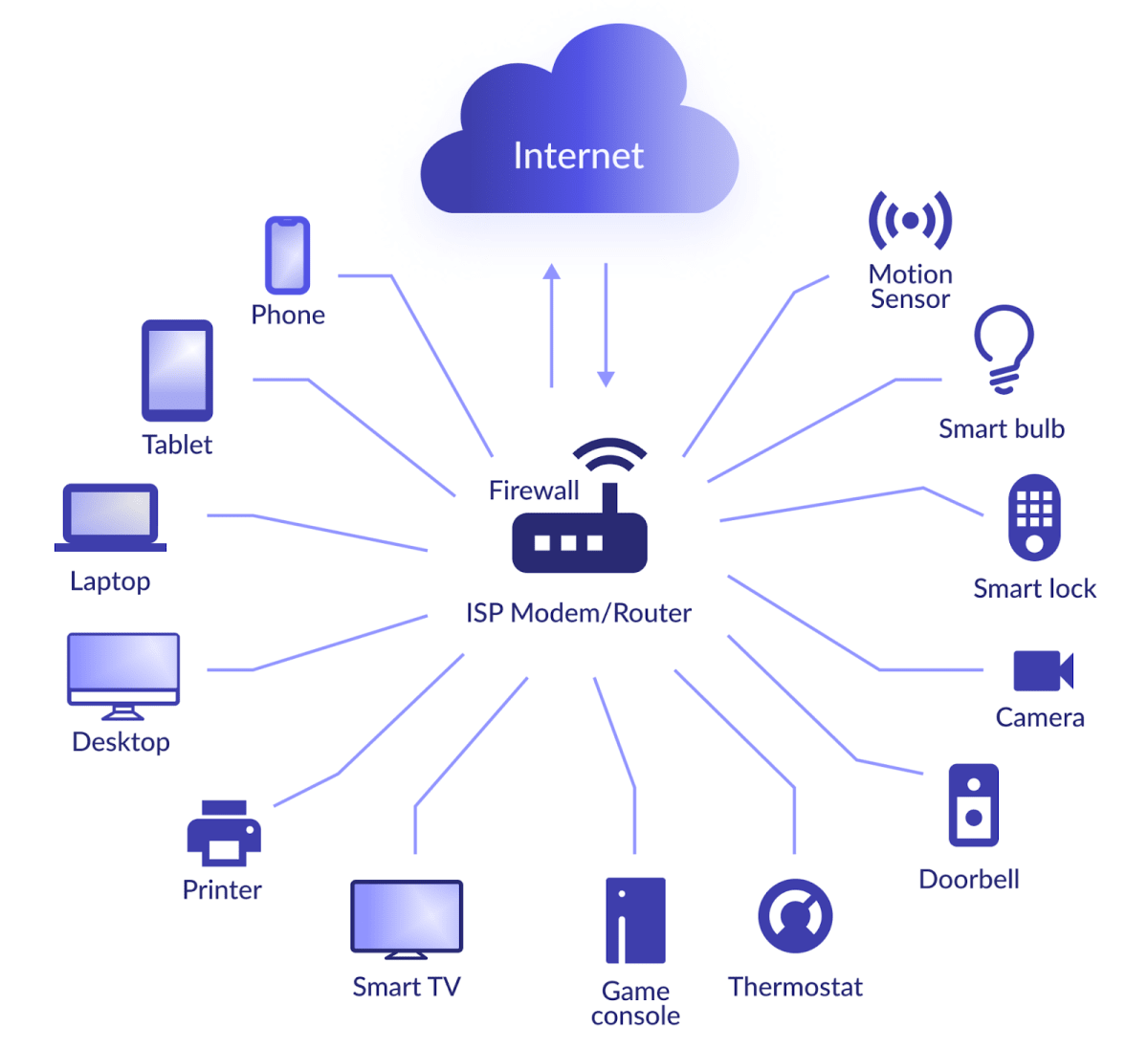
Firewalls play a crucial role in securing networks by controlling incoming and outgoing traffic based on predetermined security rules. When IoT devices are placed behind firewalls, it becomes essential to find ways to access them without compromising network security.
IoT devices often require external access for monitoring, management, and troubleshooting purposes. However, granting such access while maintaining a secure environment is a complex challenge. Understanding the architecture of IoT networks and the role of firewalls is the first step toward solving this issue.
According to a report by Gartner, the number of IoT devices is expected to surpass 25 billion by 2025. This rapid growth highlights the importance of secure access solutions for IoT devices.
Key Challenges in IoT Access
- Ensuring data privacy and protection
- Managing multiple devices within a single network
- Preventing unauthorized access to sensitive systems
- Scaling solutions for large-scale IoT deployments
Methods to Access IoT Devices Behind Firewalls
There are several methods available for accessing IoT devices behind firewalls. Each method has its own advantages and limitations, and the choice of method depends on the specific requirements of your network.
The following sections will explore various techniques in detail, providing practical examples and implementation strategies.
Read also:Who Did John Leguizamo Play In Ice Age A Comprehensive Guide
Direct Access via IP Address
One of the simplest methods is to access IoT devices using their IP addresses. However, this approach requires careful configuration of firewalls and routers to allow external traffic.
Using a Virtual Private Network (VPN) for Secure Access
A Virtual Private Network (VPN) is one of the most secure ways to access IoT devices behind firewalls. By encrypting all communication between the device and the external network, a VPN ensures that sensitive data remains protected.
VPNs are widely used in enterprise environments due to their ability to provide secure remote access to internal networks. Popular VPN solutions include OpenVPN, WireGuard, and Cisco AnyConnect.
Advantages of Using a VPN
- Enhanced security through encryption
- Centralized access control
- Compatibility with multiple devices and platforms
Implementing Port Forwarding for IoT Access
Port forwarding is another method for accessing IoT devices behind firewalls. This technique involves configuring your router to direct incoming traffic to a specific device on your network.
While port forwarding is relatively easy to set up, it does pose some security risks if not properly configured. It is essential to use strong passwords and restrict access to only necessary ports.
Steps to Configure Port Forwarding
- Log in to your router's admin panel
- Locate the port forwarding settings
- Specify the internal IP address of the IoT device
- Assign a specific external port for communication
Cloud-Based Solutions for IoT Access
Cloud-based solutions offer a scalable and flexible way to access IoT devices behind firewalls. These solutions typically involve deploying IoT gateways in the cloud, which act as intermediaries between the devices and external networks.
Platforms such as AWS IoT Core, Microsoft Azure IoT Hub, and Google Cloud IoT Core provide robust tools for managing IoT devices securely.
Benefits of Cloud-Based IoT Access
- Automatic updates and maintenance
- Scalability for growing IoT deployments
- Integrated analytics and monitoring capabilities
Security Best Practices for IoT Access
Securing IoT devices behind firewalls requires a multi-layered approach. Below are some best practices to ensure the safety and integrity of your IoT network:
- Use strong, unique passwords for all devices
- Regularly update firmware and software
- Implement network segmentation to isolate IoT devices
- Monitor network activity for suspicious behavior
According to a study by IBM, 60% of data breaches involve compromised credentials. This statistic underscores the importance of implementing strong authentication mechanisms for IoT devices.
Real-World Examples of IoT Access Behind Firewalls
Several organizations have successfully implemented secure IoT access solutions. For example, a manufacturing company used a combination of VPN and cloud-based technologies to remotely monitor and manage their industrial IoT devices.
Another example involves a smart city initiative where IoT sensors were deployed to monitor traffic patterns. The city used a combination of port forwarding and network segmentation to ensure secure access to the sensors.
Case Study: Secure IoT Access in Healthcare
In the healthcare industry, secure access to IoT devices is critical for patient safety. A hospital implemented a cloud-based IoT solution to monitor vital signs of patients in real-time. This solution allowed doctors and nurses to access critical data securely from anywhere in the hospital.
Troubleshooting Common Issues
Despite careful planning, issues may arise when accessing IoT devices behind firewalls. Below are some common problems and their solutions:
- Connection Timeout: Ensure that firewalls and routers are properly configured to allow external traffic.
- Unauthorized Access: Implement strong authentication mechanisms and restrict access to trusted users.
- Data Loss: Use encryption and backup solutions to protect sensitive information.
Future Trends in IoT and Firewall Technology
The future of IoT and firewall technology is exciting, with advancements such as artificial intelligence and machine learning playing a significant role. These technologies will enable more intelligent and adaptive security solutions for IoT networks.
Additionally, the development of 5G networks will provide faster and more reliable connectivity for IoT devices, further enhancing their capabilities.
Emerging Technologies in IoT Security
- AI-driven threat detection
- Blockchain for secure data sharing
- Zero-trust architecture for network security
Conclusion
In conclusion, accessing IoT devices behind firewalls is a critical challenge that requires careful consideration of security, scalability, and ease of use. By implementing the methods and best practices outlined in this article, you can ensure secure and efficient access to your IoT devices.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT technology and network security.