Connecting remote IoT devices through a peer-to-peer (P2P) network using a Raspberry Pi is becoming increasingly essential for modern tech enthusiasts and professionals alike. As the Internet of Things (IoT) continues to expand, ensuring secure and seamless communication between devices has become a priority. This guide will explore the intricacies of setting up a secure connection for remote IoT devices using Raspberry Pi in a P2P configuration.
With the rise of smart homes, industrial automation, and wearable technology, IoT has transformed how we interact with devices. However, security remains a significant concern, especially when devices are connected remotely. This article will provide step-by-step instructions, expert tips, and best practices to help you establish a robust and secure connection.
Whether you're a hobbyist or a professional, understanding how to securely connect remote IoT devices using Raspberry Pi will empower you to create innovative projects while maintaining top-notch security standards. Let's dive into the details and learn how to achieve this efficiently.
Read also:Who Are The Actors For Alexa And Katie A Comprehensive Guide
Table of Contents
- Overview of Securely Connecting IoT P2P Raspberry Pi
- Understanding Raspberry Pi Basics
- Introduction to IoT and Its Importance
- Peer-to-Peer Architecture Explained
- Security Challenges in Remote IoT Connections
- Tools and Software You’ll Need
- Step-by-Step Setup Process
- Best Practices for Secure Connections
- Troubleshooting Common Issues
- Future Trends in IoT Security
Overview of Securely Connecting IoT P2P Raspberry Pi
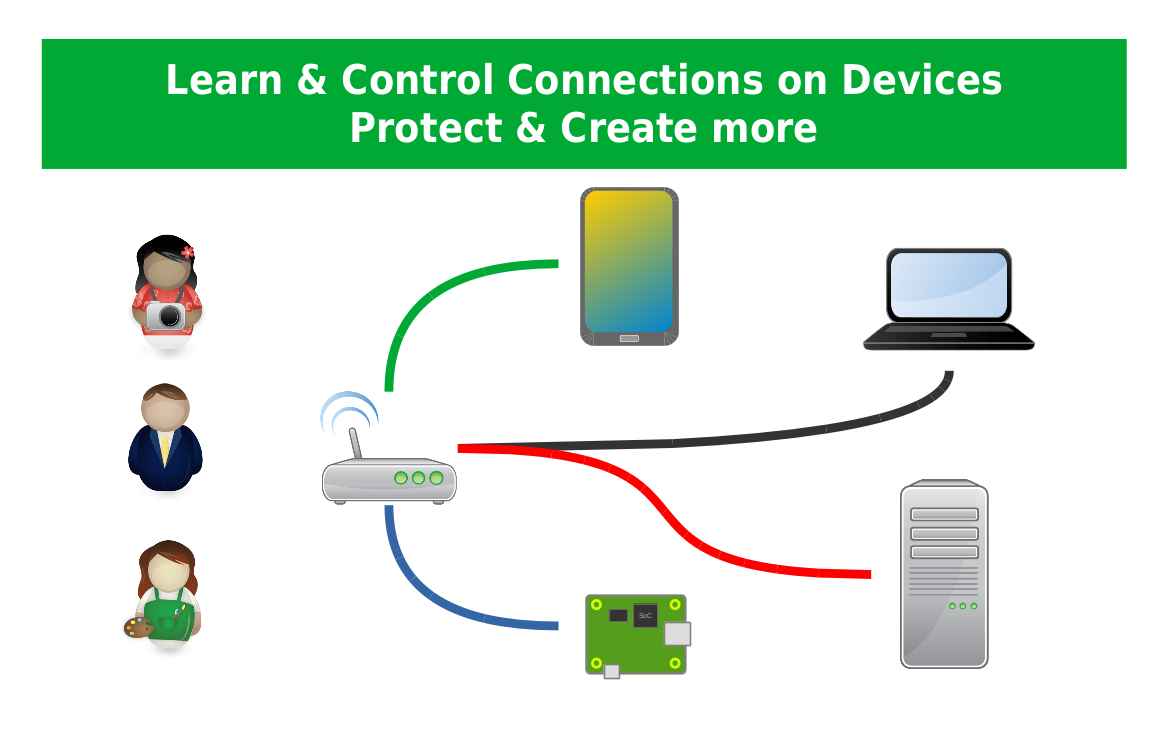
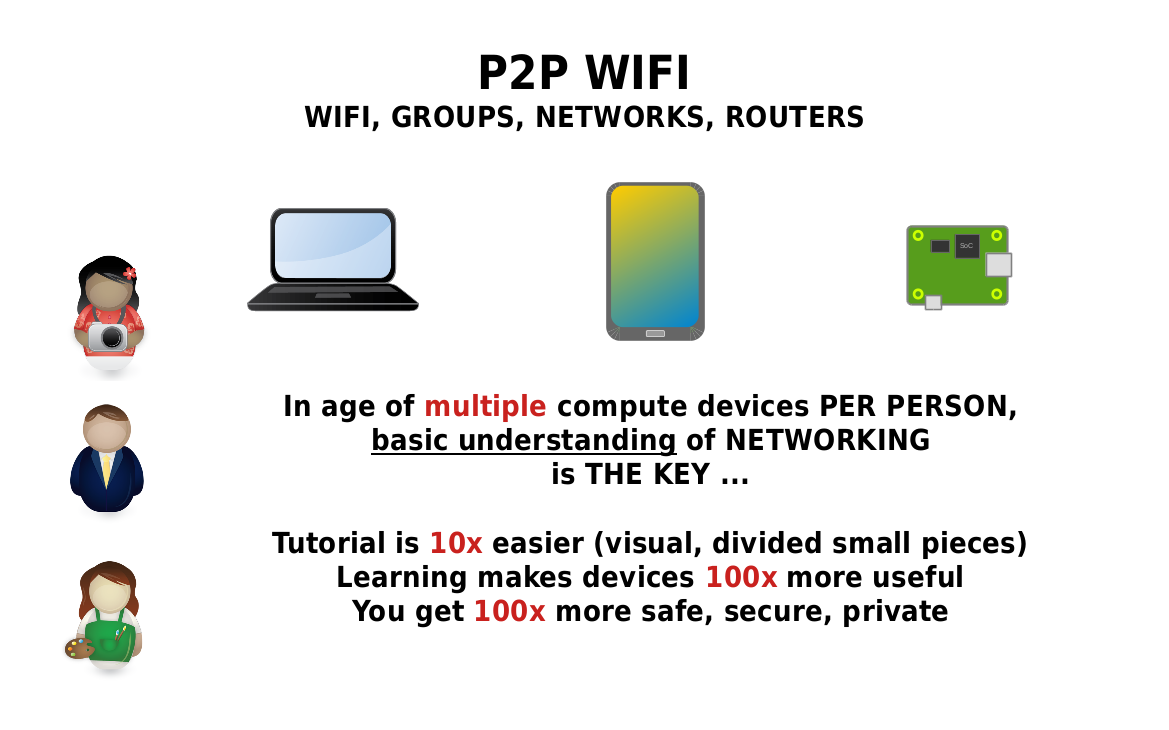
When it comes to securely connecting remote IoT devices, the Raspberry Pi stands out as a versatile and cost-effective solution. It offers powerful hardware capabilities combined with a flexible operating system, making it ideal for IoT applications. By leveraging P2P architecture, you can establish direct communication between devices without relying on centralized servers, thus reducing latency and enhancing security.
Why Choose Raspberry Pi for IoT?
