Managing IoT devices behind a firewall has become one of the most critical challenges for modern IT administrators and cybersecurity professionals. As the Internet of Things (IoT) continues to grow, ensuring secure and efficient management of these devices is no longer optional but a necessity. Firewalls play a pivotal role in protecting networks from unauthorized access, but they also complicate the process of managing IoT devices.
IoT devices are increasingly integrated into various sectors, from healthcare to manufacturing and smart homes. However, these devices often lack robust security features, making them potential entry points for cyber threats. Properly managing IoT devices behind a firewall ensures that they remain secure while maintaining optimal performance.
In this comprehensive guide, we will explore strategies, best practices, and tools for managing IoT devices securely behind a firewall. By the end of this article, you'll have a thorough understanding of the challenges involved and actionable solutions to overcome them.
Read also:Unveiling The Ice Age 3 Voice Actors A Comprehensive Look Into Their Talents
Table of Contents
- Introduction to IoT Devices
- Understanding Firewalls
- Challenges in Managing IoT Devices Behind a Firewall
- Best Practices for Managing IoT Devices
- Tools for Managing IoT Devices
- Enhancing Security for IoT Devices
- The Importance of Network Segmentation
- Regular Updates and Maintenance
- Monitoring IoT Device Activity
- Conclusion and Call to Action
Introduction to IoT Devices
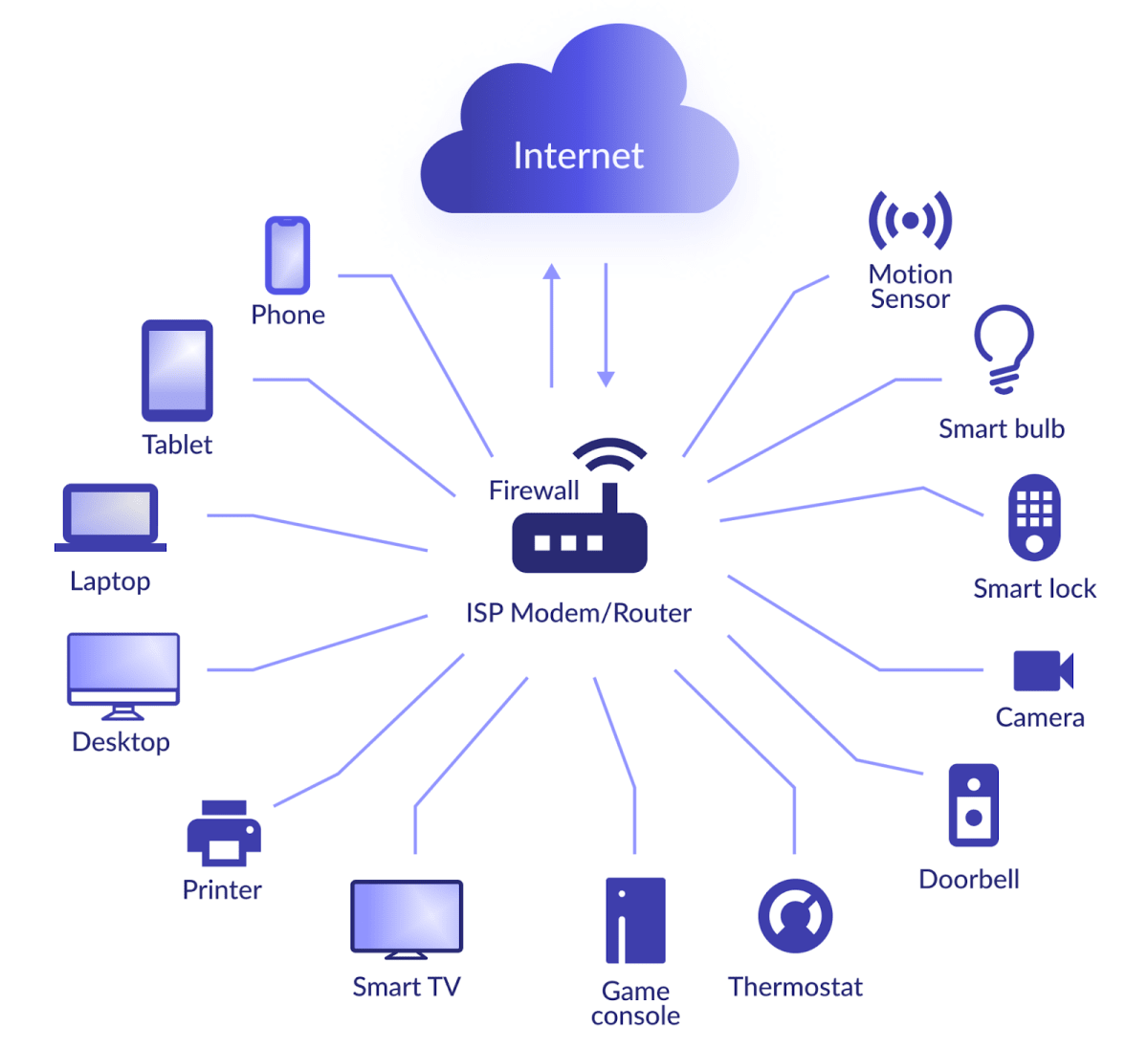
IoT devices refer to any physical objects embedded with sensors, software, and connectivity features that allow them to exchange data with other devices and systems over the internet. These devices range from simple household appliances like smart thermostats to complex industrial machinery.
The rapid adoption of IoT devices has revolutionized how we interact with technology, offering convenience, efficiency, and automation. However, the integration of IoT devices into corporate networks introduces new security risks. Understanding the nature and capabilities of these devices is crucial for effective management.
Some common types of IoT devices include:
- Smart home devices (e.g., smart locks, cameras, and lighting)
- Industrial IoT devices (e.g., sensors, controllers, and actuators)
- Wearable devices (e.g., fitness trackers and smartwatches)
- Healthcare devices (e.g., remote monitoring devices and medical implants)
Understanding Firewalls
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a barrier between trusted internal networks and untrusted external networks, such as the internet.
Firewalls can be hardware-based, software-based, or a combination of both. They play a vital role in protecting IoT devices by filtering out malicious traffic and unauthorized access attempts. However, managing IoT devices behind a firewall requires careful configuration to ensure that legitimate traffic is not blocked.
Types of Firewalls
There are several types of firewalls, each with its own strengths and weaknesses:
Read also:Amatuer Facials
- Packet-filtering firewalls: Analyze individual packets of data and decide whether to allow or block them based on predefined rules.
- Stateful inspection firewalls: Track the state of active connections and use this information to make more informed decisions.
- Application-layer firewalls: Inspect traffic at the application layer, providing more granular control over specific applications and protocols.
Challenges in Managing IoT Devices Behind a Firewall
Managing IoT devices behind a firewall presents several challenges that IT administrators must address:
- Limited security features: Many IoT devices lack robust security features, making them vulnerable to attacks.
- Complex network configurations: IoT devices often require specific network settings, which can be difficult to configure within a firewall.
- Resource constraints: IoT devices typically have limited processing power and memory, which can make it challenging to implement advanced security measures.
Addressing these challenges requires a combination of strategic planning, technical expertise, and the right tools.
Best Practices for Managing IoT Devices
Implementing best practices is essential for effectively managing IoT devices behind a firewall. Here are some key strategies:
1. Device Discovery and Inventory
Begin by identifying all IoT devices on your network and maintaining an up-to-date inventory. This includes recording device types, firmware versions, and network configurations.
2. Secure Authentication
Ensure that all IoT devices require secure authentication before accessing the network. This can be achieved through methods such as username/password combinations, multi-factor authentication (MFA), or digital certificates.
3. Regular Audits
Conduct regular audits of your IoT devices to identify potential vulnerabilities and ensure compliance with security policies.
Tools for Managing IoT Devices
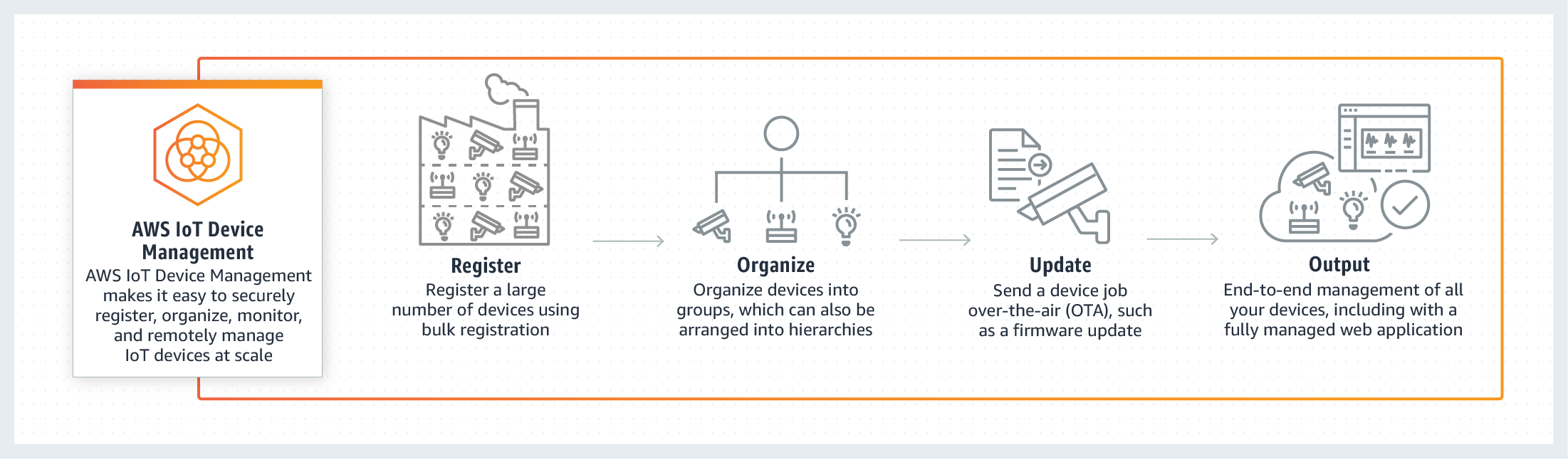
Several tools are available to assist with managing IoT devices behind a firewall:
- Device management platforms: These platforms provide centralized control over IoT devices, allowing administrators to configure settings, monitor activity, and apply updates.
- Network monitoring tools: Tools like Wireshark and Nagios can help monitor network traffic and detect anomalies in IoT device behavior.
- Firewall management software: Solutions such as Palo Alto Networks and Fortinet offer advanced features for managing firewalls and securing IoT devices.
Enhancing Security for IoT Devices
Securing IoT devices behind a firewall involves implementing multiple layers of protection:
Data Encryption
Encrypting data transmitted between IoT devices and other systems ensures that sensitive information remains confidential. Use protocols such as TLS/SSL for secure communication.
Intrusion Detection and Prevention
Deploy intrusion detection and prevention systems (IDPS) to monitor for and respond to suspicious activity on your network.
Access Control
Implement strict access control policies to limit who can interact with IoT devices and what actions they can perform.
The Importance of Network Segmentation
Network segmentation involves dividing a network into smaller, isolated segments. This approach helps contain potential security breaches and reduces the attack surface for IoT devices. By placing IoT devices in their own segment, you can apply specific security rules and monitor traffic more effectively.
Benefits of network segmentation include:
- Improved security
- Enhanced performance
- Simplified management
Regular Updates and Maintenance
Keeping IoT devices up to date with the latest firmware and security patches is critical for maintaining their security. Manufacturers frequently release updates to address known vulnerabilities and improve device functionality.
Develop a regular maintenance schedule to ensure that all devices receive updates promptly. Consider automating this process where possible to reduce the administrative burden.
Monitoring IoT Device Activity
Continuous monitoring of IoT device activity is essential for detecting and responding to potential security threats. Use tools such as SIEM (Security Information and Event Management) systems to aggregate and analyze data from multiple sources.
Key indicators to monitor include:
- Unusual traffic patterns
- Failed login attempts
- Configuration changes
Conclusion and Call to Action
Managing IoT devices behind a firewall is a complex but necessary task for ensuring the security and performance of modern networks. By following the strategies and best practices outlined in this article, you can effectively manage IoT devices while minimizing risks.
We encourage you to take action by implementing the recommendations discussed and sharing this article with your colleagues. Your feedback and questions are valuable, so please leave a comment below or explore other articles on our site for more insights into IoT and cybersecurity.
References: