As technology continues to evolve, the importance of secure tunneling for AWS IoT device management cannot be overstated. IoT devices are becoming increasingly integrated into our daily lives, from smart homes to industrial applications. However, ensuring secure communication between these devices and the cloud remains a critical challenge. Secure tunneling is a solution that addresses this challenge, providing a robust framework for data protection and device management.
In the rapidly expanding world of IoT, where billions of devices are connected and exchanging data, security is paramount. Without proper security measures, sensitive information can be intercepted, leading to potential breaches and unauthorized access. AWS IoT provides a powerful platform for managing IoT devices, and secure tunneling plays a pivotal role in safeguarding communication channels.
This article delves into the concept of secure tunneling for AWS IoT device management, exploring its significance, implementation strategies, and best practices. Whether you're a developer, system administrator, or simply someone interested in IoT security, this guide will provide valuable insights to help you understand and implement secure tunneling effectively.
Read also:Cast Of Debbie Does Dallas Exploring The Iconic Films Stars
Table of Contents
- Introduction to Secure Tunneling
- Understanding AWS IoT
- What is Secure Tunneling?
- Benefits of Secure Tunneling for AWS IoT
- Implementing Secure Tunneling
- Best Practices for Secure Tunneling
- Challenges in Secure Tunneling
- Use Cases for Secure Tunneling in AWS IoT
- Comparison with Other Security Protocols
- Future Trends in Secure Tunneling
Introduction to Secure Tunneling
Why Secure Tunneling Matters
Secure tunneling is a fundamental concept in modern network security, especially for IoT ecosystems. It establishes an encrypted communication channel between devices and the cloud, ensuring data integrity and confidentiality. With AWS IoT device management, secure tunneling acts as a protective barrier against potential threats such as data breaches and unauthorized access.
In today's interconnected world, where devices communicate across various networks, secure tunneling ensures that sensitive information remains protected from malicious actors. By encrypting data in transit, secure tunneling minimizes the risk of interception and tampering.
Understanding AWS IoT
Overview of AWS IoT
AWS IoT is a comprehensive platform designed to facilitate secure and scalable communication between IoT devices and the cloud. It provides a range of services, including device registration, data collection, and analytics, all while maintaining robust security measures.
AWS IoT Core, one of its key components, enables bidirectional communication between devices and the cloud. By integrating secure tunneling, AWS IoT ensures that data transmitted between devices and the cloud remains secure and reliable.
What is Secure Tunneling?
Definition and Mechanism
Secure tunneling refers to the process of creating an encrypted communication channel between two endpoints, typically a device and a server. This mechanism ensures that data transmitted through the channel remains confidential and tamper-proof. In the context of AWS IoT device management, secure tunneling uses protocols such as TLS (Transport Layer Security) to establish secure connections.
TLS encrypts data packets at the transport layer, ensuring that even if intercepted, the data cannot be deciphered without the appropriate decryption keys. This makes secure tunneling an essential component of IoT security.
Read also:Stanford Notable Alumni Celebrating The Achievers Who Changed The World
Benefits of Secure Tunneling for AWS IoT
Enhanced Security
- Protects sensitive data from interception and unauthorized access.
- Ensures data integrity by preventing tampering during transmission.
- Reduces the risk of cyberattacks and data breaches.
Scalability
- Supports large-scale IoT deployments with consistent security measures.
- Handles multiple devices and connections without compromising performance.
