As the Internet of Things (IoT) continues to grow, securely connecting remote devices has become a top priority for businesses and developers. With the increasing reliance on cloud computing, platforms like AWS provide robust solutions to manage IoT devices seamlessly. By leveraging Raspberry Pi and AWS VPC, you can create a secure and scalable infrastructure for your IoT projects. In this article, we will explore how to securely connect remote IoT devices using Raspberry Pi and AWS services.
The integration of IoT devices with cloud platforms like AWS offers numerous advantages, including enhanced scalability, real-time data processing, and centralized management. However, ensuring the security of these connections is critical, especially when devices are deployed remotely. This article will provide a comprehensive guide on setting up a secure infrastructure for IoT devices using Raspberry Pi and AWS VPC.
Whether you're a developer, IT professional, or hobbyist, understanding how to securely connect remote IoT devices is essential. By the end of this article, you'll have the knowledge and tools to implement a secure and efficient IoT setup using Raspberry Pi and AWS services. Let's dive in!
Read also:Inspirational Quotes On Gangs Understanding Overcoming And Empowering
Table of Contents:
- Introduction to IoT and AWS VPC
- Raspberry Pi Overview
- AWS VPC Explained
- Setting Up Secure Connections
- Remote Device Management
- Best Security Practices
- Troubleshooting Common Issues
- Scaling IoT Infrastructure
- Real-World Use Cases
- Conclusion
Introduction to IoT and AWS VPC
The Internet of Things (IoT) refers to the network of interconnected devices that communicate and exchange data over the internet. These devices range from smart home appliances to industrial sensors and wearable technology. AWS Virtual Private Cloud (VPC) provides a secure and isolated environment for managing IoT devices, ensuring that data remains protected and accessible only to authorized users.
Why Use AWS for IoT?
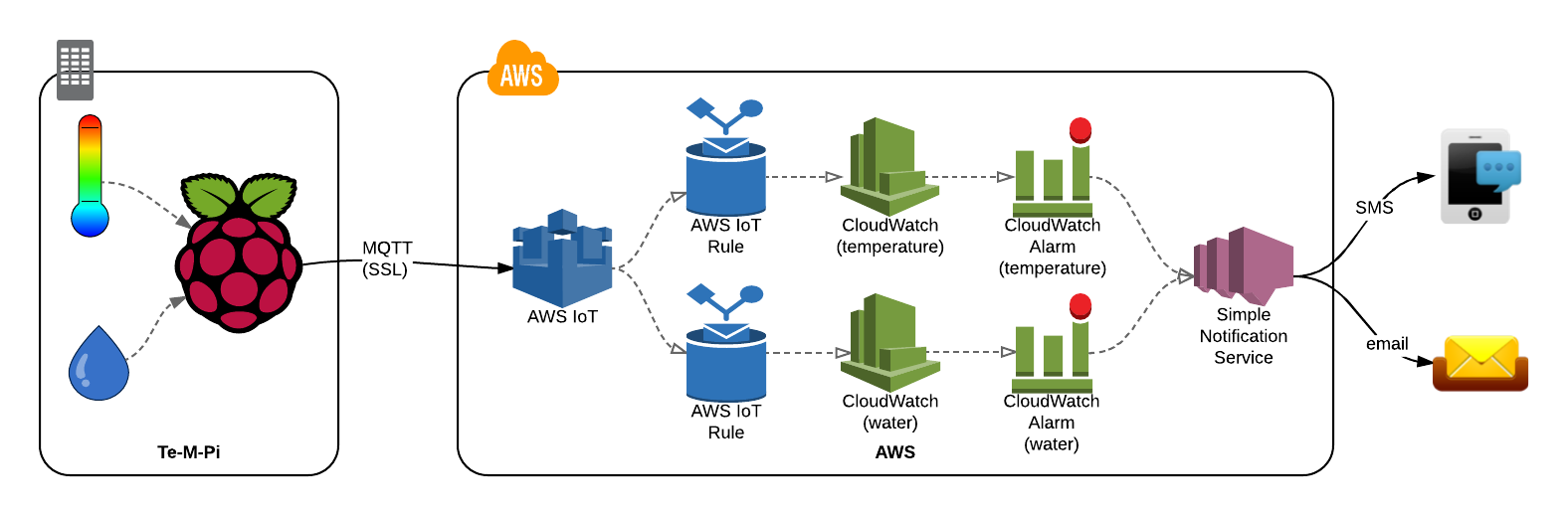
AWS offers a range of services tailored for IoT applications, including AWS IoT Core, AWS Lambda, and Amazon Kinesis. These services enable real-time data processing, device management, and secure communication between devices and the cloud. By leveraging AWS VPC, you can create a private network that isolates your IoT devices from the public internet, reducing the risk of unauthorized access.
Key Features of AWS IoT
- Secure device communication using MQTT, HTTP, or WebSockets.
- Device management and monitoring through AWS IoT Core.
- Scalable infrastructure to handle millions of devices.
- Integration with other AWS services for advanced analytics and machine learning.
Raspberry Pi Overview
Raspberry Pi is a popular single-board computer used for a variety of applications, including IoT projects. Its affordability, small form factor, and open-source nature make it an ideal choice for developers and hobbyists alike. By combining Raspberry Pi with AWS services, you can create a powerful and secure IoT setup.
Read also:How Did Doc Shaw Passed Away Unveiling The Truth Behind His Demise
Key Features of Raspberry Pi
- Supports multiple operating systems, including Raspbian and Ubuntu.
- Equipped with GPIO pins for interfacing with sensors and actuators.
- Includes built-in Wi-Fi and Bluetooth for wireless communication.
- Can be easily programmed using Python, C++, and other languages.
AWS VPC Explained
AWS Virtual Private Cloud (VPC) allows you to create a private network within the AWS cloud. This network is isolated from other AWS accounts and the public internet, providing an additional layer of security for your IoT devices. By configuring subnets, security groups, and network access control lists (NACLs), you can control inbound and outbound traffic to your devices.
Components of AWS VPC
- VPC Subnets: Divide your VPC into smaller networks for better organization and security.
- Security Groups: Act as virtual firewalls to control traffic to and from your instances.
- NACLs: Provide an additional layer of security by controlling traffic at the subnet level.
Setting Up Secure Connections
To securely connect your Raspberry Pi to AWS VPC, you need to follow a series of steps. These include configuring your VPC, setting up a Raspberry Pi instance, and establishing secure communication channels.
Step 1: Configure AWS VPC
Create a new VPC in the AWS Management Console and configure subnets, security groups, and NACLs to suit your needs. Ensure that your VPC is properly isolated from the public internet to prevent unauthorized access.
Step 2: Set Up Raspberry Pi
Install the necessary software on your Raspberry Pi, including the AWS IoT SDK and MQTT client. Configure the device to connect to your AWS VPC using secure protocols such as TLS.
Remote Device Management
Managing IoT devices remotely is crucial for maintaining their functionality and security. AWS IoT Core provides tools for monitoring and managing devices from a centralized location. You can use these tools to update firmware, troubleshoot issues, and enforce security policies.
Best Practices for Remote Management
- Regularly update device firmware to patch security vulnerabilities.
- Monitor device activity to detect and respond to suspicious behavior.
- Enforce strict access controls to prevent unauthorized access.
Best Security Practices
Securing your IoT devices is paramount, especially when they are deployed remotely. Implementing best security practices can help protect your devices and data from cyber threats.
Security Tips for IoT Devices
- Use strong passwords and two-factor authentication for device access.
- Encrypt data in transit and at rest using industry-standard protocols.
- Regularly audit your security settings to ensure compliance with best practices.
Troubleshooting Common Issues
Even with the best planning, issues can arise when setting up IoT devices. Common problems include connectivity issues, configuration errors, and security breaches. By understanding these issues and their solutions, you can quickly resolve them and maintain the integrity of your IoT setup.
Common IoT Issues and Solutions
- Connectivity Problems: Check network settings and ensure that all devices are properly configured.
- Configuration Errors: Review device settings and update them as needed.
- Security Breaches: Investigate suspicious activity and strengthen security measures.
Scaling IoT Infrastructure
As your IoT project grows, you may need to scale your infrastructure to accommodate additional devices and data. AWS provides several tools and services to help you scale your IoT infrastructure efficiently and cost-effectively.
Scaling Strategies for IoT
- Use AWS Auto Scaling to automatically adjust resources based on demand.
- Implement data analytics tools to process and analyze large volumes of data.
- Optimize device communication to reduce latency and improve performance.
Real-World Use Cases
IoT applications are being used in a variety of industries, including healthcare, agriculture, and manufacturing. By leveraging Raspberry Pi and AWS VPC, businesses can create innovative solutions that improve efficiency, reduce costs, and enhance customer experiences.
Examples of IoT Applications
- Smart Agriculture: Monitor soil moisture and weather conditions to optimize crop yields.
- Remote Healthcare: Enable patients to monitor their health remotely and share data with healthcare providers.
- Industrial Automation: Automate manufacturing processes to improve productivity and reduce errors.
Conclusion
Securing remote IoT devices using Raspberry Pi and AWS VPC is a critical task that requires careful planning and execution. By following the steps outlined in this article, you can create a secure and scalable infrastructure for your IoT projects. Remember to implement best security practices, regularly update your devices, and monitor their activity to ensure their continued functionality and security.
We encourage you to share your thoughts and experiences in the comments section below. If you found this article helpful, please consider sharing it with your network. For more insights on IoT and cloud computing, explore our other articles and resources.