Raspberry Pi is renowned for its adaptability and ease of use in IoT projects. Its compatibility with various operating systems and programming languages allows developers to implement advanced security protocols effortlessly. Additionally, its GPIO pins enable seamless integration with sensors and actuators, expanding its functionality in IoT ecosystems.
Key Benefits of P2P Architecture
- Reduced dependency on cloud servers
- Lower latency in data transmission
- Enhanced security through direct communication
- Scalability for large-scale IoT deployments
Understanding Raspberry Pi Basics
Before diving into the specifics of securely connecting IoT devices, it's essential to understand the fundamentals of Raspberry Pi. This section will cover its hardware specifications, operating systems, and common applications in IoT projects.
Hardware Specifications
Raspberry Pi models come with varying specifications, but most include:
- Quad-core processors
- 1-8 GB RAM
- Multiple USB ports
- HDMI and Ethernet connectivity
Operating Systems
Raspberry Pi supports several operating systems, such as:
- Raspberry Pi OS
- Ubuntu
- Debian
Introduction to IoT and Its Importance
The Internet of Things (IoT) refers to the network of interconnected devices capable of collecting and exchanging data. Its importance lies in its ability to enhance efficiency, automation, and real-time monitoring across various industries.
Read also:Lauren Bgc6 Unveiling The Rising Stars Journey
Applications of IoT
- Smart home automation
- Industrial monitoring systems
- Healthcare wearables
Peer-to-Peer Architecture Explained
Peer-to-peer (P2P) architecture eliminates the need for centralized servers by enabling direct communication between devices. This approach offers numerous advantages, including improved security and reduced latency.
How P2P Works
In a P2P network, each device acts as both a client and a server, allowing them to exchange data directly. This decentralized structure enhances resilience and scalability, making it ideal for IoT applications.
Security Challenges in Remote IoT Connections
Securing remote IoT devices poses several challenges, including unauthorized access, data breaches, and device hijacking. Implementing robust security measures is crucial to mitigate these risks.
Common Security Threats
- Data interception
- Denial-of-service attacks
- Firmware vulnerabilities
Tools and Software You’ll Need
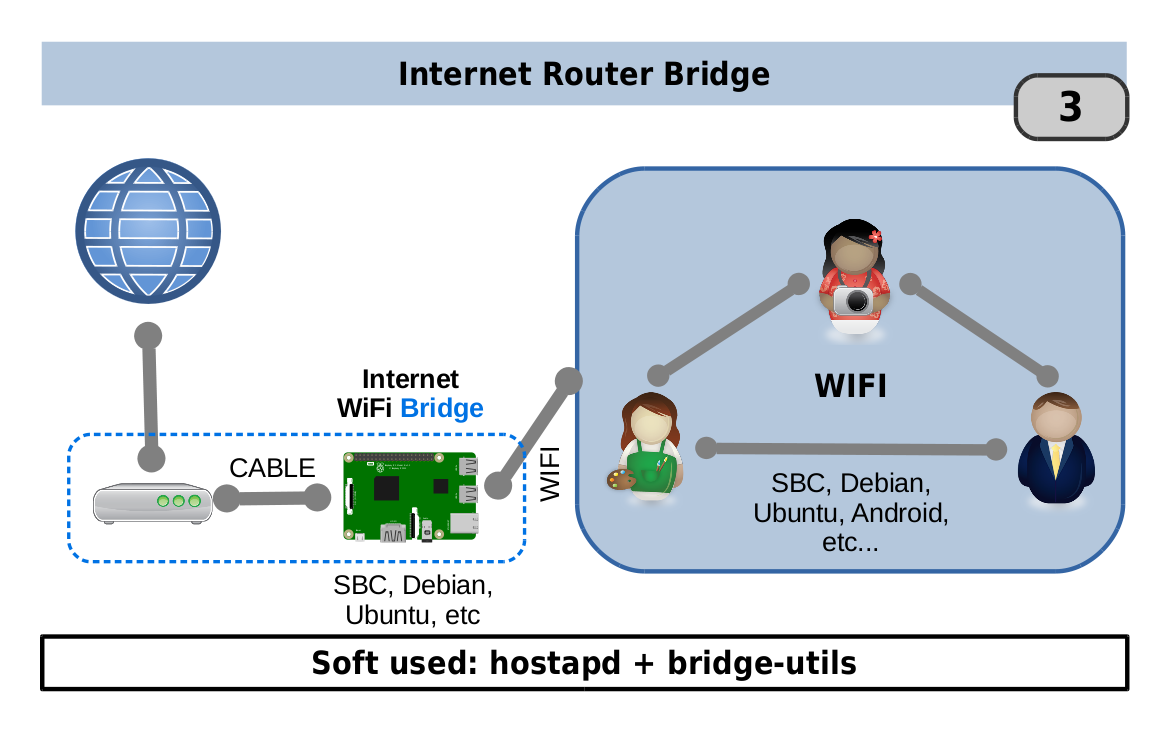
To securely connect remote IoT devices using Raspberry Pi, you’ll need the following tools and software:
- Raspberry Pi board
- Power supply and microSD card
- SSH client for remote access
- Security protocols like TLS and SSH
Step-by-Step Setup Process
This section will walk you through the process of setting up a secure P2P connection for remote IoT devices using Raspberry Pi.
Step 1: Install the Operating System
Begin by installing Raspberry Pi OS on your microSD card. Ensure that the latest version is used for optimal performance and security.
Step 2: Configure Network Settings
Set up Wi-Fi or Ethernet connectivity to enable remote access. Use static IP addresses for consistent communication between devices.
Step 3: Implement Security Protocols
Enable SSH and configure TLS certificates to secure data transmission. Regularly update firmware and software to patch vulnerabilities.
Best Practices for Secure Connections
Adopting best practices is essential for maintaining secure remote IoT connections. Here are some tips to follow:
- Use strong, unique passwords for all devices
- Regularly monitor network activity for suspicious behavior
- Encrypt sensitive data using advanced encryption standards
Troubleshooting Common Issues
Encountering issues during setup is common, but they can be resolved with the right approach. Below are some common problems and their solutions:
- Connection errors: Check network settings and ensure proper hardware configuration
- Authentication failures: Verify SSH keys and update authentication credentials
Future Trends in IoT Security
The future of IoT security lies in advancements such as blockchain technology, artificial intelligence, and quantum encryption. These innovations promise to enhance security measures and address emerging threats.
Blockchain in IoT
Blockchain technology can provide decentralized and tamper-proof data storage, ensuring the integrity of IoT communications.
Artificial Intelligence for Threat Detection
AI-powered systems can detect and respond to security threats in real time, offering proactive protection against attacks.
Conclusion
Securing remote IoT devices through a P2P network using Raspberry Pi is a critical step in creating robust and efficient IoT ecosystems. By following the guidelines outlined in this article, you can establish secure connections while leveraging the full potential of IoT technology. We encourage you to share your thoughts and experiences in the comments section below and explore other articles on our site for further insights.
Thank you for reading, and happy tinkering!