In today's digital era, VNC (Virtual Network Computing) server usage has become increasingly popular for remote access and control. However, the rise in VNC server adoption has also highlighted the critical issue of VNC server security risk. As more businesses and individuals rely on remote work solutions, understanding and mitigating these risks is essential to safeguard sensitive data and systems.
VNC server security risk is a growing concern for IT professionals and users alike. The technology allows users to remotely access and control computers from distant locations, making it an invaluable tool for collaboration and troubleshooting. However, this convenience comes with potential vulnerabilities that could be exploited by malicious actors.
Throughout this article, we will explore the various aspects of VNC server security risks, including how they occur, the potential consequences, and effective strategies to protect your systems. By understanding these risks, you can take proactive steps to ensure your remote connections remain secure and protected.
Read also:Harry Jowsey And Rylee Arnold A Comprehensive Look Into Their Journey Achievements And Impact
Understanding VNC Server Security Risk
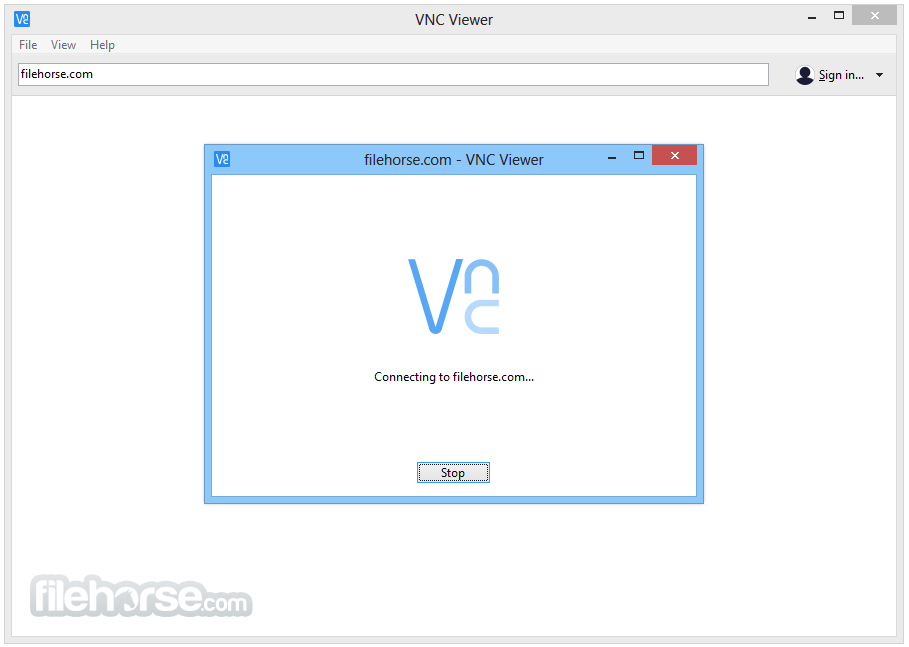
VNC server security risk refers to the potential vulnerabilities and threats associated with using VNC technology for remote access. These risks can arise from improper configuration, weak authentication mechanisms, or outdated software versions. Understanding these risks is the first step in securing your VNC connections.
Common VNC server security risks include unauthorized access, data interception, and exploitation of software vulnerabilities. These risks can lead to severe consequences, such as data breaches, financial losses, and reputational damage. Therefore, it is crucial to implement robust security measures to mitigate these risks.
Types of VNC Server Security Risks
Unauthorized Access
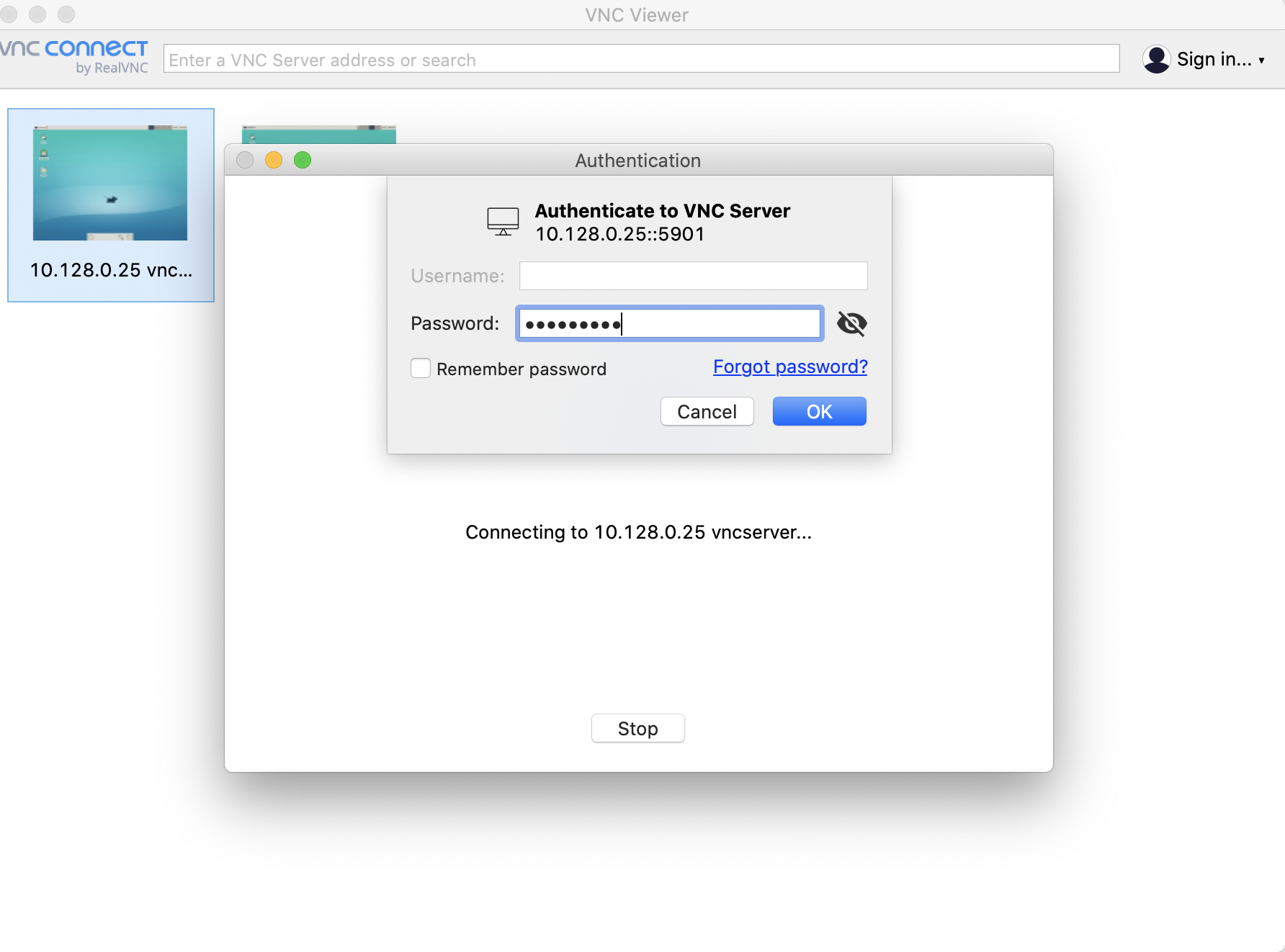
One of the most significant VNC server security risks is unauthorized access. This occurs when attackers gain access to your VNC server without proper authorization. Weak passwords, lack of encryption, and unpatched vulnerabilities are common causes of unauthorized access.
