In today's hyper-connected world, the Internet of Things (IoT) has become an integral part of our daily lives. From smart home devices to industrial sensors, IoT devices are revolutionizing how we interact with technology. However, managing and monitoring IoT devices behind Network Address Translation (NAT) presents unique challenges that need to be addressed to ensure optimal performance and security.
As the number of IoT devices continues to grow exponentially, organizations and individuals must adopt effective strategies to monitor IoT devices behind NAT. This is crucial not only for maintaining network efficiency but also for safeguarding sensitive data from potential cyber threats.
This article delves into the intricacies of monitoring IoT devices behind NAT, providing actionable insights and best practices to help you optimize your IoT network infrastructure. Whether you're a network administrator, IT professional, or tech enthusiast, this guide will equip you with the knowledge and tools necessary to manage IoT devices effectively.
Read also:Ages Of Housewives Of Beverly Hills A Comprehensive Look At The Cast
Table of Contents
- Introduction to IoT and NAT
- Challenges of Monitoring IoT Devices Behind NAT
- Tools for Monitoring IoT Devices Behind NAT
- Methods of Monitoring IoT Devices Behind NAT
- Security Considerations for IoT Devices Behind NAT
- Optimizing Network Performance
- Best Practices for Managing IoT Devices
- Real-World Examples of IoT Monitoring
- Future Trends in IoT Monitoring
- Conclusion and Call to Action
Introduction to IoT and NAT
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data. NAT, or Network Address Translation, is a method used to allow multiple devices to share a single public IP address, commonly employed in home and small business networks.
Understanding the relationship between IoT and NAT is essential for effective device management. When IoT devices are behind NAT, they may face connectivity issues, reduced performance, and increased security risks. This section explores the basics of IoT and NAT, laying the foundation for more advanced topics.
What is IoT?
IoT encompasses a wide range of devices, from wearable fitness trackers to industrial machinery. These devices are designed to collect and transmit data, often in real-time, enabling smarter decision-making and automation.
How Does NAT Work?
NAT allows multiple devices within a private network to access the internet using a single public IP address. It translates private IP addresses into a public IP address, ensuring seamless communication while maintaining network security.
Challenges of Monitoring IoT Devices Behind NAT
Monitoring IoT devices behind NAT presents several challenges that can hinder network performance and security. These challenges include limited visibility, potential data breaches, and difficulty in diagnosing issues.
Limited Visibility
When IoT devices are behind NAT, network administrators may struggle to gain a clear view of device activity. This lack of visibility can make it challenging to identify performance bottlenecks or security vulnerabilities.
Read also:Unveiling The Cast Of Jeepers Creepers A Deep Dive Into Horror Cinema
Data Security Risks
IoT devices behind NAT are susceptible to data breaches if not properly secured. Hackers can exploit vulnerabilities in these devices to gain unauthorized access to sensitive information, making security a top priority.
Diagnosis Difficulties
Identifying and resolving issues with IoT devices behind NAT can be time-consuming and complex. Without the right tools and strategies, diagnosing problems can become a significant challenge for network administrators.
Tools for Monitoring IoT Devices Behind NAT
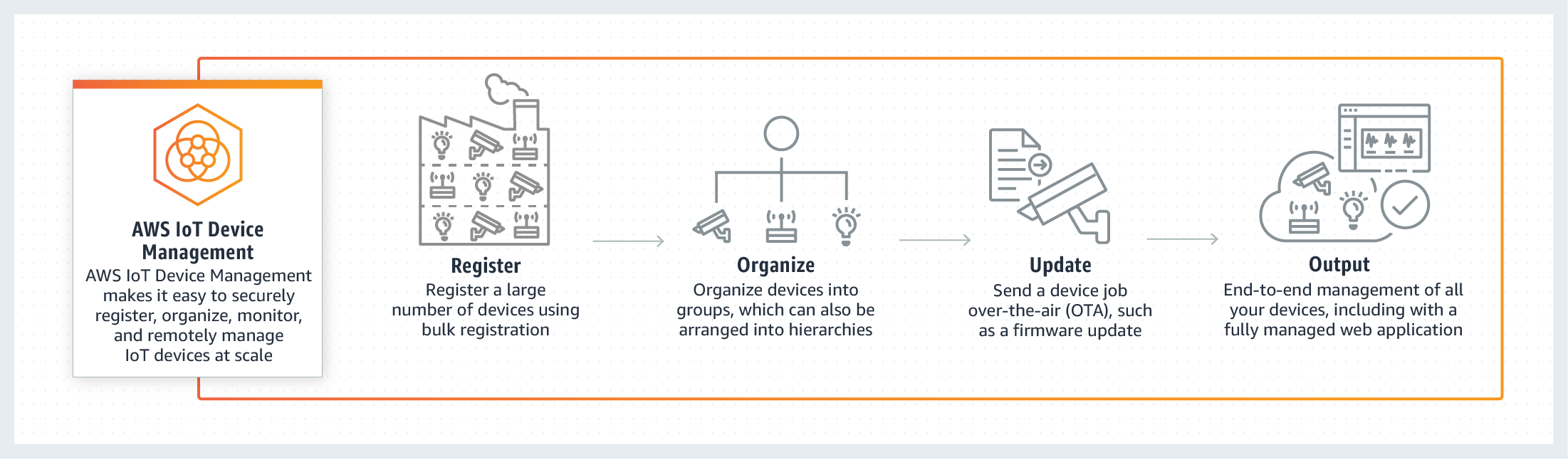
To effectively monitor IoT devices behind NAT, it's essential to utilize the right tools. These tools provide valuable insights into device performance, security, and connectivity, enabling administrators to maintain a healthy network environment.
Network Monitoring Software
- Wireshark: A powerful network protocol analyzer that captures and interacts with network packets.
- PRTG Network Monitor: A comprehensive monitoring solution that offers real-time insights into network performance.
- SolarWinds Network Performance Monitor: A robust tool designed to monitor and analyze network traffic and device activity.
IoT-Specific Tools
- DevicePilot: A platform dedicated to IoT device monitoring, offering advanced analytics and alerting features.
- Ubidots: A cloud-based IoT platform that provides tools for data visualization and device management.
Methods of Monitoring IoT Devices Behind NAT
Various methods can be employed to monitor IoT devices behind NAT, each with its own advantages and limitations. Understanding these methods is crucial for selecting the most appropriate approach for your network environment.
Port Forwarding
Port forwarding allows specific ports to be opened for IoT devices, enabling direct communication with external networks. While effective, this method can expose devices to potential security risks if not properly configured.
UPnP (Universal Plug and Play)
UPnP simplifies the process of connecting devices to a network by automatically configuring port mappings. However, UPnP can pose security risks if not securely implemented.
Tunneling
Tunneling involves encapsulating IoT device traffic within a secure connection, ensuring data privacy and integrity. This method is particularly useful for sensitive applications requiring high levels of security.
Security Considerations for IoT Devices Behind NAT
Security is a critical concern when monitoring IoT devices behind NAT. Implementing robust security measures is essential to protect sensitive data and prevent unauthorized access.
Encryption
Encrypting data transmitted between IoT devices and external networks ensures confidentiality and integrity. Protocols such as TLS (Transport Layer Security) and SSL (Secure Sockets Layer) are widely used for secure communication.
Firewall Configuration
Configuring firewalls to restrict unauthorized access to IoT devices is a vital security measure. Firewalls can be set up to allow only specific traffic, reducing the risk of cyberattacks.
Regular Updates
Keeping IoT devices and firmware up to date is crucial for addressing known vulnerabilities and ensuring optimal performance. Regular updates should be part of any IoT management strategy.
Optimizing Network Performance
Optimizing network performance is essential for ensuring seamless operation of IoT devices behind NAT. By implementing best practices, network administrators can enhance device connectivity and reduce latency.
Bandwidth Management
Efficiently managing bandwidth usage is key to maintaining network performance. Techniques such as Quality of Service (QoS) can prioritize critical traffic, ensuring optimal performance for IoT devices.
Load Balancing
Load balancing distributes network traffic across multiple devices, preventing overload and ensuring consistent performance. This technique is particularly useful in environments with numerous IoT devices.
Network Segmentation
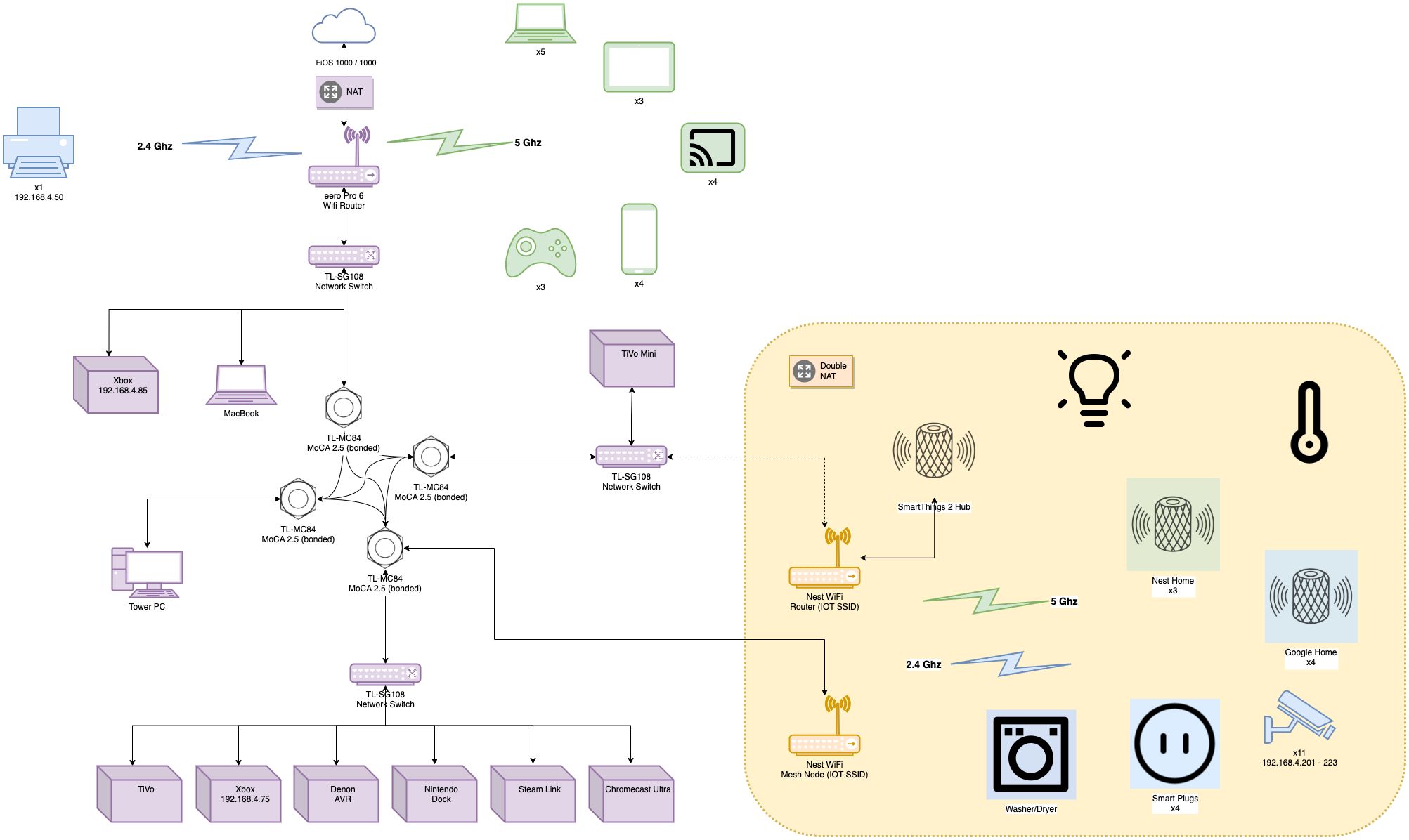
Segmenting networks to isolate IoT devices from other network components can improve security and performance. This approach minimizes the impact of potential security breaches and optimizes resource allocation.