Implementing Secure Tunneling
Step-by-Step Guide
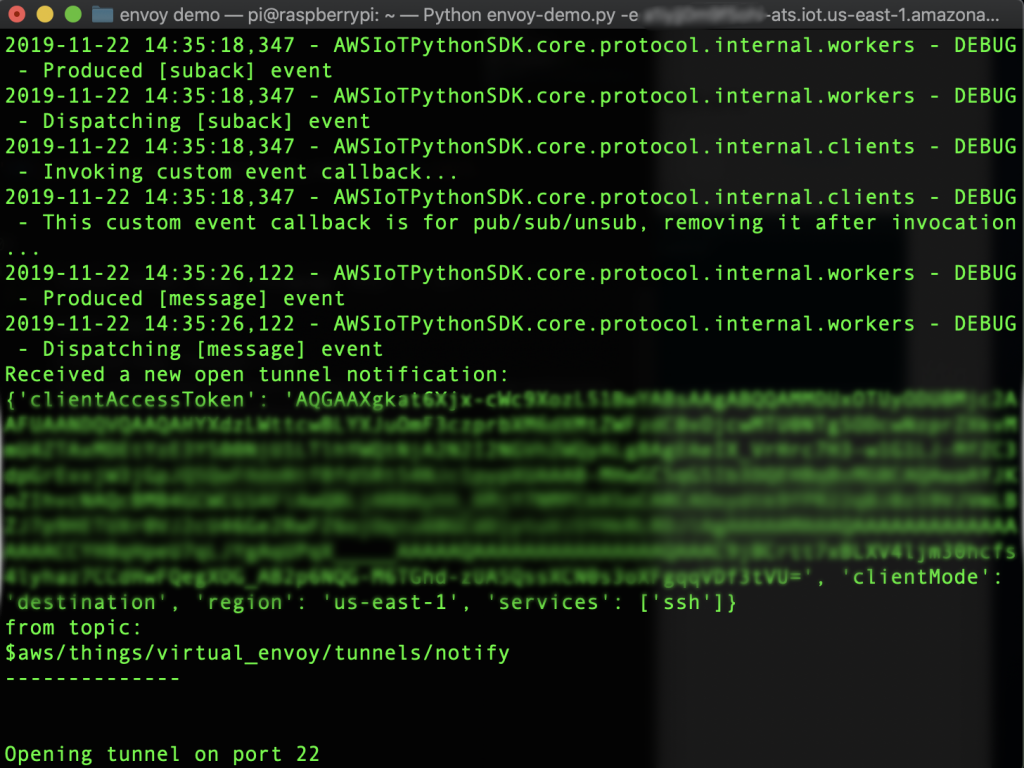
Implementing secure tunneling in AWS IoT involves several key steps:
- Device Registration: Register devices with AWS IoT Core to establish a trusted identity.
- Certificate Management: Generate and manage security certificates for devices to authenticate communication.
- TLS Configuration: Configure TLS settings to ensure encrypted communication channels.
- Monitoring and Logging: Implement monitoring and logging mechanisms to detect and respond to potential security threats.
Best Practices for Secure Tunneling
Key Considerations
- Use strong encryption algorithms to enhance security.
- Regularly update security certificates and keys to prevent vulnerabilities.
- Monitor network traffic for suspicious activities and anomalies.
- Adhere to industry standards and compliance regulations.
Challenges in Secure Tunneling
Common Obstacles
Despite its benefits, secure tunneling in AWS IoT device management presents several challenges:
- Resource Constraints: IoT devices often have limited processing power and memory, making it difficult to implement complex encryption protocols.
- Latency Issues: Encrypted communication can introduce latency, affecting real-time applications.
- Key Management: Managing encryption keys securely and efficiently can be a complex task.
Use Cases for Secure Tunneling in AWS IoT
Real-World Applications
Secure tunneling finds application in various industries, including:
- Smart Homes: Ensuring secure communication between smart appliances and the cloud.
- Industrial IoT: Protecting sensitive data in industrial automation and control systems.
- Healthcare: Safeguarding patient data in connected medical devices.
Comparison with Other Security Protocols
Secure Tunneling vs. Traditional Protocols
While secure tunneling offers robust security features, it is essential to compare it with other protocols:
- SSH (Secure Shell): Primarily used for secure remote access, SSH is less suitable for IoT devices due to its resource-intensive nature.
- SSL (Secure Sockets Layer): An older protocol that has largely been replaced by TLS, SSL lacks some of the advanced features offered by secure tunneling.
Future Trends in Secure Tunneling
Innovations and Advancements
The future of secure tunneling in AWS IoT device management looks promising, with advancements such as:
- Quantum Cryptography: Offering unparalleled security by leveraging quantum mechanics.
- AI-Driven Security: Using artificial intelligence to detect and respond to threats in real-time.
- Edge Computing Integration: Enhancing security by processing data closer to the source.
Conclusion
In conclusion, secure tunneling for AWS IoT device management is a critical component of modern IoT security. By establishing encrypted communication channels, it ensures the protection of sensitive data and facilitates secure device interactions. As IoT continues to evolve, adopting secure tunneling practices will remain essential for safeguarding connected ecosystems.
We encourage you to explore the resources and tools provided by AWS IoT to enhance your understanding and implementation of secure tunneling. Feel free to leave a comment or share this article with others who may benefit from it. For more insights into IoT security, check out our other articles on related topics.
Data sources and references: