In the era of interconnected devices, securely connecting remote IoT P2P downloads on Android is crucial for safeguarding your digital assets. The Internet of Things (IoT) has revolutionized the way we interact with technology, but it also brings new security challenges. This guide will walk you through the essential steps to ensure your IoT connections remain secure and efficient.
As more people embrace IoT devices, the demand for secure communication between devices grows exponentially. Whether you're a tech enthusiast, a small business owner, or a developer, understanding how to secure IoT peer-to-peer (P2P) connections on Android is vital. This article will provide actionable insights to protect your data and devices.
By the end of this comprehensive guide, you'll have a clear understanding of the best practices for securely connecting remote IoT P2P downloads on Android. Let's dive in and explore how to fortify your IoT ecosystem against potential threats.
Read also:Feb 9th Zodiac Sign Discover The Traits Compatibility And Astrological Insights
Table of Contents:
- Introduction to IoT Security
- Why Secure IoT Connections Matter
- Securing Android IoT Devices
- Understanding P2P in IoT
- The Role of Encryption
- Secure Protocols for IoT
- Common IoT Security Risks
- Solutions for IoT Security Challenges
- Tools for Securely Connecting IoT Devices
- Best Practices for IoT Security
- Conclusion
Introduction to IoT Security
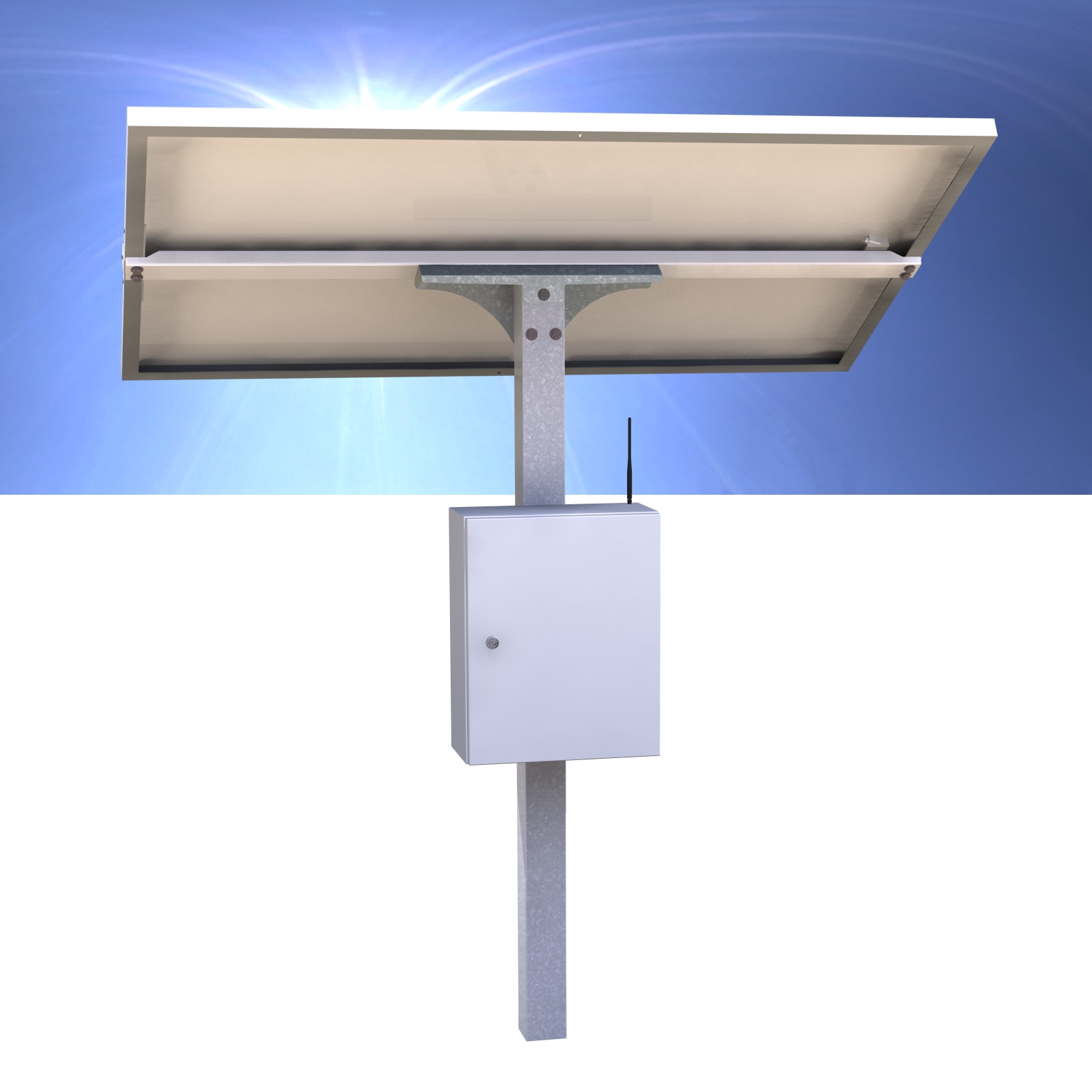
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data. As IoT devices continue to proliferate, securing these connections becomes paramount. Securing remote IoT P2P downloads on Android is a critical step in ensuring data integrity and privacy.