- Weak passwords can be easily guessed or cracked using brute-force attacks.
- Unencrypted connections expose sensitive data to interception and eavesdropping.
- Outdated software versions may contain known vulnerabilities that attackers can exploit.
Data Interception
Data interception is another critical VNC server security risk. When data transmitted between the client and server is not encrypted, attackers can intercept and steal sensitive information. This can include login credentials, personal data, and confidential business information.
Consequences of VNC Server Security Breaches
The consequences of VNC server security breaches can be severe and far-reaching. Organizations and individuals who experience such breaches may face significant financial losses, legal liabilities, and damage to their reputation. Additionally, compromised systems can lead to further attacks, such as ransomware or malware infections.
Some of the potential consequences of VNC server security breaches include:
Read also:Alexa And Katie Cast A Comprehensive Look At The Talented Ensemble Behind The Heartwarming Show
- Loss of sensitive data, including personal information and intellectual property.
- Financial losses due to theft, fraud, or the cost of recovering from an attack.
- Reputational damage, which can impact customer trust and business relationships.
- Compliance violations, leading to fines and penalties for failing to protect sensitive data.
Best Practices for Securing VNC Servers
Implementing best practices for securing VNC servers is essential to mitigate the risks associated with remote access. By following these guidelines, you can enhance the security of your VNC connections and protect your systems from potential threats.
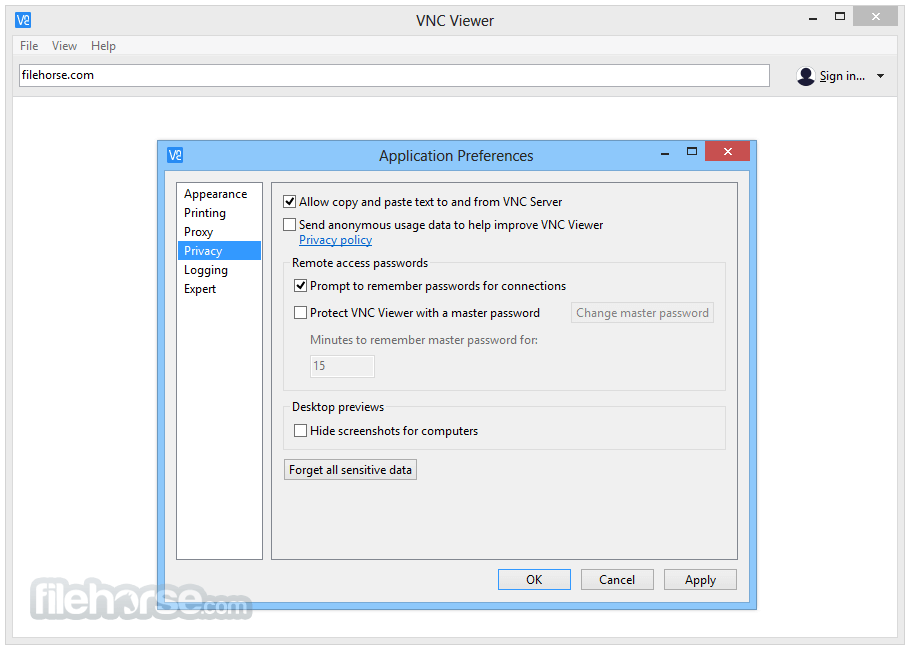
Use Strong Authentication
Strong authentication is a fundamental aspect of VNC server security. This involves using robust passwords, two-factor authentication (2FA), and other methods to ensure only authorized users can access your VNC server.