Best Practices for Managing IoT Devices
Adopting best practices for managing IoT devices behind NAT is crucial for achieving optimal results. These practices encompass a wide range of strategies, from device configuration to ongoing maintenance.
Device Configuration
Configuring IoT devices correctly is the foundation of effective management. This includes setting up secure authentication methods, enabling encryption, and configuring network settings appropriately.
Ongoing Maintenance
Regular maintenance is essential for ensuring the continued performance and security of IoT devices. This includes monitoring device health, performing firmware updates, and addressing any issues promptly.
User Education
Educating users about IoT device management and security best practices is vital for maintaining a secure network environment. Providing training and resources can help users make informed decisions and avoid common pitfalls.
Real-World Examples of IoT Monitoring
Examining real-world examples of IoT monitoring provides valuable insights into practical applications and potential challenges. These examples highlight the importance of effective monitoring strategies in various industries.
Smart Home Applications
In smart home environments, monitoring IoT devices behind NAT ensures seamless operation of appliances, lighting, and security systems. Solutions such as smart thermostats and cameras rely on reliable connectivity and security measures.
Industrial IoT
Industrial IoT applications, such as manufacturing and logistics, require robust monitoring solutions to maintain operational efficiency. These systems often involve large-scale deployments of IoT devices, making effective management critical.
Future Trends in IoT Monitoring
The landscape of IoT monitoring is evolving rapidly, driven by advancements in technology and changing user demands. Staying informed about future trends is essential for adapting to new challenges and opportunities.
Artificial Intelligence and Machine Learning
AI and machine learning are transforming IoT monitoring by enabling predictive analytics and automated decision-making. These technologies can significantly enhance the efficiency and effectiveness of IoT device management.
5G and Edge Computing
The advent of 5G and edge computing is set to revolutionize IoT monitoring by providing faster connectivity and reduced latency. These technologies will enable more sophisticated applications and improve overall network performance.
Conclusion and Call to Action
Monitoring IoT devices behind NAT is a complex but essential task for maintaining network performance and security. By understanding the challenges, utilizing the right tools, and adopting best practices, network administrators can effectively manage IoT devices and ensure optimal results.
We encourage readers to share their thoughts and experiences in the comments section below. Additionally, exploring related articles on our website can provide further insights into IoT management and networking. Together, we can build a safer and more connected future.
References:
- Wireshark Official Documentation: https://www.wireshark.org/docs/
- SolarWinds Network Performance Monitor: https://www.solarwinds.com/network-performance-monitor
- DevicePilot Platform: https://www.devicepilot.com/