Remote login IoT over internet has become a fundamental aspect of modern technology, revolutionizing how we interact with devices across the globe. This capability allows users to access and manage Internet of Things (IoT) devices remotely, providing convenience and efficiency. However, as the demand for remote access grows, so does the importance of ensuring security and reliability in these systems.
The ability to perform remote login IoT over the internet opens up countless possibilities for businesses and individuals alike. From monitoring home security systems to managing industrial equipment, remote access to IoT devices simplifies operations and enhances productivity. Yet, with great convenience comes the need for robust security measures to protect sensitive data and maintain system integrity.
In this article, we will delve deep into the world of remote login IoT over the internet. We will explore the technology behind it, discuss security best practices, and provide actionable insights to help you implement secure remote access solutions. Whether you're a tech enthusiast, a business owner, or an IT professional, this guide will equip you with the knowledge you need to navigate this rapidly evolving field.
Read also:Dracula 2000 Cast The Definitive Guide To The Films Stellar Ensemble
Table of Contents
- Introduction to Remote Login IoT Over Internet
- The Technology Behind Remote Login IoT
- Benefits of Remote Login IoT Over Internet
- Security Challenges in Remote Login IoT
- Best Practices for Secure Remote Login
- Tools and Software for Remote Login IoT
- Network Architecture for Remote Access
- Data Privacy in IoT Remote Login
- Future Trends in Remote Login IoT
- Conclusion and Next Steps
Introduction to Remote Login IoT Over Internet
Remote login IoT over the internet refers to the ability to access and control IoT devices from a distant location using an internet connection. This technology has become increasingly popular due to its versatility and convenience. IoT devices, ranging from smart home appliances to industrial sensors, can now be managed remotely, providing users with greater control and flexibility.
Why Remote Login IoT Matters
The significance of remote login IoT over the internet lies in its ability to streamline operations and reduce costs. For instance, businesses can monitor and maintain critical infrastructure without the need for on-site personnel. Similarly, individuals can manage their smart home devices from anywhere in the world, enhancing their quality of life.
Key Components of Remote Login IoT
- IoT Devices: Sensors, cameras, and other connected devices.
- Network Connectivity: Reliable internet connection to facilitate communication.
- Authentication Mechanisms: Secure methods to verify user identity.
- Remote Access Software: Tools and platforms that enable remote control.
The Technology Behind Remote Login IoT
Understanding the technology behind remote login IoT over the internet is crucial for implementing effective solutions. This section explores the core components and mechanisms that enable remote access to IoT devices.
Communication Protocols
Several communication protocols are commonly used in remote login IoT systems, including:
- MQTT: A lightweight protocol ideal for low-bandwidth environments.
- HTTP/HTTPS: Standard protocols for web-based communication.
- WebSocket: A protocol that allows real-time, bidirectional communication.
Cloud Computing
Cloud computing plays a vital role in remote login IoT over the internet. It provides the infrastructure needed to store and process data, enabling seamless communication between devices and users. Popular cloud platforms such as AWS IoT, Microsoft Azure, and Google Cloud offer robust solutions for IoT remote access.
Benefits of Remote Login IoT Over Internet
The advantages of remote login IoT over the internet are numerous and varied. Below are some of the key benefits:
Read also:Lauren Bgc6 Unveiling The Rising Stars Journey
- Increased Efficiency: Streamline operations by managing devices remotely.
- Cost Savings: Reduce the need for on-site personnel and travel expenses.
- Enhanced Flexibility: Access devices from anywhere, at any time.
- Improved Monitoring: Monitor device performance and receive real-time alerts.
Security Challenges in Remote Login IoT
While remote login IoT over the internet offers many benefits, it also presents significant security challenges. These challenges must be addressed to ensure the safety and integrity of IoT systems.
Common Security Threats
- Unauthorized Access: Hackers attempting to gain access to IoT devices.
- Data Breaches: Sensitive information being compromised during transmission.
- Malware Attacks: Malicious software targeting IoT devices.
Strategies to Mitigate Risks
Implementing robust security measures is essential to protect against these threats. This includes using strong authentication methods, encrypting data, and regularly updating software.
Best Practices for Secure Remote Login
Adopting best practices is crucial for ensuring secure remote login IoT over the internet. Below are some recommendations:
- Use Multi-Factor Authentication (MFA) to verify user identity.
- Encrypt data during transmission using protocols like TLS/SSL.
- Regularly update firmware and software to patch vulnerabilities.
- Limit access to authorized personnel only.
Tools and Software for Remote Login IoT
A variety of tools and software are available to facilitate remote login IoT over the internet. These solutions cater to different needs and requirements, making it easier to implement secure remote access.
Popular Remote Access Software
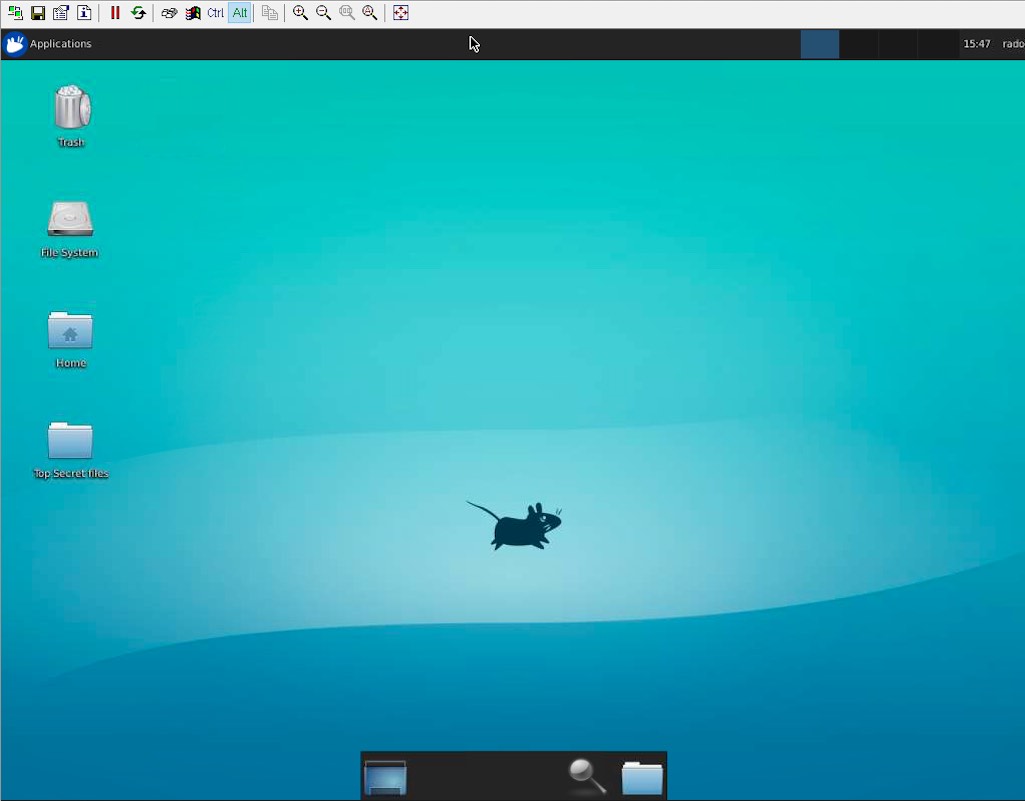
- TeamViewer: A widely used tool for remote access and support.
- AnyDesk: A fast and secure remote desktop solution.
- Windows Remote Desktop: A built-in feature for Windows users.
IoT Platforms
IoT platforms such as AWS IoT Core, Microsoft Azure IoT Hub, and Google Cloud IoT Core provide comprehensive solutions for managing IoT devices and enabling remote access.
Network Architecture for Remote Access
Designing an effective network architecture is essential for secure remote login IoT over the internet. This involves configuring firewalls, setting up virtual private networks (VPNs), and implementing network segmentation.
Firewall Configuration
Firewalls play a critical role in protecting IoT devices from unauthorized access. Proper configuration ensures that only legitimate traffic is allowed to pass through.
Virtual Private Networks (VPNs)
VPNs provide a secure tunnel for communication between devices and users, encrypting data and protecting it from interception.
Data Privacy in IoT Remote Login
Data privacy is a growing concern in the realm of remote login IoT over the internet. Organizations must comply with regulations such as GDPR and CCPA to protect user data and maintain trust.
Compliance with Regulations
Understanding and adhering to data privacy regulations is crucial for ensuring legal compliance and safeguarding user information.
Data Encryption
Encrypting data both at rest and in transit is a fundamental practice for maintaining data privacy in IoT remote login systems.
Future Trends in Remote Login IoT
The future of remote login IoT over the internet is bright, with several emerging trends set to shape the industry. These include advancements in artificial intelligence, the rise of 5G technology, and the integration of blockchain for enhanced security.
Artificial Intelligence
AI-powered solutions are revolutionizing remote login IoT by enabling predictive maintenance and intelligent decision-making.
5G Technology
The rollout of 5G networks promises faster and more reliable connectivity, paving the way for more advanced IoT applications.
Conclusion and Next Steps
Remote login IoT over the internet has transformed the way we interact with connected devices, offering unparalleled convenience and efficiency. However, with this convenience comes the responsibility to ensure security and privacy. By following the best practices outlined in this guide and staying informed about emerging trends, you can harness the full potential of remote login IoT while safeguarding your systems and data.
We encourage you to take action by implementing secure remote access solutions and exploring the tools and platforms available. Share your thoughts and experiences in the comments below, and don't forget to explore other articles on our site for more insights into the world of IoT and technology.