Enable Encryption
Encryption is critical for protecting data transmitted between the client and server. By enabling encryption, you can prevent attackers from intercepting and reading sensitive information. Popular encryption protocols for VNC include SSL/TLS and AES.
Regularly Update Software
Keeping your VNC software up to date is essential for addressing known vulnerabilities and ensuring the security of your system. Regularly updating your software helps protect against exploits targeting outdated versions.
Monitoring and Logging VNC Connections
Monitoring and logging VNC connections can help detect and respond to potential security incidents. By tracking connection attempts, login activity, and other relevant data, you can identify suspicious behavior and take appropriate action.
Implementing a centralized logging system and setting up alerts for unusual activity can significantly enhance your ability to detect and respond to security threats. Additionally, reviewing logs regularly can provide valuable insights into potential vulnerabilities and areas for improvement.
Firewall and Network Security
Firewalls and network security measures play a crucial role in protecting VNC servers from external threats. By configuring firewalls to restrict access to VNC ports and implementing network segmentation, you can reduce the attack surface and enhance overall security.
Restrict Access to VNC Ports
Limiting access to VNC ports is an effective way to prevent unauthorized access. By configuring firewalls to allow only trusted IP addresses or networks, you can reduce the risk of attackers gaining access to your VNC server.
Implement Network Segmentation
Network segmentation involves dividing your network into smaller, isolated segments. This approach can help contain potential breaches and prevent attackers from moving laterally within your network.
Employee Training and Awareness
Employee training and awareness are vital components of VNC server security. Educating users about best practices, recognizing phishing attempts, and following security protocols can significantly reduce the risk of security breaches.
Organizations should regularly conduct training sessions and provide resources to help employees understand the importance of VNC server security and their role in maintaining it.
Third-Party Audits and Penetration Testing
Conducting third-party audits and penetration testing can help identify vulnerabilities in your VNC server setup. These assessments provide valuable insights into potential weaknesses and recommendations for improving security.
Engaging professional security experts to evaluate your VNC server configuration can help ensure compliance with industry standards and best practices. Regular audits and testing can also help demonstrate due diligence and commitment to security.
Legal and Compliance Considerations
Organizations must consider legal and compliance requirements when implementing VNC server security measures. Depending on your industry and geographic location, you may be subject to regulations such as GDPR, HIPAA, or PCI-DSS.
Ensuring compliance with these regulations is essential to avoid penalties and protect sensitive data. Implementing appropriate security controls and documenting your efforts can help demonstrate compliance and reduce legal risks.
Emerging Threats and Future Trends
As technology evolves, so do the threats associated with VNC server security. Staying informed about emerging threats and trends is crucial for maintaining robust security measures. Some of the emerging trends in VNC server security include:
- Increased use of artificial intelligence and machine learning for threat detection.
- Advancements in encryption and authentication technologies.
- Greater emphasis on zero-trust architecture and micro-segmentation.
Conclusion and Call to Action
VNC server security risk is a significant concern for anyone using remote access technology. By understanding the potential risks and implementing best practices, you can protect your systems and data from malicious actors. Remember to use strong authentication, enable encryption, and regularly update your software to enhance security.
We encourage you to take action by reviewing your current VNC server setup and implementing the recommended security measures. Additionally, consider sharing this article with colleagues and friends to help raise awareness about VNC server security risks. For more information on cybersecurity best practices, explore our other articles and resources.
Table of Contents
- Understanding VNC Server Security Risk
- Types of VNC Server Security Risks
- Consequences of VNC Server Security Breaches
- Best Practices for Securing VNC Servers
- Monitoring and Logging VNC Connections
- Firewall and Network Security
- Employee Training and Awareness
- Third-Party Audits and Penetration Testing
- Legal and Compliance Considerations
- Emerging Threats and Future Trends
- Conclusion and Call to Action
For more detailed information, refer to trusted sources such as the National Institute of Standards and Technology (NIST) and the Center for Internet Security (CIS).