Key Features of IoT Security
IoT security encompasses several key features that protect devices and data from unauthorized access. These include:
- Data encryption
- Authentication mechanisms
- Network segmentation
- Regular firmware updates
Why Secure IoT Connections Matter
Securing IoT connections is essential for protecting sensitive information and maintaining the reliability of connected devices. With the increasing reliance on IoT technology, the risk of cyberattacks rises. Understanding the importance of secure IoT connections is the first step in mitigating these risks.
Impact of Insecure IoT Connections
Insecure IoT connections can lead to:
- Data breaches
- Device hijacking
- Network vulnerabilities
- Financial losses
Securing Android IoT Devices
Android-based IoT devices require specific security measures to ensure their safe operation. By implementing robust security protocols, you can protect your Android IoT devices from potential threats. Securing remote IoT P2P downloads on Android involves several steps, including:
Read also:Karolina Kurkova Height A Comprehensive Look At The Supermodels Iconic Height
Steps to Secure Android IoT Devices
- Using strong passwords and two-factor authentication
- Installing reputable security apps
- Regularly updating device firmware
- Limiting access to trusted networks
Understanding P2P in IoT
Peer-to-peer (P2P) communication in IoT allows devices to exchange data directly without relying on a central server. This method enhances efficiency and reduces latency but requires stringent security measures to prevent unauthorized access. Understanding P2P in IoT is crucial for securely connecting remote IoT P2P downloads on Android.
Advantages of P2P in IoT
P2P communication offers several advantages, including:
- Reduced reliance on central servers
- Improved data transfer speeds
- Enhanced scalability
The Role of Encryption
Encryption plays a vital role in securing IoT connections. By encrypting data transmitted between devices, you can protect sensitive information from interception. Encryption is a cornerstone of securely connecting remote IoT P2P downloads on Android.
Types of Encryption for IoT
Common encryption methods for IoT include:
- Advanced Encryption Standard (AES)
- Transport Layer Security (TLS)
- Secure Sockets Layer (SSL)
Secure Protocols for IoT
Using secure protocols is essential for maintaining the integrity of IoT connections. Protocols such as MQTT, CoAP, and HTTP/2 provide secure and efficient communication between IoT devices. These protocols are crucial for securely connecting remote IoT P2P downloads on Android.
Popular IoT Protocols
Some of the most widely used IoT protocols include:
- MQTT
- CoAP
- HTTP/2
Common IoT Security Risks
IoT devices face several security risks that can compromise their functionality and data integrity. Identifying these risks is the first step in developing effective countermeasures. Common IoT security risks include:
Examples of IoT Security Risks
- Malware infections
- Distributed Denial of Service (DDoS) attacks
- Unauthorized access
Solutions for IoT Security Challenges
Addressing IoT security challenges requires a multifaceted approach. By combining advanced technologies with best practices, you can fortify your IoT ecosystem against potential threats. Solutions for IoT security challenges include:
Effective IoT Security Solutions
- Implementing firewalls and intrusion detection systems
- Using AI-driven security tools
- Conducting regular security audits
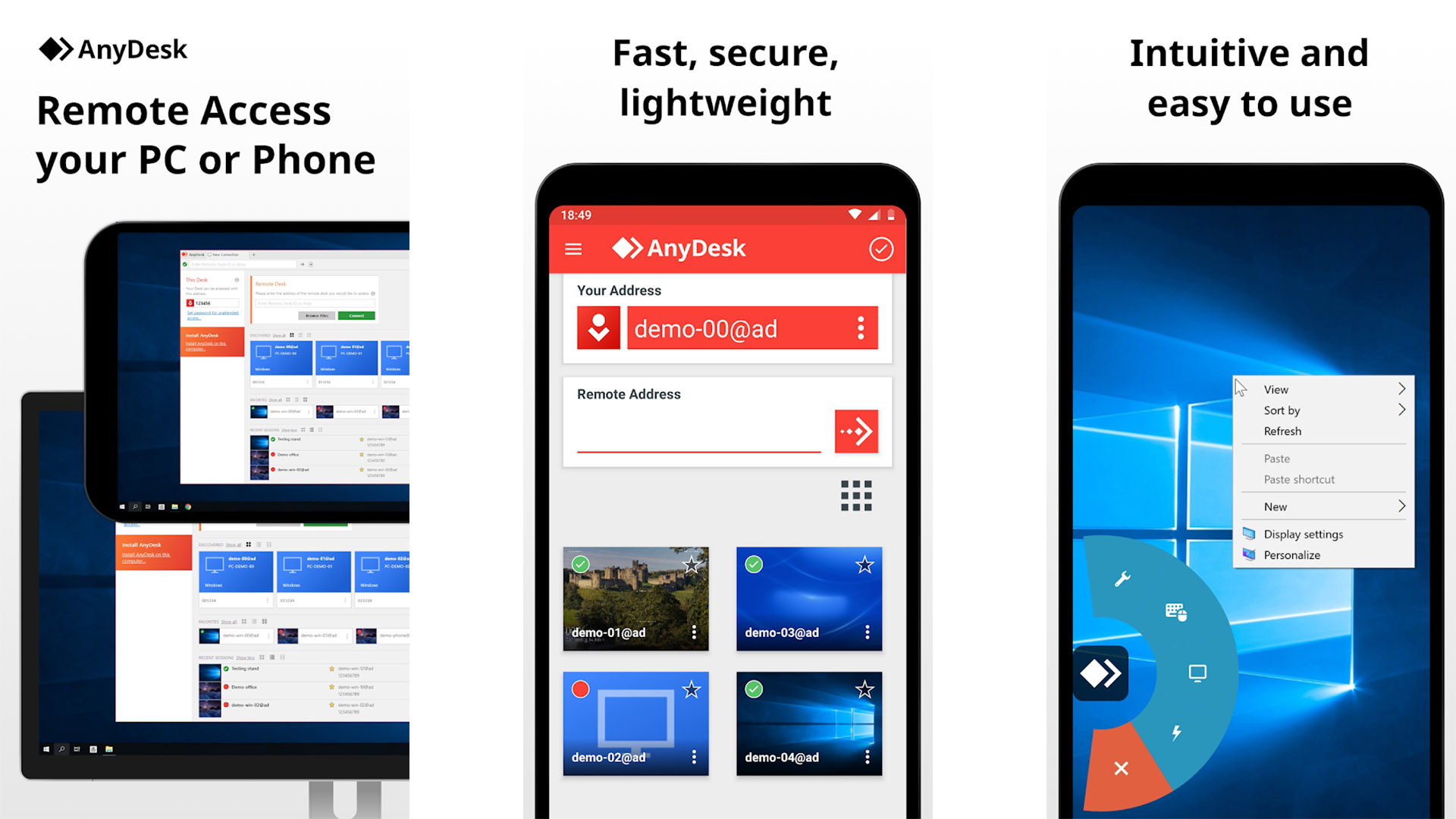
Tools for Securely Connecting IoT Devices
Several tools are available to help secure IoT connections. These tools provide features such as encryption, authentication, and network monitoring. Tools for securely connecting IoT devices include:
Recommended IoT Security Tools
- Wireshark
- OpenSSL
- Snort
Best Practices for IoT Security
Adopting best practices is essential for maintaining the security of IoT devices. By following these guidelines, you can ensure the safe operation of your IoT ecosystem. Best practices for IoT security include:
Essential IoT Security Best Practices
- Regularly updating device firmware
- Using strong, unique passwords
- Limiting device access to trusted networks
Conclusion
Securing remote IoT P2P downloads on Android is a critical aspect of maintaining the integrity of your IoT ecosystem. By understanding the importance of secure IoT connections, implementing robust security measures, and adopting best practices, you can protect your devices and data from potential threats.
We encourage you to take action by implementing the strategies outlined in this guide. Leave a comment below to share your thoughts or ask questions. Don't forget to explore other articles on our site for more insights into IoT security and related topics.
Data sources and references:
- IoT Security Foundation
- National Institute of Standards and Technology (NIST)
- IEEE Communications Magazine