Setting up IoT remote SSH is a critical process that allows you to manage and control your devices from anywhere in the world. As the Internet of Things (IoT) continues to expand, remote access has become essential for monitoring and maintaining connected devices. However, ensuring the security of your IoT setup is paramount to protect sensitive data and prevent unauthorized access.
In this guide, we will explore the ins and outs of configuring IoT remote SSH securely. Whether you're a beginner or an experienced user, understanding the best practices for setting up IoT remote SSH will help you avoid common pitfalls and ensure your devices remain protected.
By the end of this article, you'll have a thorough understanding of the tools, configurations, and security measures required to establish a reliable IoT remote SSH setup. Let's dive in!
Read also:51 Celebrities Discovering The Worlds Short But Talented Stars
Contents:
- Introduction to IoT and SSH
- IoT Remote SSH Setup Process
- Security Best Practices for IoT SSH
- Tools Required for IoT SSH Setup
- Configuration Steps for IoT SSH
- Troubleshooting IoT SSH Issues
- Performance Optimization Tips
- Automating IoT SSH Processes
- Advanced Security Measures for IoT SSH
- Conclusion and Next Steps
Introduction to IoT and SSH
What is IoT?
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity to exchange data with other devices and systems over the internet. From smart home appliances to industrial machinery, IoT devices are transforming the way we interact with technology.
What is SSH?
Secure Shell (SSH) is a cryptographic network protocol used to securely operate network services over an unsecured network. It provides a secure channel for remote access and management of devices, making it ideal for IoT applications.
Why Use IoT Remote SSH?
IoT remote SSH allows administrators to access and manage IoT devices remotely, enabling efficient troubleshooting, configuration updates, and system monitoring. This capability is especially valuable for devices deployed in remote or inaccessible locations.
IoT Remote SSH Setup Process
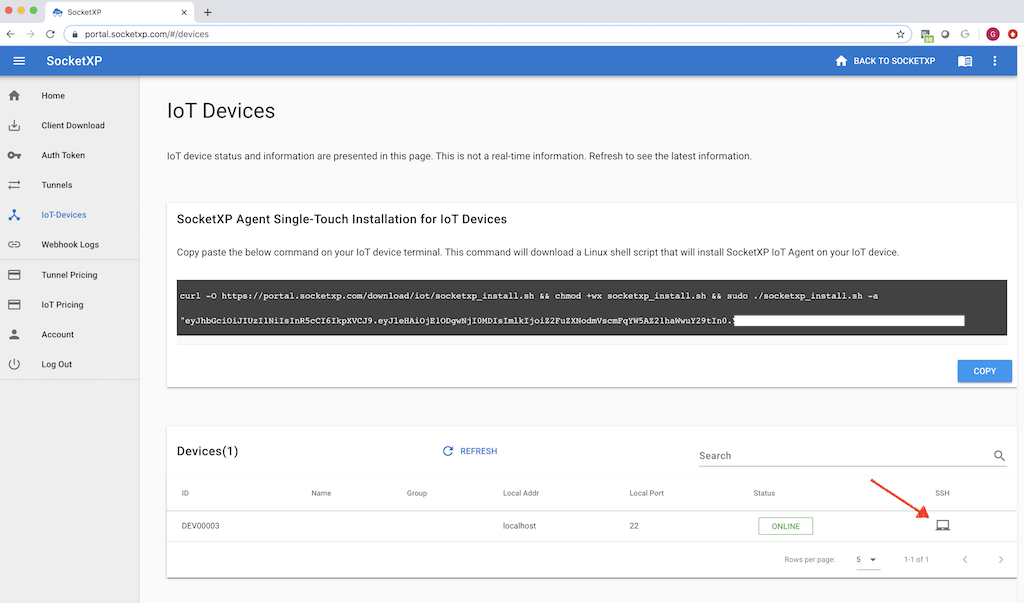
Setting up IoT remote SSH involves several key steps to ensure both functionality and security. Below, we outline the process in detail:
- Identify the devices that require remote access.
- Install an SSH server on each IoT device.
- Configure firewall settings to allow SSH traffic.
- Set up port forwarding on your router if necessary.
- Test the connection from a remote location.
Security Best Practices for IoT SSH
Security is a top priority when setting up IoT remote SSH. Here are some best practices to follow:
Read also:Discover Your February 9 Zodiac Sign And Its Unique Traits
Use Strong Passwords
Create complex passwords or use SSH keys for authentication to enhance security. Avoid using default credentials provided by manufacturers.
Enable Two-Factor Authentication (2FA)
Two-factor authentication adds an extra layer of security by requiring users to provide two forms of identification before gaining access.
Regularly Update Firmware
Keep your IoT devices and SSH server software up to date with the latest security patches and updates to protect against vulnerabilities.
Tools Required for IoT SSH Setup
To successfully configure IoT remote SSH, you'll need the following tools:
- An SSH client (e.g., PuTTY, OpenSSH).
- A router with port forwarding capabilities.
- A domain name or dynamic DNS service for easier access.
- Firewall software to control incoming and outgoing traffic.
Configuration Steps for IoT SSH
Follow these step-by-step instructions to configure IoT remote SSH:
Step 1: Install an SSH Server
Begin by installing an SSH server on your IoT device. For Linux-based devices, you can use OpenSSH, which is widely supported and easy to configure.
Step 2: Configure Firewall Settings
Adjust your firewall settings to allow SSH traffic on port 22 (or a custom port if you choose to change it). Ensure that only trusted IP addresses have access to the SSH server.
Step 3: Set Up Port Forwarding
If your IoT device is behind a NAT router, configure port forwarding to direct incoming SSH traffic to the correct internal IP address.
Troubleshooting IoT SSH Issues
Encountering issues during the setup process is common. Here are some common problems and their solutions:
- Connection Refused: Check if the SSH server is running and verify firewall settings.
- Authentication Failed: Ensure you're using the correct username and password or SSH key.
- Timeout Errors: Verify network connectivity and port forwarding configuration.
Performance Optimization Tips
To ensure optimal performance of your IoT remote SSH setup, consider the following tips:
Optimize Network Bandwidth
Limit bandwidth usage by disabling unnecessary services and optimizing data transfer protocols.
Use Compression
Enable SSH compression to reduce the amount of data transmitted over the network, improving speed and efficiency.
Automating IoT SSH Processes
Automation can significantly streamline IoT remote SSH management. Use tools like Ansible or Shell scripts to automate routine tasks such as:
- Configuration updates.
- Backup and recovery processes.
- Monitoring and alerting systems.
Advanced Security Measures for IoT SSH
For added security, consider implementing the following advanced measures:
Change Default SSH Port
Move SSH from the default port 22 to a non-standard port to reduce the risk of automated attacks.
Implement IP Whitelisting
Restrict access to your SSH server by allowing only specific IP addresses to connect.
Monitor Logs Regularly
Regularly review SSH logs to detect and respond to suspicious activity promptly.
Conclusion and Next Steps
In conclusion, setting up IoT remote SSH is a powerful way to manage and control your connected devices securely. By following the steps outlined in this guide and adhering to best practices, you can ensure a robust and reliable setup.
We encourage you to take action by implementing these strategies in your own IoT environment. Share your experiences and questions in the comments below, and don't forget to explore other resources on our site for further learning.
References: