In the rapidly evolving world of technology, IoT SSH Tunnel AWS has become a crucial element for secure communication between devices in the Internet of Things (IoT) ecosystem. As more devices become connected, ensuring secure data transfer is no longer optional but a necessity. This article will provide a deep dive into the concept of IoT SSH Tunnel AWS, exploring its significance, implementation, and best practices.
The integration of IoT with cloud platforms like AWS opens up a world of possibilities for businesses and developers alike. However, with these opportunities come challenges, particularly concerning data security and privacy. IoT SSH Tunnel AWS addresses these concerns by creating a secure communication channel for IoT devices.
This guide is designed for developers, IT professionals, and anyone interested in understanding how IoT SSH Tunnel AWS works. By the end of this article, you will have a solid understanding of the concept, its implementation, and why it is essential for modern IoT applications.
Read also:Think Like A Man Too Cast A Comprehensive Guide To The Stars Behind The Scenes
Below is a detailed table of contents to help you navigate through the article:
- What is IoT SSH Tunnel AWS?
- Importance of Secure Communication in IoT
- How Does SSH Tunnel Work?
- Integrating SSH Tunnel with AWS
- Benefits of Using IoT SSH Tunnel AWS
- Common Implementation Challenges
- Best Practices for Secure IoT Communication
- Use Cases of IoT SSH Tunnel AWS
- Future Trends in IoT and AWS
- Conclusion and Call to Action
What is IoT SSH Tunnel AWS?
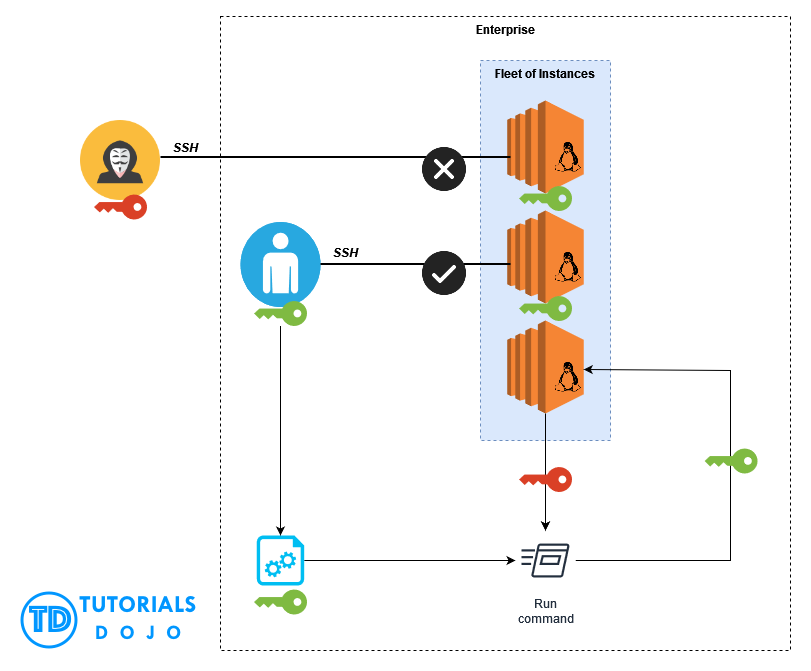
IoT SSH Tunnel AWS refers to the use of Secure Shell (SSH) tunnels to facilitate secure communication between IoT devices and AWS cloud services. SSH tunnels encrypt data transmitted between devices and servers, ensuring that sensitive information remains protected from unauthorized access.
This method is particularly important in IoT applications where devices often communicate over public networks, making them vulnerable to cyber threats. By leveraging AWS's robust infrastructure, organizations can enhance the security and reliability of their IoT deployments.
Key Features of IoT SSH Tunnel AWS
- Encryption: Data transmitted through SSH tunnels is encrypted, providing an additional layer of security.
- Authentication: IoT SSH Tunnel AWS ensures that only authorized devices and users can access the network.
- Scalability: AWS's infrastructure allows for seamless scaling of IoT applications, accommodating growing demands.
Importance of Secure Communication in IoT
As IoT continues to expand, the need for secure communication becomes increasingly critical. With billions of interconnected devices, the risk of data breaches and cyberattacks is significant. IoT SSH Tunnel AWS plays a vital role in mitigating these risks by ensuring that data remains secure during transmission.
Secure communication is not just about protecting sensitive information; it also ensures the integrity and reliability of IoT systems. Organizations that prioritize security can build trust with their customers and stakeholders, ultimately leading to long-term success.
Statistical Evidence of IoT Security Risks
According to a report by Gartner, by 2025, over 75% of organizations will experience an IoT-based security breach. This highlights the urgency of implementing robust security measures like IoT SSH Tunnel AWS to safeguard IoT ecosystems.
Read also:Brianne Oconnor Age A Comprehensive Look At Her Life And Achievements
How Does SSH Tunnel Work?
An SSH tunnel creates an encrypted connection between a client and a server, allowing data to be transmitted securely over untrusted networks. In the context of IoT SSH Tunnel AWS, this means that IoT devices can communicate with AWS services without exposing sensitive information to potential attackers.
The process involves establishing an SSH session between the client (IoT device) and the server (AWS instance). Once the session is established, data is encapsulated within the SSH protocol, ensuring that it remains encrypted during transmission.
Steps to Establish an SSH Tunnel
- Generate SSH keys for authentication.
- Configure the IoT device to connect to the AWS instance using the SSH protocol.
- Set up port forwarding to allow data to pass through the tunnel.
Integrating SSH Tunnel with AWS
Integrating SSH Tunnel with AWS involves setting up an EC2 instance to act as the server endpoint for the tunnel. This instance serves as the gateway between IoT devices and other AWS services, such as S3, DynamoDB, or Lambda.
To integrate SSH Tunnel with AWS, follow these steps:
- Create an EC2 instance with the necessary security groups and permissions.
- Install and configure the SSH server on the EC2 instance.
- Set up port forwarding rules to direct traffic from IoT devices to the appropriate AWS services.
Benefits of Using AWS for SSH Tunnel
- Global Infrastructure: AWS provides a global network of data centers, ensuring low latency and high availability.
- Managed Services: AWS offers a range of managed services that simplify the deployment and management of IoT applications.
- Scalability: AWS allows organizations to scale their IoT deployments as needed, accommodating growth without compromising performance.
Benefits of Using IoT SSH Tunnel AWS
Implementing IoT SSH Tunnel AWS offers several advantages for organizations looking to enhance the security and efficiency of their IoT applications. Some of the key benefits include:
- Enhanced Security: By encrypting data transmissions, IoT SSH Tunnel AWS ensures that sensitive information remains protected from unauthorized access.
- Improved Reliability: Secure communication reduces the risk of data loss or corruption, ensuring that IoT systems operate reliably.
- Cost Efficiency: Leveraging AWS's infrastructure can help organizations reduce costs associated with maintaining on-premises servers and networking equipment.
Common Implementation Challenges
While IoT SSH Tunnel AWS offers numerous benefits, there are challenges that organizations may encounter during implementation. These include:
- Complexity: Setting up and managing SSH tunnels can be complex, requiring specialized knowledge and expertise.
- Performance: Encrypted communication may introduce latency, impacting the performance of IoT applications.
- Scalability: As the number of IoT devices grows, managing SSH tunnels can become challenging without proper planning and infrastructure.
Strategies to Overcome Challenges
To address these challenges, organizations can adopt strategies such as automating SSH key management, optimizing network configurations, and leveraging AWS's advanced features for scalability and performance.
Best Practices for Secure IoT Communication
To ensure the security and reliability of IoT SSH Tunnel AWS, organizations should follow best practices, including:
- Regular Key Rotation: Rotate SSH keys periodically to minimize the risk of unauthorized access.
- Access Control: Implement strict access controls to ensure that only authorized devices and users can access the network.
- Monitoring and Logging: Monitor network activity and maintain logs to detect and respond to potential security threats.
Use Cases of IoT SSH Tunnel AWS
IoT SSH Tunnel AWS has a wide range of applications across various industries. Some common use cases include:
- Smart Home Automation: Secure communication between smart home devices and cloud services.
- Industrial IoT: Protecting data transmissions in industrial environments where security is paramount.
- Healthcare IoT: Ensuring the privacy and security of patient data in connected healthcare systems.
Future Trends in IoT and AWS
As technology continues to evolve, the future of IoT SSH Tunnel AWS looks promising. Emerging trends such as edge computing, 5G networks, and AI-driven analytics are expected to further enhance the capabilities of IoT applications. AWS is actively investing in these areas, providing organizations with the tools and resources needed to stay ahead in the rapidly changing landscape of IoT.
Predictions for IoT and AWS
Experts predict that by 2030, IoT will become even more integrated into everyday life, with AWS playing a central role in enabling secure and scalable IoT deployments. Organizations that embrace these advancements will be well-positioned to capitalize on the opportunities presented by the IoT revolution.
Conclusion and Call to Action
In conclusion, IoT SSH Tunnel AWS is a powerful solution for ensuring secure communication in IoT applications. By leveraging AWS's robust infrastructure and advanced security features, organizations can protect their IoT ecosystems from cyber threats while maintaining performance and scalability.
We invite you to take action by implementing the strategies and best practices discussed in this article. Share your thoughts and experiences in the comments section below, and don't forget to explore other articles on our website for more insights into IoT and cloud computing.
Stay informed, stay secure, and embrace the future of IoT SSH Tunnel AWS!