In today's interconnected world, IoT (Internet of Things) devices have become integral to our daily lives. Accessing these devices securely is crucial, especially when using SSH (Secure Shell) as a protocol. Whether you're managing smart home devices, industrial sensors, or remote servers, understanding how to access IoT devices via SSH is essential for maintaining security and efficiency.
SSH provides a secure channel for communication between devices over an unsecured network. By leveraging SSH, users can remotely manage IoT devices with confidence, knowing their data remains encrypted and protected from unauthorized access. This article will delve into practical examples and methods for accessing IoT devices using SSH, offering step-by-step instructions and valuable tips.
Whether you're a beginner or an experienced IT professional, this guide will provide you with the knowledge and tools necessary to establish secure connections with your IoT devices. Let's explore the nuances of IoT device SSH access and learn how to implement it effectively in various scenarios.
Read also:Charles Alden Black Jr The Extraordinary Life And Legacy Of A Remarkable Figure
Table of Contents
- Introduction to SSH and Its Importance in IoT
- Overview of IoT Devices and Their Security Needs
- Basic SSH Setup for IoT Devices
- Step-by-Step Guide to Access IoT Device via SSH
- Using SSH Key Authentication for Enhanced Security
- Common SSH Commands for IoT Device Management
- Troubleshooting Common SSH Connection Issues
- Best Practices for Secure SSH Access
- Real-World Examples of IoT SSH Implementation
- Conclusion and Next Steps
Introduction to SSH and Its Importance in IoT
SSH, or Secure Shell, is a cryptographic network protocol used to establish secure connections between devices over unsecured networks. In the context of IoT, SSH plays a pivotal role in ensuring that remote access to devices remains protected against unauthorized access and cyber threats.
As IoT devices continue to proliferate across industries, the need for secure communication channels has never been more critical. SSH not only encrypts data transmitted between devices but also authenticates users and systems, preventing unauthorized access. This makes it an ideal choice for managing IoT devices remotely.
Why SSH is Preferred for IoT Devices
- Encryption of data during transmission
- Authentication mechanisms to verify user identity
- Support for secure file transfers via SCP and SFTP
- Compatibility with a wide range of operating systems and platforms
By utilizing SSH, organizations and individuals can confidently manage their IoT devices without compromising security or performance. In the following sections, we'll explore how to set up and access IoT devices using SSH, along with best practices for maintaining secure connections.
Overview of IoT Devices and Their Security Needs
IoT devices encompass a wide range of technologies, from smart home appliances to industrial sensors and medical devices. Each type of IoT device presents unique security challenges that must be addressed to ensure safe and reliable operation.
Common security concerns for IoT devices include unauthorized access, data breaches, and malicious attacks. Implementing SSH as a standard protocol for remote access helps mitigate these risks by providing a secure and encrypted communication channel.
Read also:Shatrughan Sinha Age A Comprehensive Look At The Iconic Bollywood Star
Types of IoT Devices
- Smart home devices (e.g., thermostats, lighting systems)
- Industrial IoT sensors and controllers
- Medical devices for remote patient monitoring
- Agricultural IoT systems for crop management
Understanding the specific requirements of each IoT device type is essential for tailoring SSH configurations to meet their unique needs. In the next section, we'll discuss how to set up SSH on IoT devices, providing a solid foundation for secure remote access.
Basic SSH Setup for IoT Devices
Setting up SSH on an IoT device involves several key steps, including enabling the SSH server, configuring firewall settings, and securing the connection with strong authentication methods. Below, we'll walk through the basic setup process to get your IoT device ready for remote access.
Enabling SSH on IoT Devices
The process for enabling SSH varies depending on the operating system and firmware of your IoT device. For devices running Linux-based systems, such as Raspberry Pi or similar single-board computers, the following steps can be used:
- Log in to your IoT device via a local terminal or console.
- Run the command
sudo systemctl enable sshto enable the SSH service. - Start the SSH service using
sudo systemctl start ssh. - Verify that SSH is running with
sudo systemctl status ssh.
For devices with proprietary firmware, consult the manufacturer's documentation for specific instructions on enabling SSH.
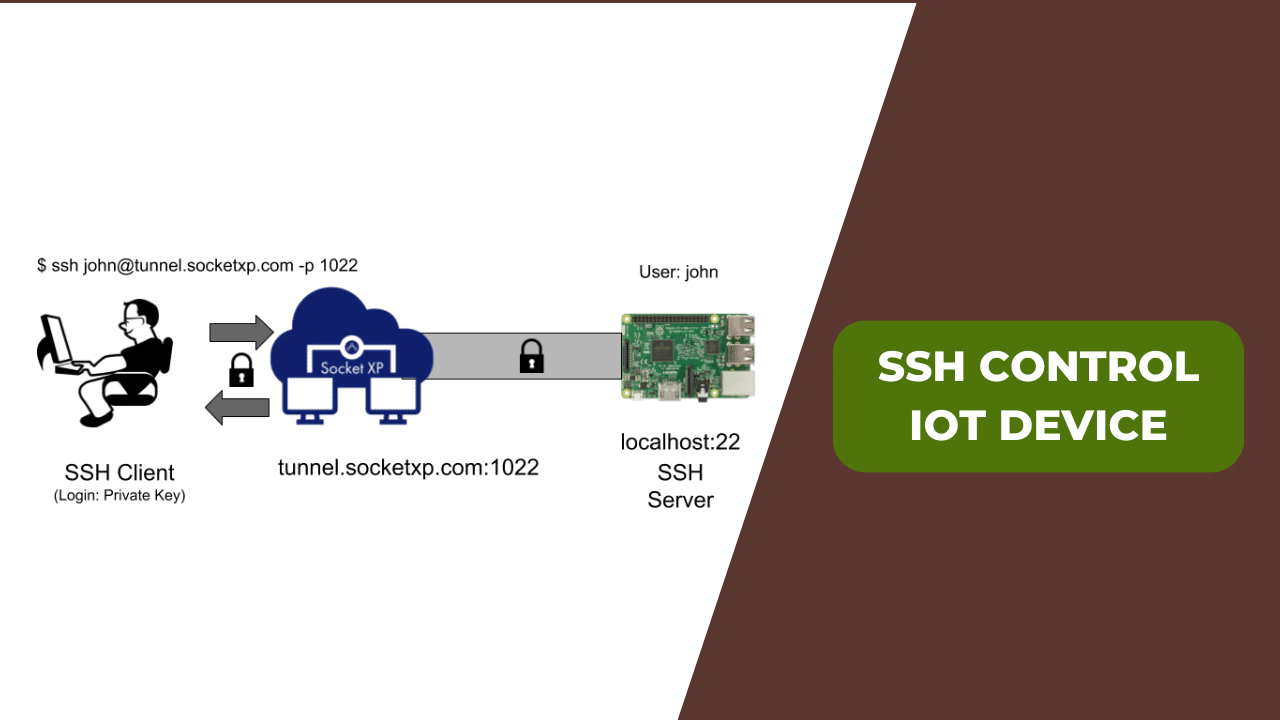
Step-by-Step Guide to Access IoT Device via SSH
Once SSH is enabled on your IoT device, you can establish a remote connection using a variety of SSH clients. Below is a step-by-step guide to accessing your IoT device via SSH:
Using SSH from a Terminal
- Open a terminal on your local machine.
- Enter the command
ssh username@ip_address, replacing "username" with your IoT device's login credentials and "ip_address" with the device's IP address. - When prompted, enter the password for the specified user account.
- You are now connected to your IoT device and can execute commands remotely.
Connecting with an SSH Client
If you prefer a graphical interface, tools like PuTTY (for Windows) or MobaXterm can be used to establish SSH connections. Simply configure the client with the appropriate IP address, port number (usually 22), and authentication details.
Using SSH Key Authentication for Enhanced Security
While password-based authentication is convenient, it can be vulnerable to brute-force attacks. To enhance security, consider using SSH key authentication, which relies on cryptographic key pairs for verification.
Generating SSH Keys
- Open a terminal and run the command
ssh-keygen. - Follow the prompts to specify a file location and passphrase for your private key.
- This process will generate a public-private key pair, typically stored in the
~/.ssh/directory.
Configuring Key-Based Authentication
- Copy the public key to your IoT device using the command
ssh-copy-id username@ip_address. - Test the connection by attempting to log in via SSH without entering a password.
- If successful, disable password authentication on your IoT device to further enhance security.
Common SSH Commands for IoT Device Management
Once connected to your IoT device via SSH, you can execute a variety of commands to manage and monitor the system. Below are some commonly used SSH commands for IoT device management:
ls: List files and directories in the current location.cd: Change the current working directory.sudo: Execute commands with administrative privileges.top: Display real-time system resource usage.ping: Test network connectivity to other devices.
Mastering these commands will empower you to efficiently manage your IoT devices from anywhere in the world.
Troubleshooting Common SSH Connection Issues
Despite its robustness, SSH connections can sometimes encounter issues. Below are some common problems and their solutions:
Connection Refused Errors
If you receive a "Connection refused" error, ensure that:
- The SSH service is running on the IoT device.
- Firewall rules allow traffic on port 22 (or the custom port you're using).
- The IP address and port number are correctly specified in the SSH client.
Authentication Failures
Authentication failures can occur due to incorrect credentials or misconfigured key-based authentication. Verify that:
- The username and password match those on the IoT device.
- The public key has been properly copied to the device's authorized_keys file.
- File permissions for the SSH configuration files are correctly set.
Best Practices for Secure SSH Access
To ensure the highest level of security when accessing IoT devices via SSH, follow these best practices:
- Use strong, unique passwords or cryptographic keys for authentication.
- Disable password authentication and rely solely on key-based methods.
- Change the default SSH port (22) to a non-standard port to reduce automated attack attempts.
- Implement firewall rules to restrict access to trusted IP addresses.
- Regularly update the firmware and operating system of your IoT devices to patch known vulnerabilities.
By adhering to these guidelines, you can significantly reduce the risk of unauthorized access and protect your IoT devices from potential threats.
Real-World Examples of IoT SSH Implementation
Organizations across various industries are leveraging SSH to securely manage their IoT devices. Below are some real-world examples of SSH implementation in IoT:
Smart Agriculture
Farmers use SSH to remotely monitor and control irrigation systems, ensuring optimal water usage and crop health. By connecting to IoT sensors via SSH, they can retrieve real-time data on soil moisture levels and adjust settings as needed.
Industrial Automation
In manufacturing facilities, SSH enables engineers to securely access and configure IoT devices responsible for monitoring production lines. This ensures smooth operations and minimizes downtime caused by equipment malfunctions.
Conclusion and Next Steps
In conclusion, accessing IoT devices via SSH provides a secure and reliable method for remote management. By following the steps outlined in this guide, you can establish secure connections to your IoT devices and implement best practices to protect against potential threats.
We encourage you to share this article with others who may benefit from its insights and leave a comment below with any questions or feedback. For further reading, explore our other articles on IoT security and best practices for maintaining robust network defenses.