Virtual Network Computing (VNC) is a powerful tool that allows users to remotely control another computer, but it also comes with security risks if not properly configured. As remote work and digital collaboration become more prevalent, securing VNC connections is essential to protect sensitive data and maintain system integrity. This guide will walk you through the steps to better secure VNC, ensuring your remote connections remain safe from potential threats.
While VNC offers convenience and flexibility, its default settings may not provide adequate protection against unauthorized access or cyberattacks. Understanding the vulnerabilities associated with VNC and implementing robust security measures can significantly enhance the safety of your remote sessions.
In this article, we will explore various strategies to improve VNC security, including encryption methods, authentication protocols, and best practices for configuration. By following these recommendations, you can minimize risks and ensure that your remote connections remain secure.
Read also:Sophie Thavet A Rising Star In The Entertainment Industry
Understanding VNC and Its Security Challenges
What is VNC and How Does It Work?
VNC is a graphical desktop-sharing system that allows users to remotely control another computer over a network or the internet. It transmits keyboard and mouse events from one computer to another, enabling real-time interaction as if the user were physically present at the remote machine.
However, VNC's default setup often lacks strong security features, making it vulnerable to unauthorized access, data interception, and other cybersecurity threats. Without proper configuration, VNC can expose sensitive information and compromise system security.
Common VNC Security Risks
Some of the most common security risks associated with VNC include:
- Weak Passwords: Using simple or easily guessable passwords can allow attackers to gain unauthorized access to your VNC sessions.
- Unencrypted Connections: Without encryption, data transmitted between the local and remote machines can be intercepted by malicious actors.
- Inadequate Authentication: Relying solely on basic password authentication may not provide sufficient protection against sophisticated cyberattacks.
- Open Ports: Leaving VNC ports open to the internet without proper firewall rules can expose your system to potential intrusions.
Implementing Strong Authentication for VNC
Why Authentication Matters in VNC Security
Authentication is a critical component of securing VNC connections. It ensures that only authorized users can access remote systems, reducing the risk of unauthorized access and data breaches.
Best Practices for VNC Authentication
To enhance VNC security through authentication, consider the following best practices:
- Use strong, complex passwords that include a mix of uppercase and lowercase letters, numbers, and special characters.
- Implement multi-factor authentication (MFA) to add an extra layer of security beyond just passwords.
- Regularly update and rotate passwords to prevent credential theft and unauthorized access.
- Restrict access to specific IP addresses or networks to limit potential attackers' ability to connect to your VNC server.
Encrypting VNC Connections
The Importance of Encryption in VNC Security
Encrypting VNC connections is essential to protect data transmitted between the local and remote machines from being intercepted or tampered with by malicious actors. Encryption ensures that even if data is intercepted, it remains unreadable without the appropriate decryption keys.
Read also:Peabody And Sherman Cast A Comprehensive Guide To The Voices Behind The Classic Adventures
Methods for Encrypting VNC Traffic
There are several methods to encrypt VNC traffic, including:
- SSL/TLS Encryption: Use SSL/TLS to secure VNC connections by encrypting data in transit.
- SSH Tunneling: Create an SSH tunnel to encapsulate VNC traffic within a secure encrypted connection.
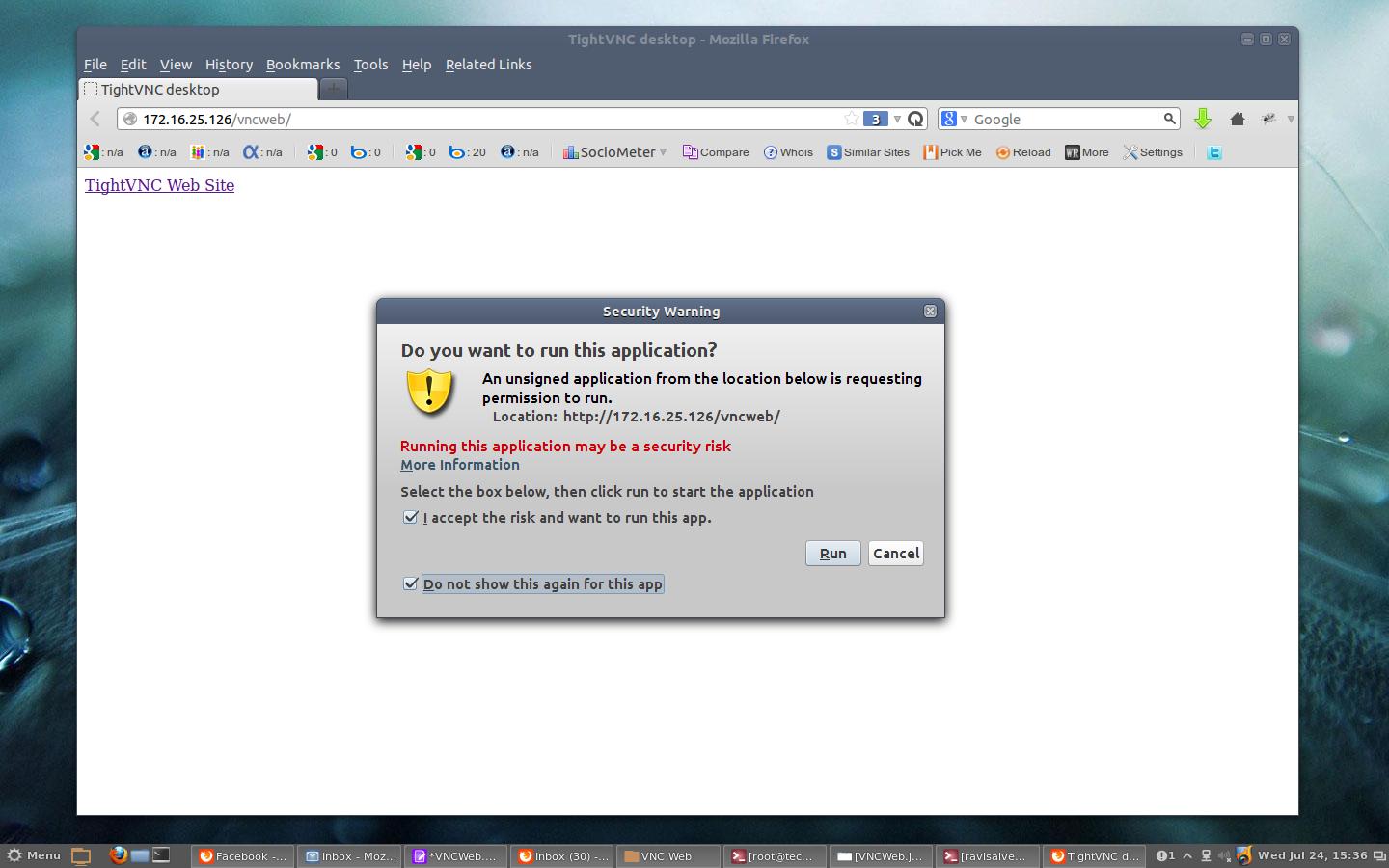
- VNC Software with Built-in Encryption: Choose VNC software that offers built-in encryption capabilities, such as TightVNC or RealVNC.
Configuring Firewall Rules for VNC
Why Firewall Configuration is Crucial
