Windows VNC security issues have become a critical concern for businesses and individuals alike who rely on remote desktop connections. Virtual Network Computing (VNC) is a widely used protocol that allows users to control computers remotely. However, its security vulnerabilities can expose sensitive data to malicious actors. As cyber threats continue to evolve, understanding the risks associated with VNC and implementing robust security measures is essential to protect your systems.
With the increasing reliance on remote work and virtual environments, securing VNC connections has never been more important. Many organizations use VNC to manage servers, troubleshoot issues, and collaborate on projects. However, without proper configuration and security measures, VNC can become a gateway for hackers to infiltrate networks and steal valuable information.
This article will explore the various Windows VNC security issues, including common vulnerabilities, best practices for securing VNC connections, and the importance of staying updated with the latest security protocols. Whether you're an IT professional or a casual user, understanding these risks and solutions can help safeguard your digital assets.
Read also:Meet The Cast Of Bear In The Big Blue House Characters A Comprehensive Guide
Table of Contents
- Introduction to VNC
- Common VNC Vulnerabilities
- Windows VNC Security Risks
- Securing VNC Connections
- Best Practices for VNC
- Encryption and Authentication
- Firewall and Network Security
- VNC Software Comparison
- Updates and Patches
- Conclusion and Call to Action
Introduction to VNC
Virtual Network Computing (VNC) is a graphical desktop sharing system that allows users to remotely control another computer. It transmits keyboard and mouse events from one computer to another over a network connection. VNC is widely used in corporate environments for remote support, server management, and collaboration.
However, VNC's open architecture and lack of built-in security features make it susceptible to various security issues. Understanding how VNC works and its limitations is crucial for mitigating potential risks. In this section, we'll delve into the basics of VNC and its role in modern IT infrastructure.
Common VNC Vulnerabilities
Weak Passwords
One of the most common VNC vulnerabilities is the use of weak or default passwords. Hackers can easily exploit these by using brute-force attacks or dictionary attacks to gain unauthorized access.
Unencrypted Connections
Without proper encryption, VNC connections can expose sensitive data to eavesdropping. This includes keystrokes, mouse movements, and even confidential documents being transmitted over the network.
Outdated Software
Using outdated VNC software can leave systems vulnerable to known exploits. Regular updates and patches are essential to address security flaws and protect against emerging threats.
Windows VNC Security Risks
Windows users face unique challenges when implementing VNC due to the operating system's architecture and network configurations. Some of the key security risks include:
Read also:Lea Dellecave The Remarkable Journey Of A Tech Entrepreneur Redefining Industries
- Unsecured ports: VNC typically uses port 5900, which can be easily targeted by attackers.
- Malware infections: Infected systems can compromise VNC connections, allowing hackers to gain control.
- Insufficient logging: Without proper logging mechanisms, it can be difficult to detect unauthorized access.
Securing VNC Connections
Securing VNC connections involves a combination of technical measures and best practices. Here are some strategies to enhance VNC security:
- Use strong, unique passwords for VNC authentication.
- Enable encryption protocols such as SSL/TLS to protect data in transit.
- Limit access to VNC ports using firewalls and network segmentation.
Best Practices for VNC
User Education
Training users on the importance of security and proper VNC usage is critical. Employees should be aware of the risks associated with remote connections and how to avoid them.
Regular Audits
Conducting regular security audits can help identify vulnerabilities and ensure compliance with organizational policies. This includes reviewing access logs and monitoring network activity.
Access Controls
Implementing strict access controls ensures that only authorized personnel can access VNC-enabled systems. Role-based access control (RBAC) is an effective way to manage permissions.
Encryption and Authentication
Encryption and authentication are fundamental to securing VNC connections. Modern VNC software supports advanced encryption standards such as AES-256, which provide robust protection against data breaches. Additionally, multi-factor authentication (MFA) can significantly enhance security by requiring users to provide multiple forms of verification.
Firewall and Network Security
Firewalls play a crucial role in protecting VNC connections by blocking unauthorized access attempts. Configuring firewalls to allow only specific IP addresses or ranges can reduce the attack surface. Network segmentation further isolates sensitive systems, making it more difficult for attackers to move laterally within the network.
VNC Software Comparison
Choosing the right VNC software is essential for ensuring security and functionality. Some popular options include:
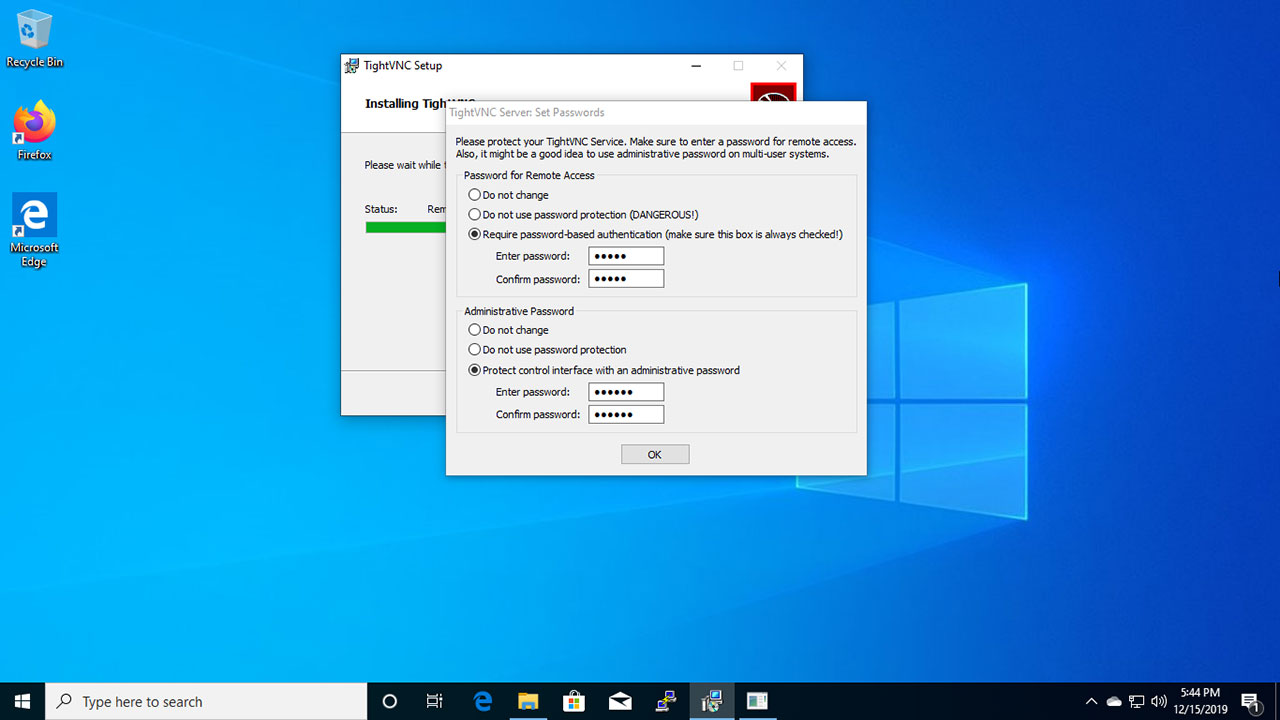
- TightVNC: Lightweight and easy to use, but lacks advanced security features.
- RealVNC: Offers enterprise-grade security and supports multiple platforms.
- UltraVNC: Provides robust encryption and additional plugins for enhanced functionality.
Each software has its strengths and weaknesses, so selecting the one that best fits your organization's needs is crucial.
Updates and Patches
Keeping VNC software up to date is vital for addressing security vulnerabilities. Software vendors frequently release patches to fix bugs and improve security. Regularly checking for updates and applying them promptly can prevent exploitation of known weaknesses.
Conclusion and Call to Action
In conclusion, Windows VNC security issues pose significant risks to individuals and organizations. By understanding the vulnerabilities and implementing appropriate security measures, you can effectively protect your systems and data. Remember to use strong passwords, enable encryption, and regularly update your software.
We encourage readers to share their thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into cybersecurity best practices. Together, we can create a safer digital environment for everyone.
Data Source: VNC Official Website, CISA