Properly configuring firewall rules is vital to securing VNC connections. Firewalls act as a barrier between your network and the outside world, controlling which traffic is allowed to pass through.
Steps to Configure Firewall for VNC
To configure your firewall for VNC, follow these steps:
- Identify the port used by your VNC server (default is usually 5900).
- Allow incoming connections only from trusted IP addresses or networks.
- Block all other incoming traffic to the VNC port to prevent unauthorized access.
- Regularly review and update firewall rules to adapt to changing security requirements.
Limiting Access to VNC
Restricting User Access
Limiting user access to VNC is an effective way to reduce the attack surface and enhance security. By controlling who can connect to your VNC server, you minimize the risk of unauthorized access and potential data breaches.
Methods for Limiting Access
Consider the following methods to restrict VNC access:
- Use access control lists (ACLs) to specify which users or groups are allowed to connect.
- Implement role-based access control (RBAC) to assign specific permissions to different users based on their roles.
- Disable VNC access for unnecessary users or systems to reduce the number of potential entry points for attackers.
Regularly Updating VNC Software
Why Updates Are Important
Regularly updating VNC software is crucial to maintaining security. Software updates often include patches for known vulnerabilities and improvements to enhance overall security and functionality.
How to Stay Up-to-Date
To ensure your VNC software remains secure, follow these steps:
- Enable automatic updates if available to ensure you receive the latest security patches.
- Regularly check for updates manually and install them promptly to address any security concerns.
- Subscribe to security bulletins or newsletters from VNC software vendors to stay informed about potential threats and updates.
Monitoring VNC Activity
Why Monitoring is Essential
Monitoring VNC activity helps detect and respond to suspicious or unauthorized access attempts, allowing you to take immediate action to protect your systems.
Tools and Techniques for Monitoring
Consider using the following tools and techniques to monitor VNC activity:
- Implement logging mechanisms to record all VNC connection attempts and activities.
- Use intrusion detection systems (IDS) to identify and alert you to potential security threats.
- Regularly review logs and reports to identify patterns or anomalies that may indicate unauthorized access.
Best Practices for Securing VNC
Comprehensive Security Measures
In addition to the specific strategies outlined above, adopting a holistic approach to VNC security can further enhance protection. Here are some best practices to consider:
- Use a strong, unique password for each VNC session to prevent credential reuse attacks.
- Disable unused or unnecessary VNC services to reduce the attack surface.
- Regularly back up important data to ensure recovery in case of a security breach.
- Conduct regular security audits and penetration testing to identify and address potential vulnerabilities.
Common Mistakes to Avoid
Identifying Security Pitfalls
Avoiding common mistakes can significantly improve VNC security. Some of the most frequent errors include:
- Using default passwords or leaving default settings unchanged.
- Failing to encrypt VNC connections, leaving data exposed to interception.
- Not regularly updating VNC software, leaving systems vulnerable to known exploits.
- Ignoring security alerts or logs, allowing potential threats to go unnoticed.
Conclusion
In conclusion, securing VNC connections is essential to protect sensitive data and maintain system integrity. By implementing strong authentication, encrypting connections, configuring firewalls, limiting access, and regularly updating software, you can significantly enhance the security of your VNC setup. Remember to monitor VNC activity and follow best practices to ensure ongoing protection.
We encourage you to take action by reviewing your current VNC configuration and implementing the strategies discussed in this guide. Share your thoughts and experiences in the comments below, and don't forget to explore other articles on our site for more cybersecurity tips and insights.
Table of Contents